BARF v0.6 releases: open source Binary Analysis & Reverse engineering Framework
BARF: Binary Analysis and Reverse engineering Framework
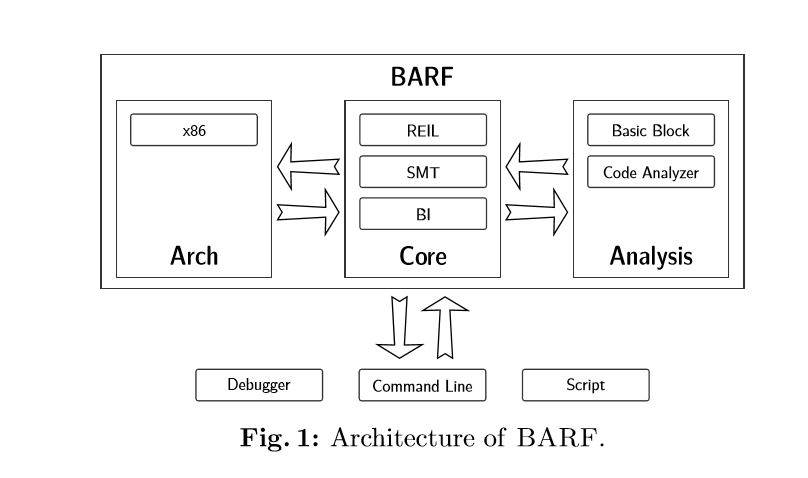
The analysis of binary code is a crucial activity in many areas of the computer sciences and software engineering disciplines ranging from software security and program analysis to reverse engineering. Manual binary analysis is a difficult and time-consuming task and there are software tools that seek to automate or assist human analysts. However, most of these tools have several technical and commercial restrictions that limit access and use by a large portion of the academic and practitioner communities. BARF is an open-source binary analysis framework that aims to support a wide range of binary code analysis tasks that are common in the information security discipline. It is a scriptable platform that supports instruction lifting from multiple architectures, binary translation to an intermediate representation, an extensible framework for code analysis plugins and interoperation with external tools such as debuggers, SMT solvers, and instrumentation tools. The framework is designed primarily for human-assisted analysis but it can be fully automated.
The BARF project includes BARF and related tools and packages. So far the project is composed of the following items:
- BARF: A multiplatform open-source Binary Analysis and Reverse engineering Framework
- PyAsmJIT: A JIT for the Intel x86_64 and ARM architecture.
- Tools built upon BARF:
- BARFgadgets: Lets you search, classify and verify ROP gadgets inside a binary program.
- BARFcfg: Lets you recover the control-flow graph of the functions of a binary program.
- BARFcg: Lets you recover the call graph of the functions of a binary program.
For more information, see:
- BARF: A multiplatform open-source Binary Analysis and Reverse engineering Framework (Whitepaper) [en]
- BARFing Gadgets (ekoparty2014 presentation)
BARF
BARF is a Python package for binary analysis and reverse engineering. It can:
- Load binary programs in different formats (
ELF,PE, etc), - It supports the Intel x86 architecture for 32 and 64 bits,
- It supports the ARM architecture for 32 bits,
- It operates on an intermediate language (REIL) thus all analysis algorithm are architecture-agnostic,
- It has integration with Z3 and CVC4 SMT solvers which means that you can express fragments of code as formulae and check restrictions on them.
Changelog v0.6
Added
- Add Python 3 compatibility.
- Add classes for managing call conventions.
- Add hook support to the
Emulatorclass. - Add
cconv(calling convention) module. - Add
ReilCputests. - Add
replaytool to replay x86 execution traces. - Add
x86.tracemodule. - Add
x86.helpermodule. - Add kao’s toy project solution to the
examplesfolder. - Add flare-on 2015 challenge #2 solution to the
examplesfolder. - Add basic symbolic execution support.
- Add extra methods to
ReilSequenceandReilContainerclasses. - Improve hook support of the
Emulatorclass. - Add support for
SHLDinstruction.
Changed
- Refactor ARM package.
- Refactor ARM tests.
- Refactor x86 package.
- Refactor x86 tests.
- Improve
emulate-binaryexample script. - Refactor
ReilBuilderclass. - Refactor instruction translators (both Intel and ARM). Group translators by category and create a module for each one.
- Improve
Emulatorclass. - Refactor
ReilCputests. - Rename
bimodule tobinary. - Refactor
Disassemblerclass. - Refactor
ReilEmulatorTainterclass. - Refactor
ReilCpuclass. - Refactor
reil.helpersmodule. - Refactor
ReilContainerclass. - Refactor
ReilBuilderclass. - Refactor
reil.taintermodule. - Refactor
ReilCpuclass. - Refactor
reil.parsertest module. - Refactor
reil.emulatortest module. - Rename
basicblockpackage (and tests) tographs. - Rename
gadgetpackage (and tests) togadgets. - Rename
reilparsermodule toreil.parser. - Refactor
reilemulatormodule. Split module into submodules:emulator.cpu,emulator.emulator,emulator.memory, andemulator.tainter. - Refactor
arch.emulatormodule.
Removed
- Remove
DualInstructionclass.
Fixed
- Fix
RSBARM instruction. - Fix control-flow graph rendering.
- Fix
SHRDtranslation. - Fix size of effective address calculation for Intel architecture.
- Fix
SHLandSHRinstruction translator.
Installation
BARF depends on the following SMT solvers:
- Z3 : A high-performance theorem prover being developed at Microsoft Research.
- CVC4 : An efficient open-source automatic theorem prover for satisfiability modulo theories (SMT) problems.
The following command installs BARF on your system:
Usage
More info, visit here.
Copyright (c) 2014, Fundación Dr. Manuel Sadosky
All rights reserved.






