EXOCET-AV-Evasion: AV-evading, undetectable, payload delivery tool
EXOCET – AV-evading, undetectable, payload delivery tool
EXOCET is superior to Metasploit’s “Evasive Payloads” modules as EXOCET uses AES-256 in GCM Mode (Galois/Counter Mode). Metasploit’s Evasion Payloads uses an easy to detect RC4 encryption. While RC4 can decrypt faster, AES-256 is much more difficult to ascertain the intent of the malware.
However, it is possible to use Metasploit to build an Evasive Payload, and then chain that with EXOCET. So EXOCET will decrypt via AES-256, and then the Metasploit Evasive Payload then decrypts itself from RC4.
Much like my previous project, Dark Lord Obama Project, this toolkit is designed to be a delivery/launch vehicle, much like Veil-Evasion does.
However, EXOCET is not limited to a single codebase or platforms that are running Python. EXOCET works on ALL supported platforms and architectures that Go supports.
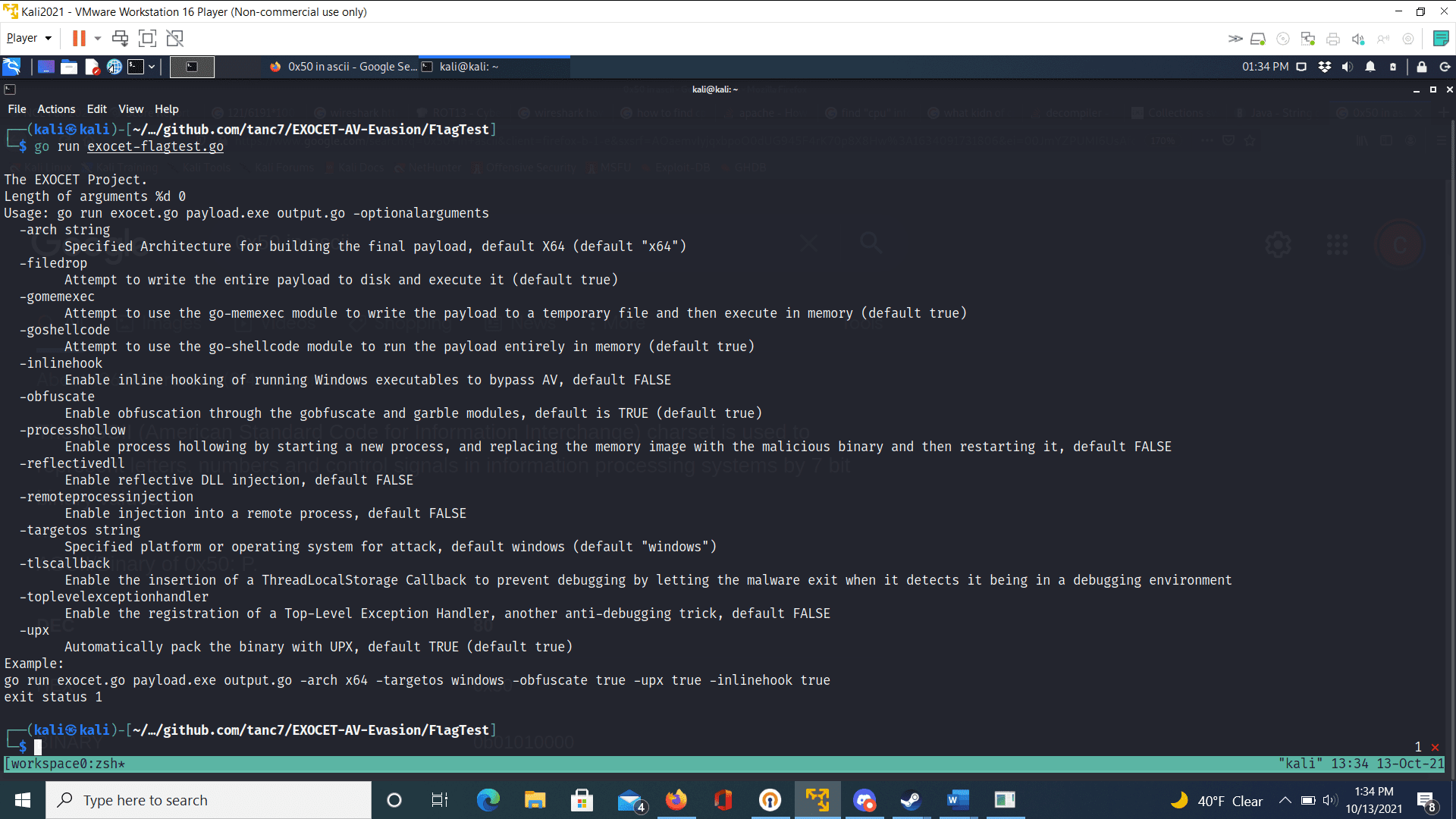
Exocet Overview
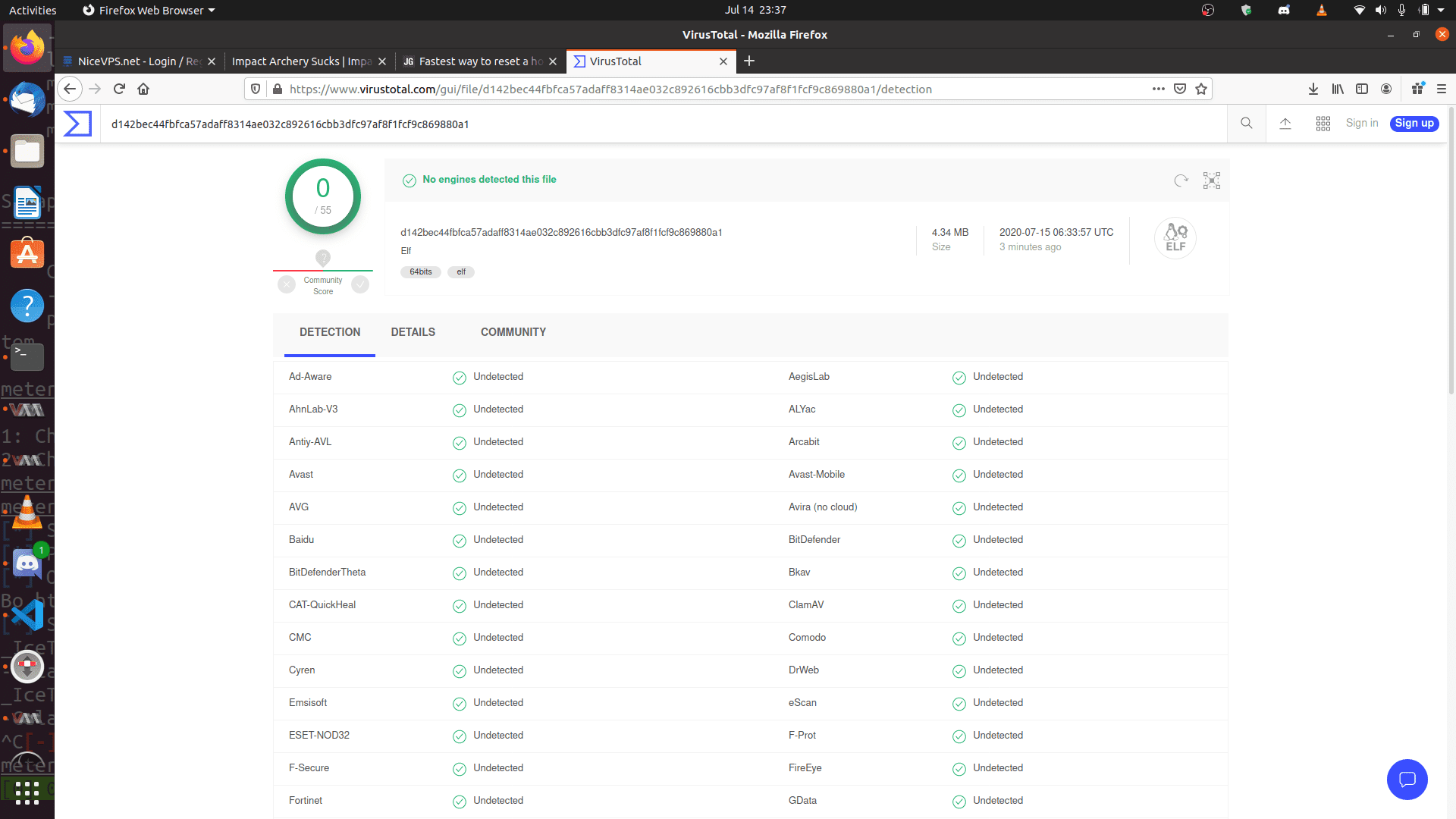
EXOCET is effectively a crypter-type malware dropper that can recycle easily detectable payloads like WannaCry, encrypt them using AES-GCM (Galois/Counter Mode), which is more secure than AES-CBC, and then create a dropper file for a majority of architectures and platforms out there.
Basically…
- It ingests dangerous malware that is now detectable by antivirus engines
- It then encrypts them and produces its own Go file
- Then that Go file can be cross-compiled to 99% of known architectures
- Upon execution, the encrypted payload is written to the disk and immediately executed on the command line
- Alternatively, instead of a file-drop, it will execute the reconstitute shellcode in memory using amenzhinsky’s go-memexec module github.com/amenzhinsky/go-memexec
- A custom shellcode executor is in the works, it takes ordinary C shellcode and after num-transform, it will run it by creating a new process after allocating the correct virtual address space and granting it RWX permissions on Windows
That means 32-bit and 64-bit architectures, and it works on Linux, Windows, Macs, Unix, Android, iPhone, etc. You take, anything, and I mean ANYTHING, like the 1988 Morris Worm that nearly brought down the internet (which exploited a flaw in the fingered listener daemon on UNIX), and makes it a viable cyberweapon again.
EXOCET is designed to be used with the DSX Program, or the “Cyber Metal Gear” as I envisioned it. Being able to launch and proliferate dangerous malware without a traceable launch trail.
EXOCET is written entirely in Go.