dirsearch v0.4.3 releases: Web path scanner
dirsearch
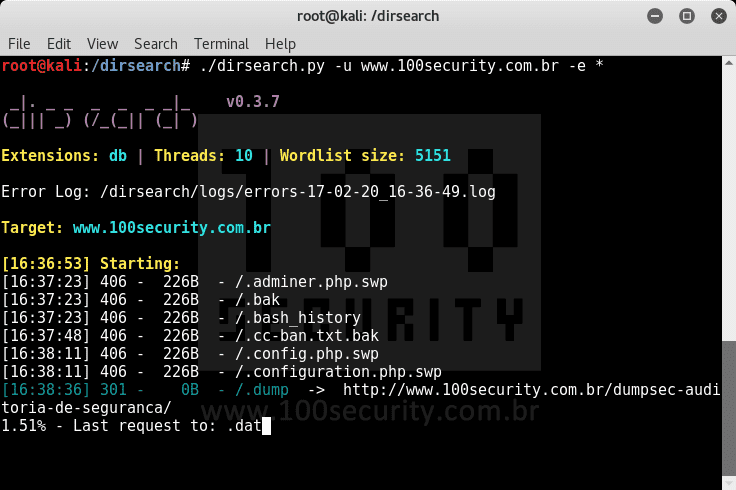
An advanced command-line tool designed to brute force directories and files in webservers, AKA web path scanner
Features
- Multithreaded
- Keep-alive connections
- Support for multiple extensions (-e|–extensions asp,php)
- Reporting (plain text, JSON)
- Heuristically detects invalid web pages
- Recursive brute forcing
- HTTP proxy support
- User-agent randomization
- Batch processing
- Request delaying
Changelog v0.43
- Automatically detect the URI scheme (
httporhttps) if no scheme is provided - SQLite report format
- Option to overwrite unwanted extensions with selected extensions
- Option to view redirects history when following redirects
- Option to crawl web paths in the responses
- HTTP traffic is saved inside log file
- Capability to save progress and resume later
- Support client certificate
- Maximum size of the log file via configuration
Download
git clone https://github.com/maurosoria/dirsearch.git
cd dirsearch
pip3 install -r requirements.txt
About wordlists
Summary:
- Wordlist is a text file, each line is a path.
- About extensions, unlike other tools, dirsearch only replaces the
%EXT%keyword with extensions from -e flag. - For wordlists without
%EXT%(like SecLists), -f | –force-extensions switch is required to append extensions to every word in wordlist, as well as the/. - To use multiple wordlists, you can separate your wordlists with commas. Example: wordlist1.txt,wordlist2.txt.
Dictionaries must be text files. Each line will be processed as such, except that the special word %EXT% is used, which will generate one entry for each extension (-e | –extension) passed as an argument.
Example:
- example/
- example.%EXT%
Passing the extensions “asp” and “aspx” will generate the following dictionary:
- example/
- example.asp
- example.aspx
You can also use -f | –force-extensions switch to append extensions to every word in the wordlists (like DirBuster).
Copyright (C) Mauro Soria (maurosoria@gmail.com)
Source: https://github.com/maurosoria/






