maalik v2.4.3 releases: Network Pivoting and Post Exploitation Framework for Windows
Maalik
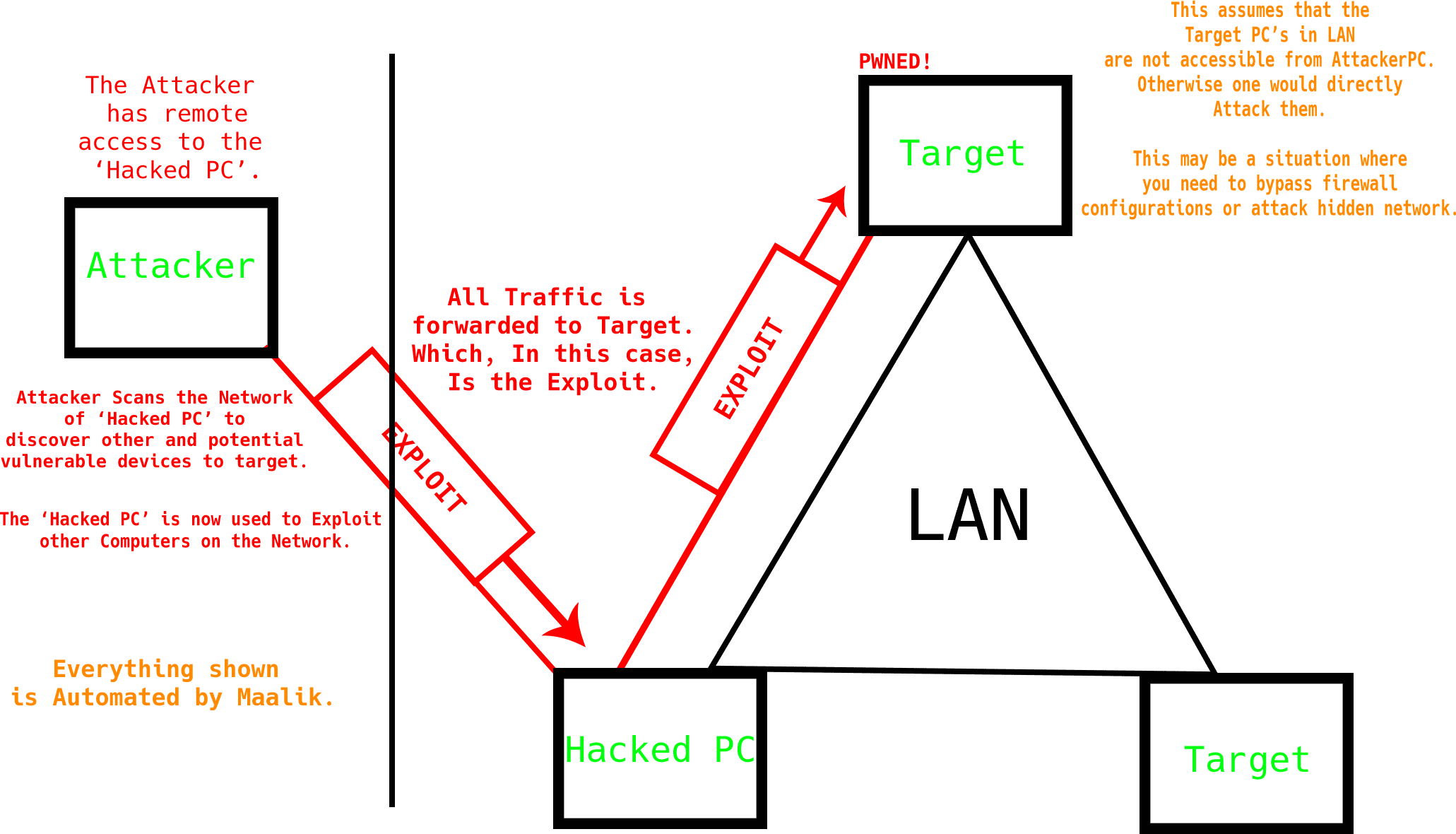
Network Pivoting and Post Exploitation Framework.
Features
Console Features
- Desktop notification on new sessions.
- Kill Online sessions easily.
- Build Maalik Client, Fhdawn easily.
- Configurable values in settings.ini
- Root shell.
- Multithreaded, Get multiple sessions.
- Maalik is extremenly easy to use.
Fhdawn Features
Fhdawn is the maalik client.
| Feature | Description |
|---|---|
| Stealth | Runs in the background, Only write hidden plaintext file to disk. |
| Execute / list / delete files and Browse | Full access to all files. Browse the system remotely. |
| Windows Defender Exclusions | Add Windows Defender Exclusions. |
| Network Pivoting | Forward a Port to another Host on the network to forward exploit traffic onto it. |
| Enable / Disable Firewall | Enable or Disable Windows Firewall, Use full for pivoting scenarios. The firewall is automatically turned off during the Pivot attack. |
| Network Scanner | Discover Hosts in the subnet. |
| Port Scanner | Scans discovered hosts for common ports. |
| Automatic Eternal Blue | Automatically runs Metasploit using rc file to potentially exploit Port 445. |
| Reverse Shell | Stable Reverse Shell, Commands executed as cmd.exe /c <your input>. |
| File upload / download | Upload or Download Files. |
| Reflective DLL Injection | Reflective DLL Injection into any process. |
| Screenshot | Take a screenshot (bmp=>png). |
| GeoLocation | Geolocate Fhdawn. |
| SAM Dump | Dumps SAM and SYSTEM files to disk, Downloads and dumps them using samdump2. |
Dynamic Payload System (DPS).
Executes ‘Payloads’ in Memory using Reflective DLL Injection. The Payload is a 32-bit Reflective DLL, That carries out tasks after successful Injection. DLL output is written to a TEXT file named output.png which is used to smuggle output back to the server, And also give the DLL Payload commands.
| Payload | Description |
|---|---|
| (DPS) Reverse Shell | Netcat Reverse shell. |
| (DPS) Administrator Prompt Trigger | Forcefully attempt to Execute an Application as Administrator. |
| (DPS) Chrome Password Recovery | Dumps Saved Google Chrome passwords. (Does not work on latest version) |
| (DPS) In Memory Meterpreter | Execute Metasploit C Shellcode. |
| (DPS) Keystroke logging | Log keystrokes. |
| (DPS) Capture Mic Input | Record Mic. |
CMD Post Exploitation Commands (CMD)
These are cmd commands that are useful in a post exploit situation. Not listed here.
- List users.
- View full System Information.
- View all Drivers.
- Get a list of running processes.
- Get Available Drive Letters.
- Get all environment variables.
- Displays information about sessions on a Remote Desktop Session Host server.
- Acronym for ‘netsh wlan show profiles’.
- Enable Remote Desktop.
- Disable Remote Desktop.
- Disable Firewall.
- Enable firewall.
- Forward a PORT on the Remote PC.
- Reset all forwarded Ports.
Changelog v2.4.3
- Added Control over Auto elevate.
- Build Bug fixed!
Install & Use
Copyright (c) 2020 QuantumCored