Category: Reverse Engineering
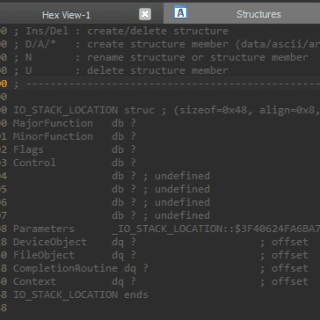
Driver Buddy Reloaded Driver Buddy Reloaded is an IDA Pro Python plugin that helps automate some tedious Windows Kernel Drivers reverse engineering tasks. It has a number of handy features, such as: Identifying the type...
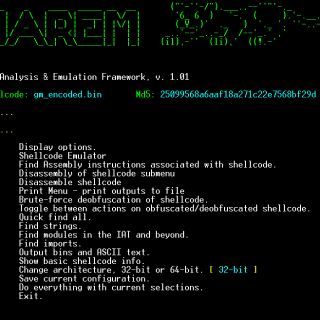
sharem SHAREM is intended to be the ultimate Windows shellcode tool, with support to emulate over 12,000 WinAPIs, virtually all user-mode Windows syscalls, and SHAREM provides numerous new features. SHAREM was released on September...
DotDumper An automatic unpacker and logger for DotNet Framework targeting files! This tool has been unveiled at Black Hat USA 2022. The automatic detection and classification of any given file in a reliable manner is...
OFRAK OFRAK (Open Firmware Reverse Analysis Konsole) is a binary analysis and modification platform. OFRAK combines the ability to: Identify and Unpack many binary formats Analyze unpacked binaries with field-tested reverse engineering tools Modify and Repack binaries with powerful patching strategies...
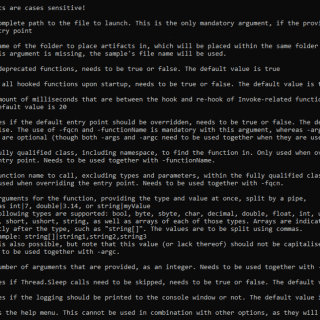
Fuzzable Framework for Automating Fuzzable Target Discovery with Static Analysis Vulnerability researchers conducting security assessments on software will often harness the capabilities of coverage-guided fuzzing through powerful tools like AFL++ and libFuzzer. This is important as...
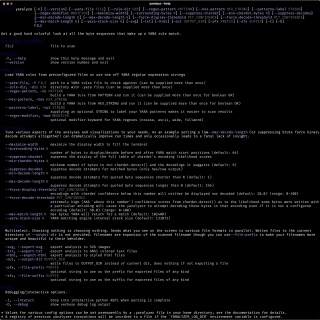
THE YARALYZER Visually inspect all of the regex matches (and their sexier, more cloak-and-dagger cousins, the YARA matches) found in binary data and/or text. See what happens when you force various character encodings upon those...
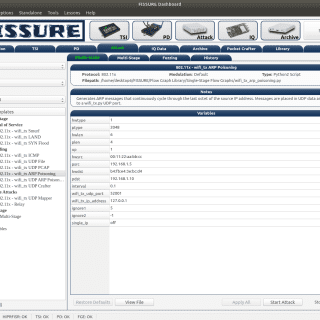
FISSURE – The RF Framework Frequency Independent SDR-based Signal Understanding and Reverse Engineering FISSURE is an open-source RF and reverses engineering framework designed for all skill levels with hooks for signal detection and classification,...
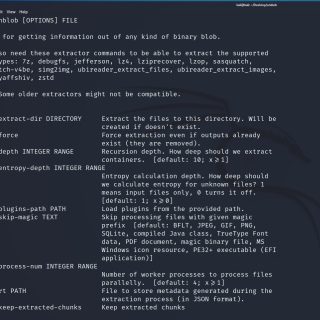
unblob unblob is a tool for getting information out of any kind of binary blob. Extractors Unblob relies on various tools for extracting the contents of a blob. These extractors are either third-party tools...
reFlutter This framework helps with Flutter apps reverse engineering using the patched version of the Flutter library which is already compiled and ready for app repacking. This library has a snapshot deserialization process modified...
Get-PDInvokeImports Get-PDInvokeImports is a tool (PowerShell module) which is able to perform automatic detection of P/Invoke, Dynamic P/Invoke, and D/Invoke usage in assembly. Showing all locations from where they are referenced and Exports all...
What is BinAbsInspector? BinAbsInspector (Binary Abstract Inspector) is a static analyzer for automated reverse engineering and scanning vulnerabilities in binaries, which is a long-term research project incubated at Keenlab. It is based on abstract interpretation...
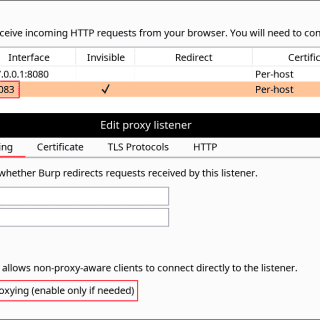
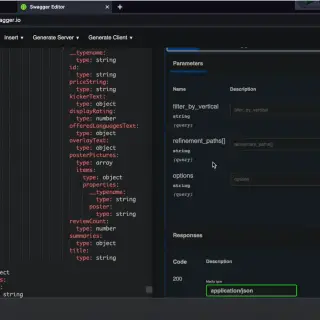
mitmproxy2swagger A tool for automatically converting mitmproxy captures to OpenAPI 3.0 specifications. This means that you can automatically reverse-engineer REST APIs by just running the apps and capturing the traffic. Install First, you will need python3 and pip3....
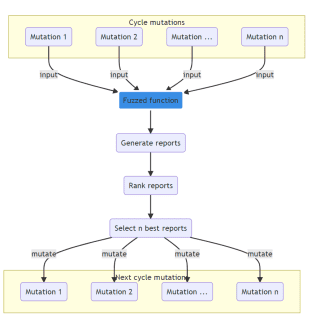
Frelatage Frelatage is a coverage-based Python fuzzing library which can be used to fuzz python code. The development of Frelatage was inspired by various other fuzzers, including AFL/AFL++, Atheris, and PythonFuzz. The main purpose of the project is...
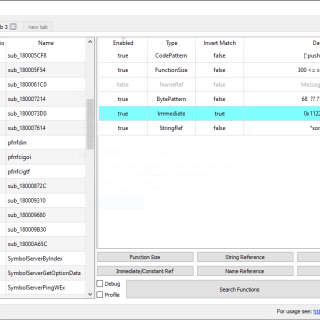
FindFunc: Advanced Filtering/Finding of Functions in IDA PRO FindFunc is an IDA PRO plugin to find code functions that contain a certain assembly or byte pattern, reference a certain name or string, or conform...
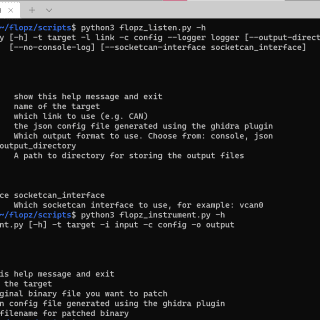
Flopz – Firmware Liberation on Python Flopz is an assembler toolkit written in pure python. Use it to: Create shellcode for embedded systems Dynamically patch large collections of binaries Instrument firmware images, for debugging...