bettercap v2.32 releases: Swiss army knife for network attacks and monitoring
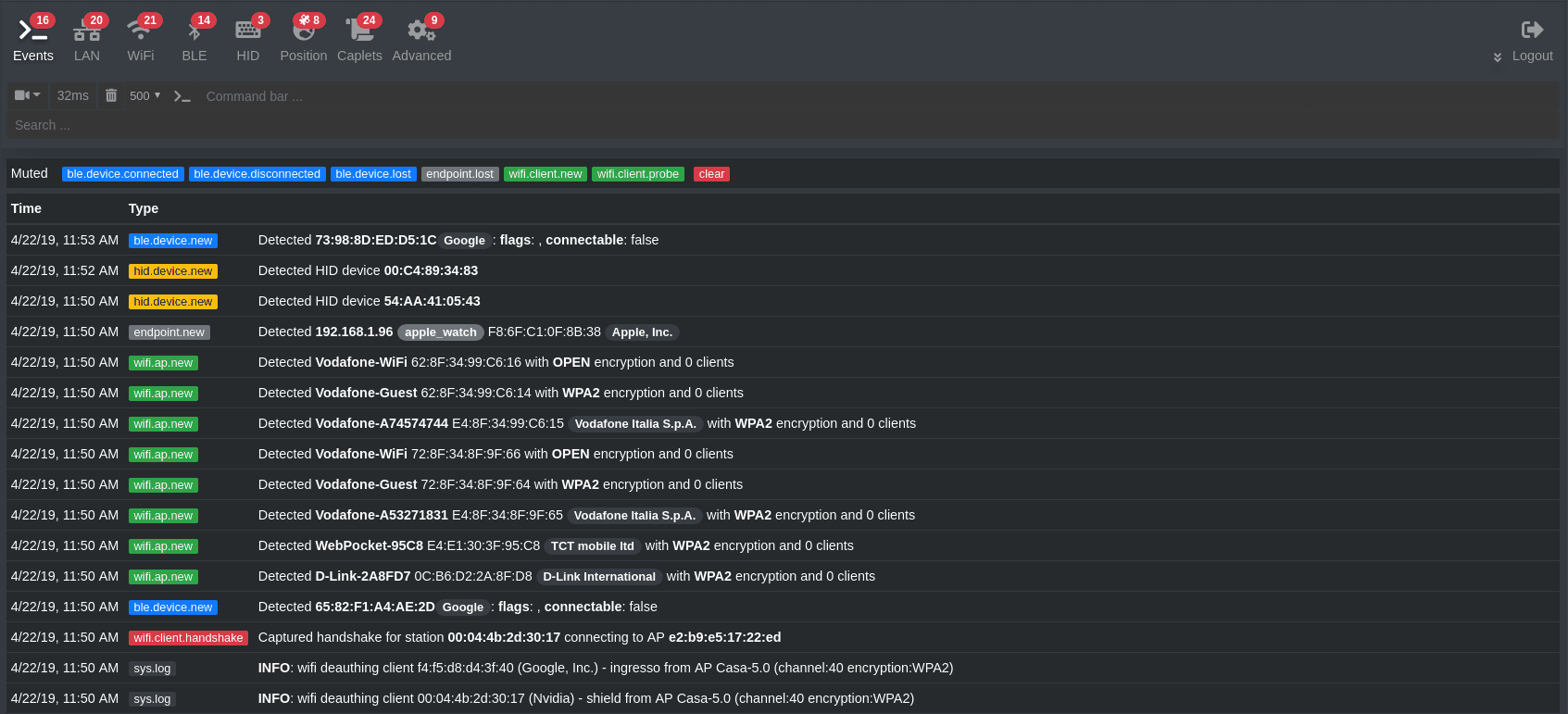
bettercap is a powerful, easily extensible, and portable framework written in Go which aims to offer to security researchers, red teamers and reverse engineers an easy to use, all-in-one solution with all the features they might possibly need for performing reconnaissance and attacking WiFi networks, Bluetooth Low Energy devices, wireless HID devices and Ethernet networks.
Main Features
- WiFi networks scanning, deauthentication attack, clientless PMKID association attack, and automatic WPA/WPA2 client handshakes capture.
- Bluetooth Low Energy devices scanning, characteristics enumeration, reading, and writing.
- 2.4Ghz wireless devices scanning and MouseJacking attacks with over-the-air HID frames injection (with DuckyScript support).
- Passive and active IP network hosts probing and recon.
- ARP, DNS and DHCPv6 spoofers for MITM attacks on IP based networks.
- Proxies at a packet level, TCP level and HTTP/HTTPS application-level fully scriptable with easy to implement javascript plugins.
- A powerful network sniffer for credentials harvesting which can also be used as a network protocol fuzzer.
- A very fast port scanner.
- A powerful REST API with support for asynchronous events notification on websocket to orchestrate your attacks easily.
- A very convenient web UI.
- More!
Bettercap v2.32 released.
Changelog
New Features
- 81ae731 new: new -pcap-buf-size option to set a custom pcap buffer size (closes #896)
- 59dce4c new: centralized pcap capture configuration management
- d0ecfd4 new: updated to go 1.16
- ef2cd00 add wifi fake authentication attack
- c8ecaf9 add channel hopping attack
- 58f4214 added Windows basepath to UI setup
Fixes
- d7f95dc Various changes and fixes
- 0637451 Fix arp.spoof not sending replies
- 6c2c0da fix: checking boundaries when parsing WPS vendor extensions (fixes #885)
- 9404620 Support for ch177
- daf2f94 Further tests for mapping dot11 frequencies to channels as ch177 was not discovered correctly based on freq
Misc
- c78a67d Add DESTDIR variable
- e9dad78 nothing but import format change
- 9020c53 make import statement clean
Download & Tutorial
Copyright (C) 2018 Simone Margaritelli
Source: https://github.com/evilsocket/