Octopus v1.2 releases: Open source pre-operation C2 server based on python and powershell
What is Octopus?
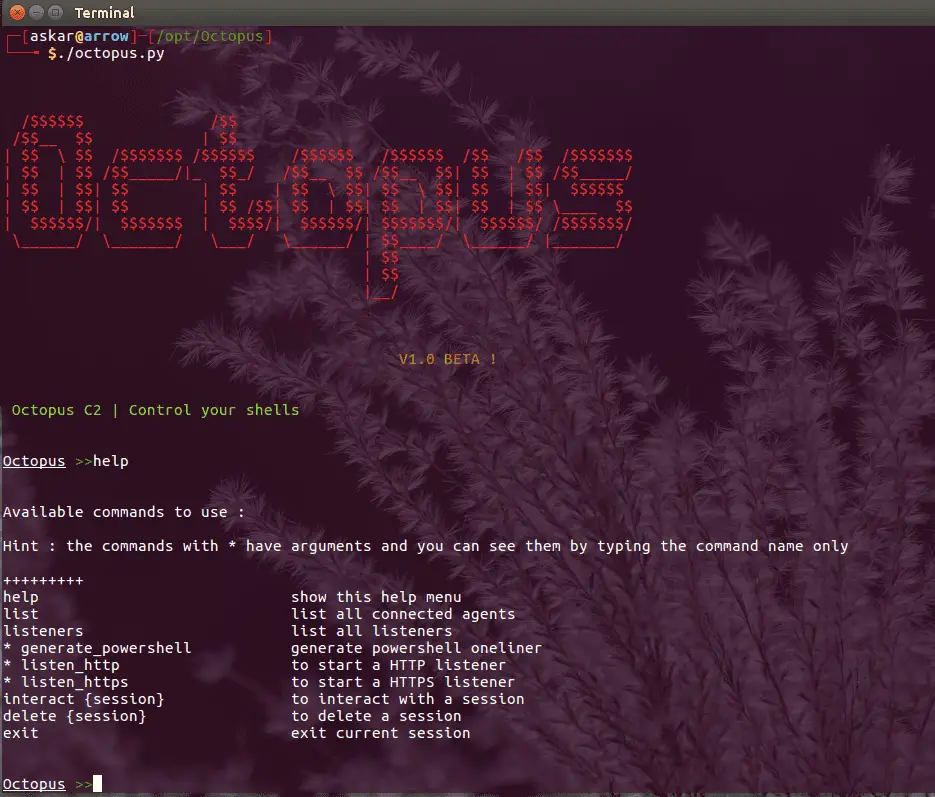
Octopus is an open-source, pre-operation C2 server based on python which can control an Octopus powershell agent through HTTP/S.
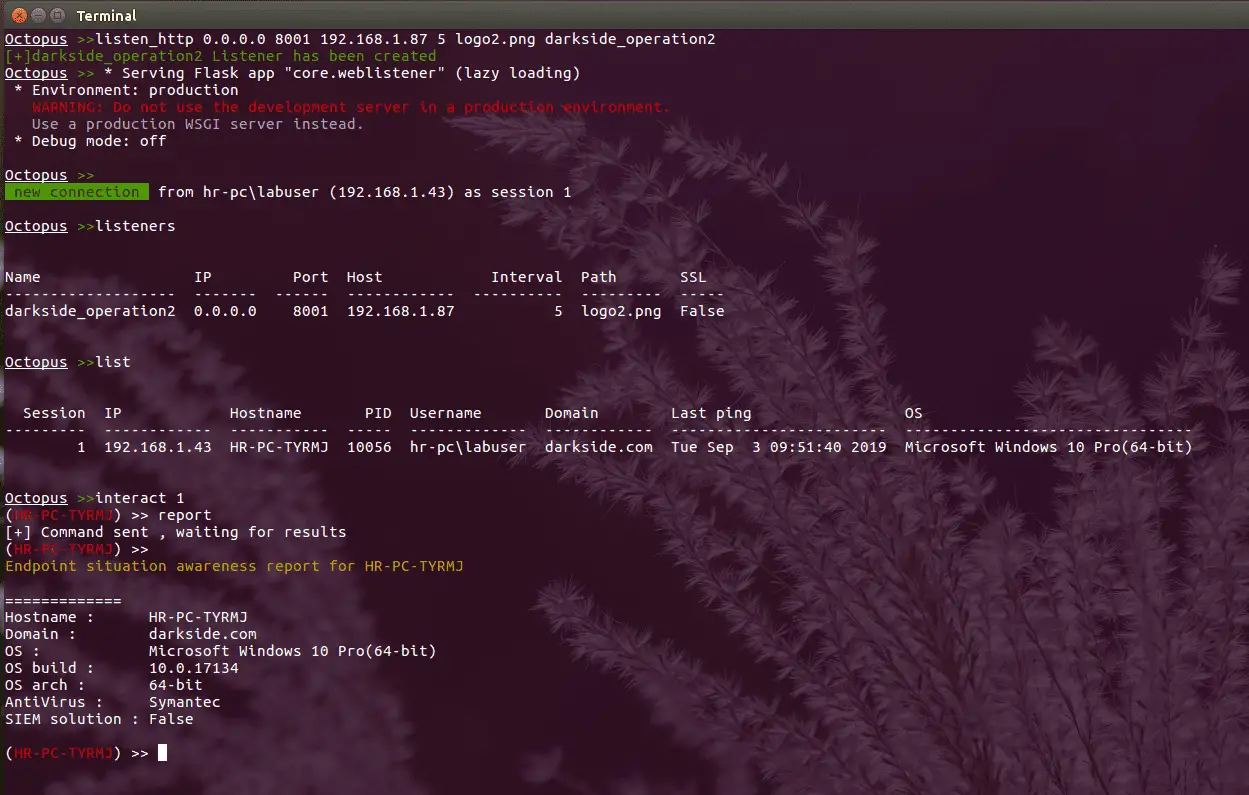
The main purpose of creating Octopus is for use before any red team operation, where rather than starting the engagement with your full operational arsenal and infrastructure, you can use Octopus first to attack the target and gather information before you start your actual red team operation.
It works in a very simple way to execute commands and exchange information with the C2 over a well-encrypted channel, which makes it inconspicuous and undetectable from almost every AV, endpoint protection, and network monitoring solution.
One cool feature in Octopus is called ESA, which stands for “Endpoint Situational Awareness”, which will gather some important information about the target that will help you to gain better understanding of the target network endpoints that you will face during your operation, thus giving you a shot to customize your real operation based on this information.
It is designed to be stealthy and covert while communicating with the C2, as it uses AES-256 by default for its encrypted channel between the powershell agent and the C2 server. You can also opt for using SSL/TLS by providing a valid certificate for your domain and configuring the Octopus C2 server to use it.
Key features
Octopus is packed with a number of features that allows you to gain an insight into your upcoming engagement before you actually need to deploy your full arsenal or tools and techniques, such as:
- Control agents through HTTP/S.
- Execute system commands.
- Download / Upload files.
- Load external powershell modules.
- Use encrypted channels (AES-256) between C2 and agents.
- Use inconspicuous techniques to execute commands and transfer results.
- Create custom and multiple listeners for each target.
- Generate different types of payloads.
- Support all Windows versions with powershell 2.0 and higher.
- Run Octopus windows executable agent without touching powershell.exe process.
- Gather information automatically from the endpoint (endpoint situational awareness) feature.
Changelog v1.2
New Features
- Shellcode generation for both x64 and x86 architecture.
- New Octopus agent with spoofed arguments.
- Word Macro generation (will be updated with each version).
- Updated the core agent to avoid more AVs.
- Special indicator while receiving a connection from privileged users.
You can check This article for more information about Octopus v1.2
Install && Use
Copyright (C) 2019 mhaskar