masm_shc v0.3 releases: creating shellcodes
masm_shc
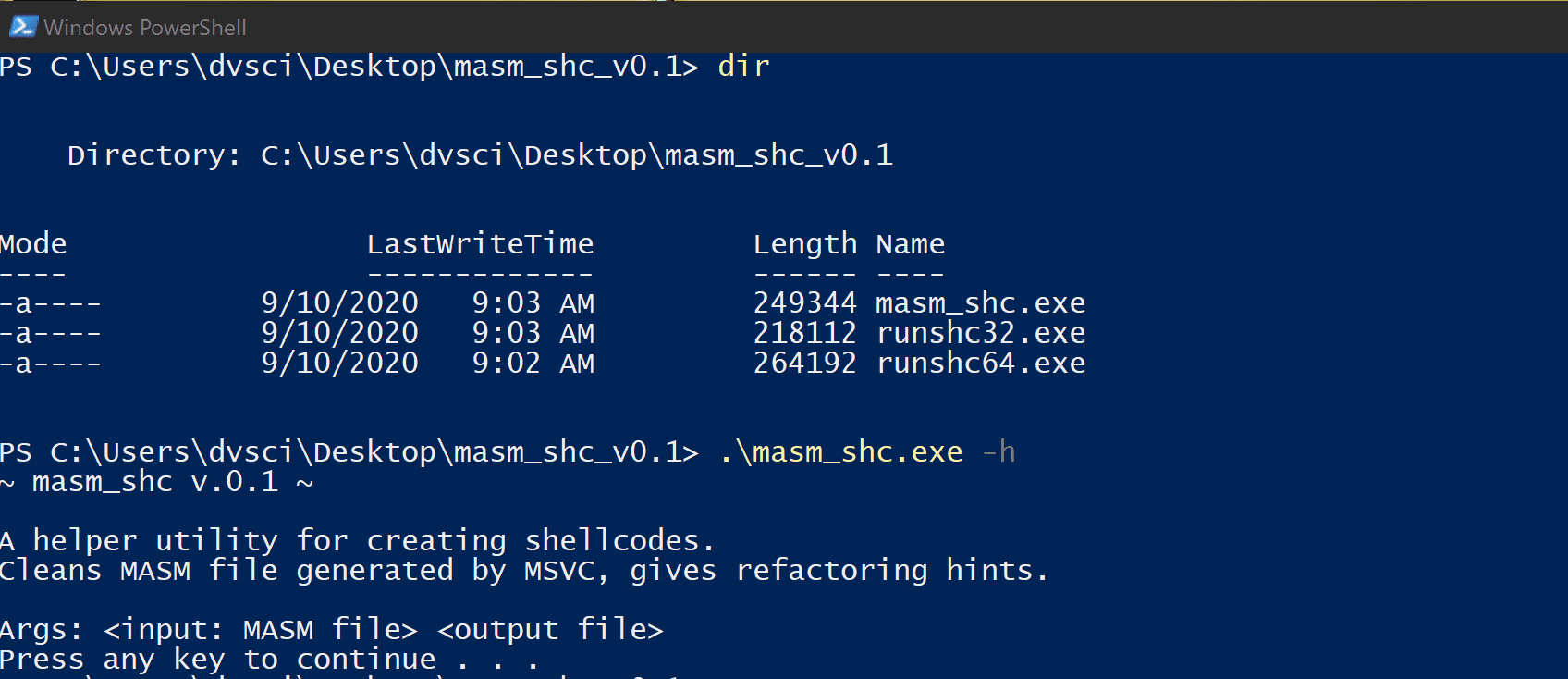
A helper utility for creating shellcodes. Cleans MASM file generated by MSVC gives refactoring hints.
demos
Examples of the code to be refactored to shellcode:
- popup.cpp – a simple “Hello World” Message Box
- knock.cpp – a simple server, opening ports, waiting for a defined input, giving a response
Howto
- Compile the example from C to MASM, using MSVC from a command line
cl /c /GS- /FA <file>.cpp
- Use masm_shc to clean the obtained MASM, inline the strings, etc.
masm_shc.exe <file>.asm <cleaned_file>.asm
It should automatically resolve most of the issues. The remaining issues should be resolved manually following the displayed hints. It will also inform if the Entry Point was changed
- Compile the resulting file by MASM into a PE (use ml for 32-bit files and ml64 for 64-bit files analogically)
ml <cleaned_file>.asm /link /entry:<my_entry_func>
- Use PE-bear to dump the .text section from the resulting PE. This will be our shellcode.
- Use runshc to test the shellcode (remember that the bitness of runshc must be the same as the bitness of the shellcode)
Download
Copyright (c) 2020 hasherezade