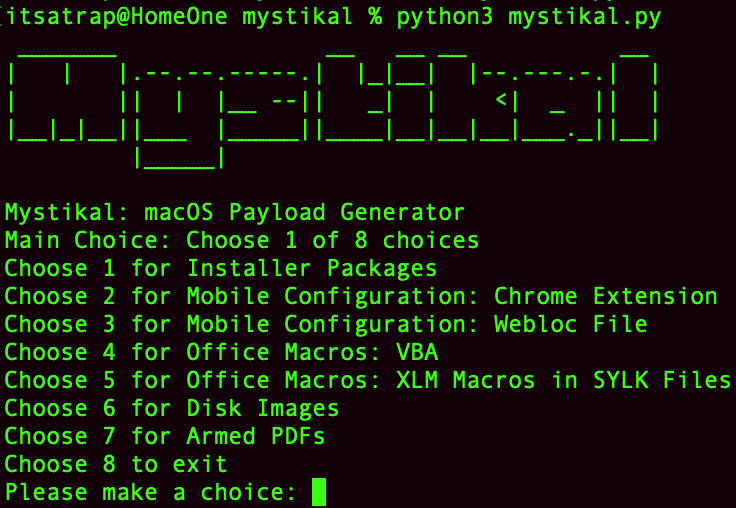
Mystikal v2.2.13 releases: macOS Initial Access Payload Generator
Mystikal
Mystikal is a macOS payload generator integrated with Mythic. Mystikal leverages Mythic scripting to log in and creates the necessary payload for the selected initial access method. Mystikal creates an Apfell or Leviathan payload depending on the chosen initial access method.
A common payload used for initial access is the installer package. These packages are eXtensible ARchiver (XAR) archives that conform to a specific folder structure and have a .pkg file extension. The easy comparison to Windows would be Windows installers which typically have the .msi file extension. As with Windows installers, installer packages execution typically results in an install wizard presented to the end-user for installation.
For offensive use, typical installer package execution relies upon preinstall and postinstall scripts, which are simple bash scripts that execute during the installation process. An alternative method depends upon the abuse of JavaScript within distribution Extensible Markup Language (XML) files using InstallerJS. Apple’s InstallerJS is an Application Programming Interface (API) leveraged in distribution XML files to perform installation checks.
Within the InstallerJS API is the system.run tag, which can execute system commands. The Silver Sparrow malware recently used this method. By abusing the distribution XML file, attackers can perform the same tasks typically within preinstall / postinstall scripts. The benefit of this method is that it makes it slightly harder to see what actions the installer package is performing. Additionally, due to the invocation time of the distribution XML file, the installer package does not need to finish the installation process for execution to occur.
Changelog v2.2.13
- Merge pull request #107 from its-a-feature/2.2-updates
- added in a few more pages for the new ui, updated mythic-cli to include…
Install
git clone https://github.com/D00MFist/Mystikal.git
cd Mystikal
sudo pip3 install -r requirements.txt
Use
Tutorial
Copyright (c) 2021, D00MFist
All rights reserved.