massExpConsole v2.3.5 releases: for mass exploiting
massExploitConsole
a collection of tools with a cli ui
disclaimer
- Please use this tool only on authorized systems, I’m not responsible for any damage caused by users who ignore my warning
- I do not own the code of adapted exploits or tools
- exploits are adapted from other sources, please refer to their author info
- Please note, due to my limited programming experience (it’s my first Python project), you can expect some silly bugs
Feature
- an easy-to-use cli ui
- execute any adpated exploits with process-level concurrency
- some built-in exploits (automated)
- hide your ip addr using proxychains4 and ss-proxy (built-in)
- zoomeye host scan (10 threads)
- google page crawler with gecko and Firefox (not fully working)
- a simple Baidu crawler (multi-threaded)
- censys host scan
Changelog v2.3.5
Bug Fixes
- unable to start when installed via BlackArch package (70250cc)
Installation
git clone https://github.com/jm33-m0/massExpConsole.git
cd massExpConsole
./mec.py
- if you ran mec.py and saw missing python modules, please run pip3 install -r requirements.txt (if anything is not listed, please report)
- now you should be good to go
- install any dependencies
- type proxy command to run a pre-configured Shadowsocks socks5 proxy in the background, vim ./data/ss.json to edit the proxy config. and, ss-proxy exits with mec.py
Usage
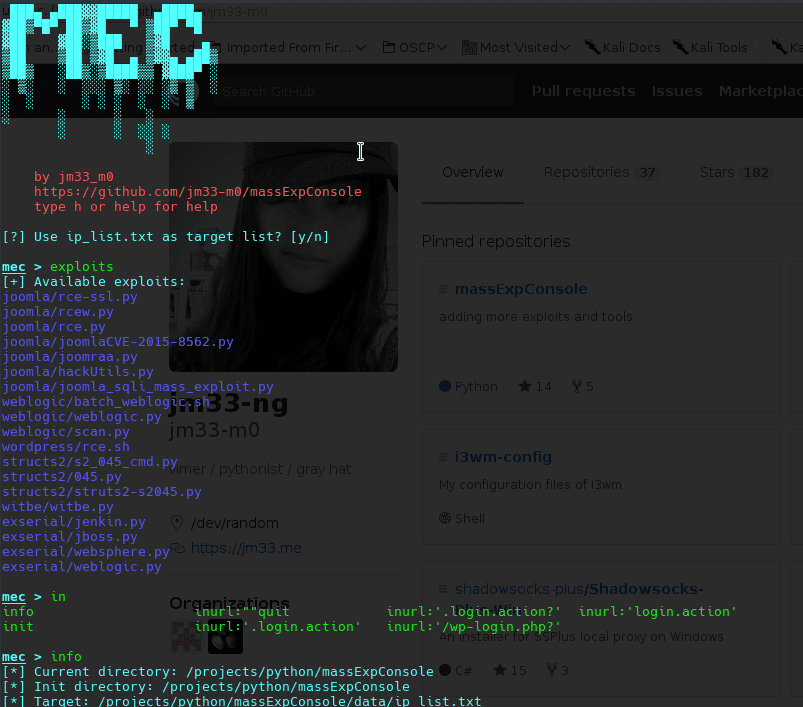
- just run mec.py, if it complains about missing modules, install them
- if you want to add your own exploit script (or binary file, whatever):
- cd exploits, mkdir <your_exploit_dir>
- your exploit should take the last argument passed to it as its target, dig into mec.py to know more
- chmod +x <exploit> to make sure it can be executed by the current user
- use attack command then m to select your custom exploit
- type help in the console to see all available features
- zoomeye requires a valid user account config file zoomeye.conf
Copyright (C) jm33-m0
Source: https://github.com/jm33-m0/






