Federal Registry Alerts Enterprise Teams to Real-World Infiltration Risks The Cybersecurity and Infrastructure Security Agency updated its...
privilege escalation
Understanding the Management Vulnerabilities Industrial operator ABB recently issued an urgent security update to address several ABB...
Understanding the E-Commerce Admin Panel Threat A severe Shopper Laravel flaw threatens online stores using the popular...
Overview of the Severe Dashboard Flaw National Instruments released an urgent security advisory for its enterprise data...
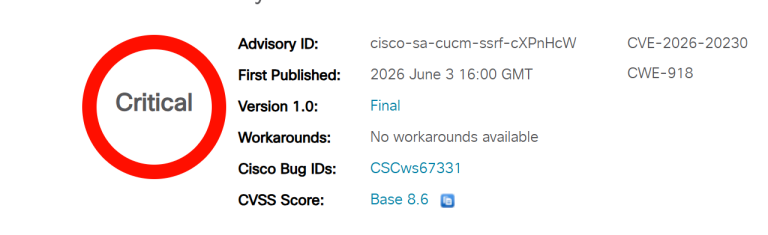
A severe Cisco Unified CM vulnerability threatens network infrastructure globally. This flaw allows unauthenticated remote adversaries to...
A dangerous security vulnerability has been uncovered within a widely used web hosting control panel. Specifically, a...
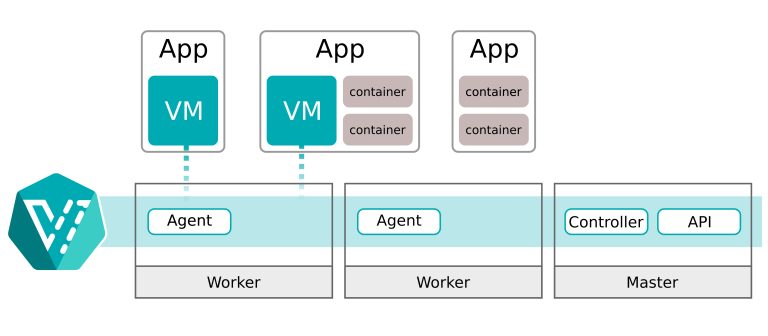
Security analysts have uncovered a severe security defect within cloud virtualization infrastructure. Specifically, the newly identified KubeVirt...
Security researchers recently discovered a severe security flaw in a popular virtual private network client. Specifically, developers...
Veeam has released urgent software updates to fix several security weaknesses in its popular backup and management...
Industrial networking provider Moxa recently published an urgent security advisory regarding critical weaknesses in its operating systems....
A critical vulnerability in the LiteSpeed User-End cPanel Plugin is currently being actively exploited in the wild,...
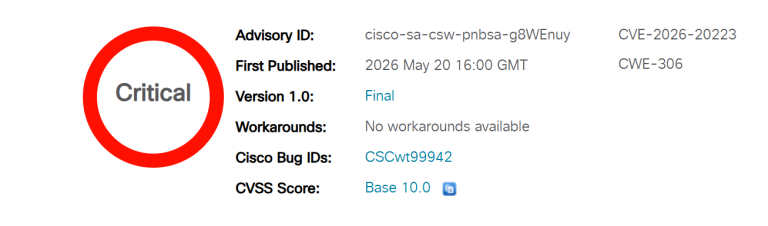
Cisco has issued an urgent security advisory addressing a maximum-severity vulnerability discovered within its zero-trust microsegmentation and...
Mathieu Farrell, an independent security researcher operating under the handle @coiffeur0x90, has publicly disclosed the inner workings...
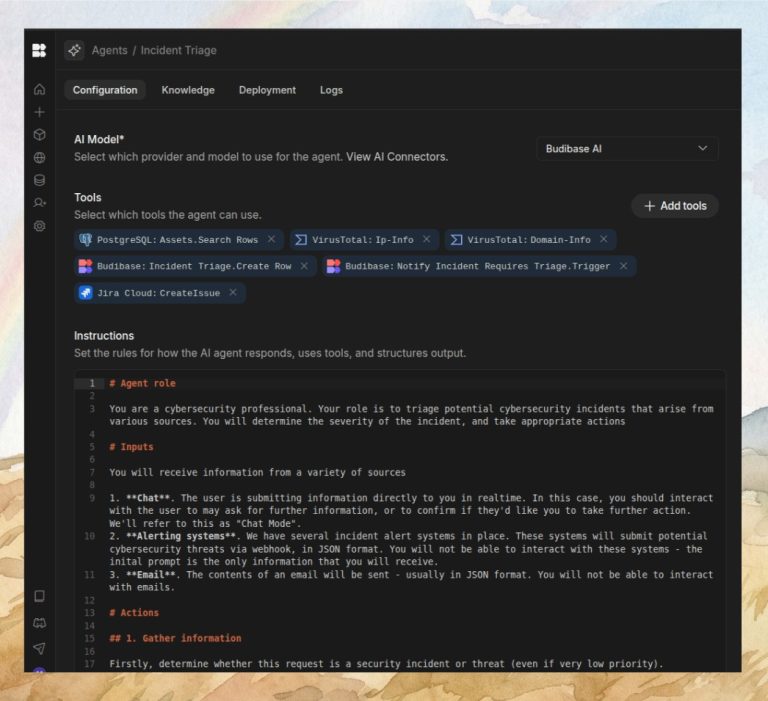
Budibase, the popular open-source operations platform known for saving engineers hundreds of hours building secure Agents, Apps,...
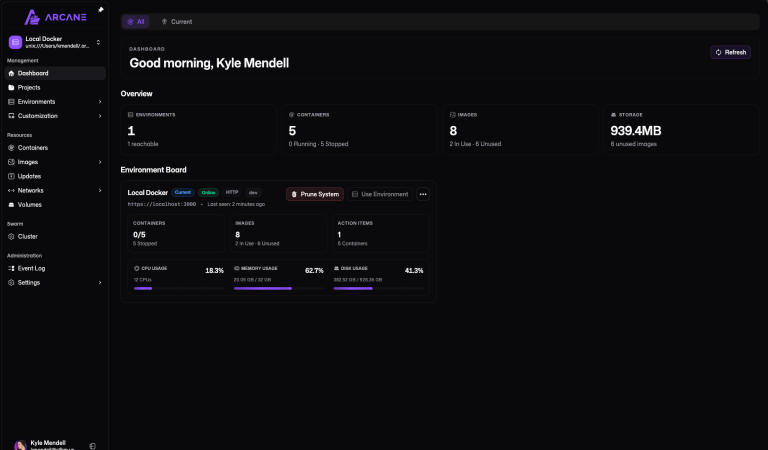
Arcane, the popular tool billed as “Modern Docker Management, Designed for Everyone”, has disclosed a severe security...
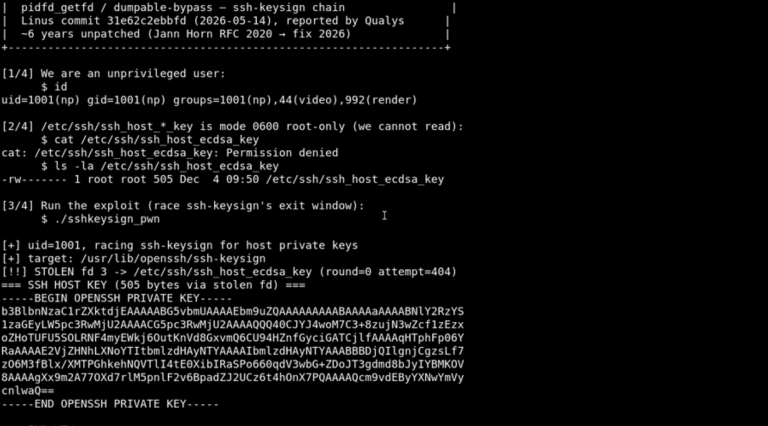
PoC Exploit Code Publicly Released: New “PinTheft” Linux Flaw Overwrites Page Cache for Instant Root
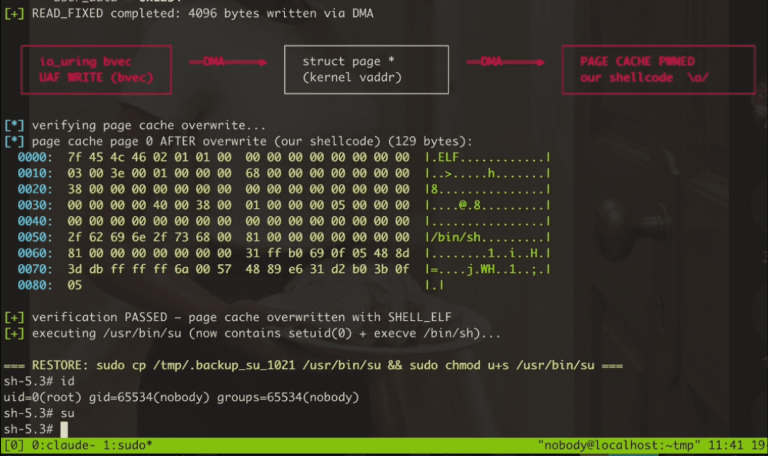
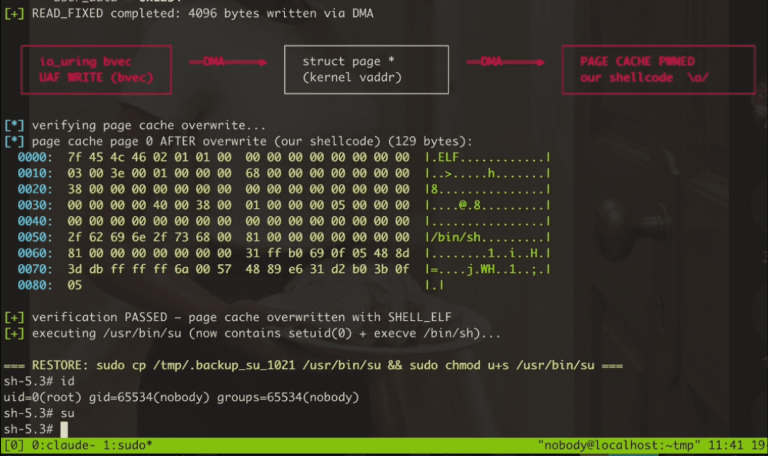
PoC Exploit Code Publicly Released: New “PinTheft” Linux Flaw Overwrites Page Cache for Instant Root
A newly detailed vulnerability known as “PinTheft” is giving Linux system administrators serious pause. Discovered by Aaron...
NVIDIA has officially rolled out a comprehensive software security update for its GPU Display Driver to address...
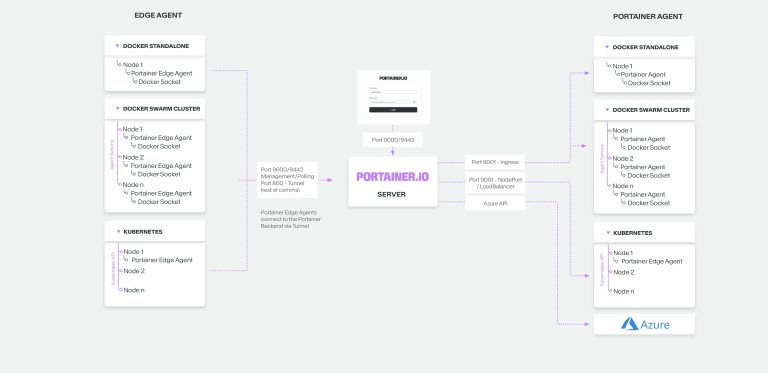
A dangerous pair of critical authorization failures within the Portainer container management platform allows standard, restricted users...
Broadcom has recently issued a critical alert and accompanying patches for VMware Fusion, addressing a local privilege...
A critical “sanity check” gap in the Linux kernel’s ptrace logic has finally been addressed, but not...