iblessing v1.0.4 beta releases: iOS security exploiting toolkit
iblessing
- iblessing is iOS security exploiting toolkit, it mainly includes application information collection, static analysis, and dynamic analysis.
- iblessing is based on a unicorn engine and capstone engine.
Features
- 🔥 Cross-platform: Tested on macOS and Ubuntu.
- iOS App static info extract, including meta data, deeplinks, urls, etc.
- Mach-O parser and dyld symbol bind simulator
- Objective-C class realizing and parsing
- Scanners making dynamic analysis for arm64 assembly code and find key information or attack surface
- Scanners using unicorn to partially simulate Mach-O arm64 code execution and find some features
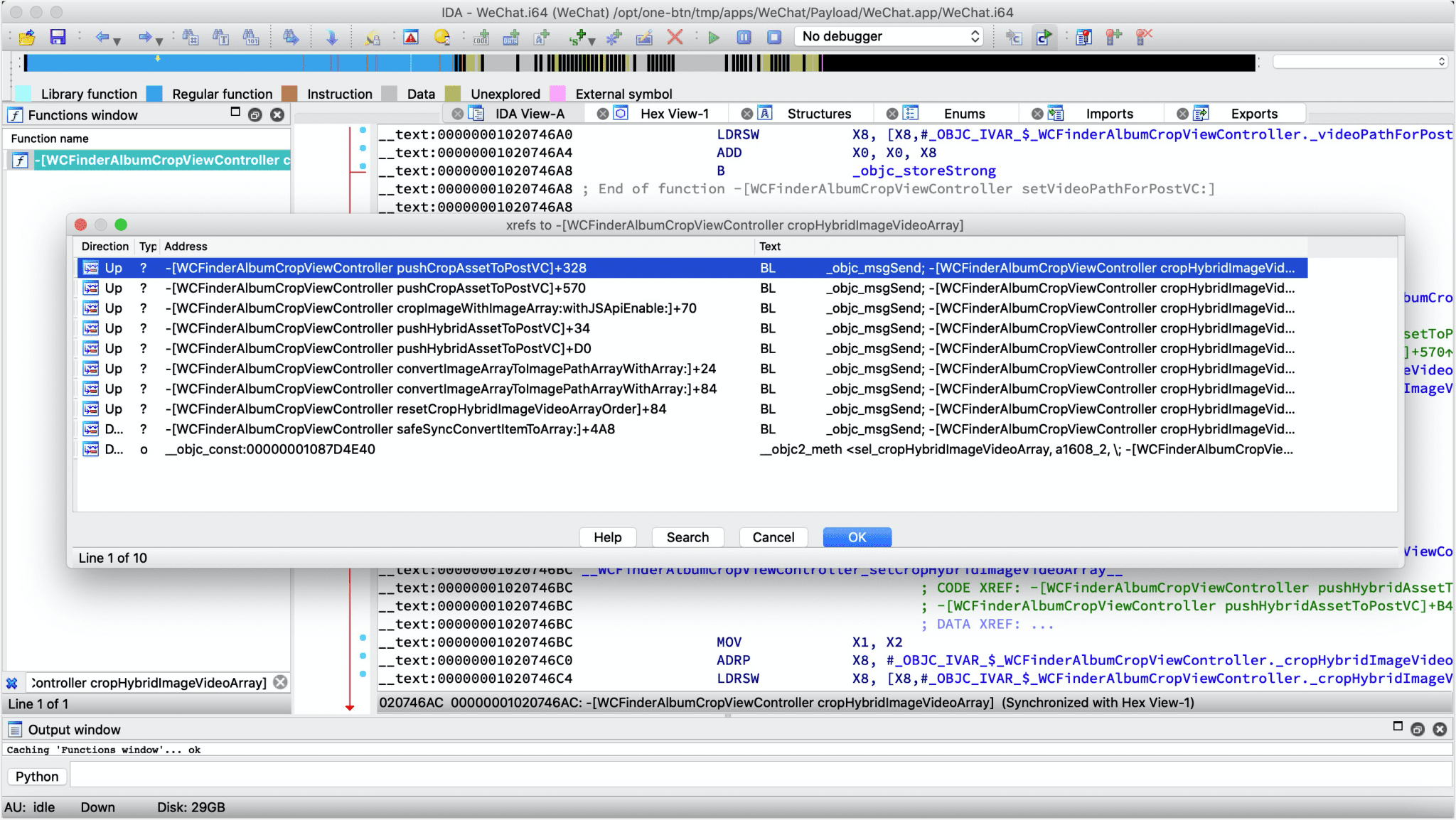
- Generators that can provide secondary processing on scanner’s report to start a query server, or generate script for IDA
- Super objc_msgSend xrefs scanner 😄
- objc methods and subs (such as blocks) emulation to generate xrefs like flare-emu
- objc function wrapper detects and ida usercall generate
- objc_msgSend sub-functions analysis
- objc block to objc_msgSend xrefs in args and a capture list
- report format including json, etc.
- Swift class and method parsing
- following branches and calls
- SimProcedures for extern symbols
- Tests
- Android Scanners Support
- Diagnostic logs
- More flexible scanner infrastructure for new scanner plugins
Changelog v1.0.4 beta
-
fix: bof
Use
Scanner
A scanner is a component used to output analysis reports through static and dynamic analysis of binary files, for example, the objc-msg-xref scanner can dynamically analyze most objc_msgSend cross-references.
[*] Scanner List:
– app-info: extract app infos
– objc-class-xref: scan for class xrefs
– objc-msg-xref: generate objc_msgSend xrefs record
– predicate: scan for NSPredicate xrefs and sql injection surfaces
– symbol-wrapper: detect symbol wrappers
Generator
A generator is a component that performs secondary processing on the report generated by the scanner, for example, it can generate IDA scripts based on the objc-msg-xref scanner’s cross-references report.
[*] Generator List:
– ida-objc-msg-xref: generator ida scripts to add objc_msgSend xrefs from objc-msg-xref scanner’s report
– objc-msg-xref-server: server to query objc-msg xrefs
– objc-msg-xref-statistic: statistics among objc-msg-send reports
Download & Tutorial
Copyright (C) 2020 Soulghost