sniffglue v0.16 releases: Secure multithreaded packet sniffer
sniffglue
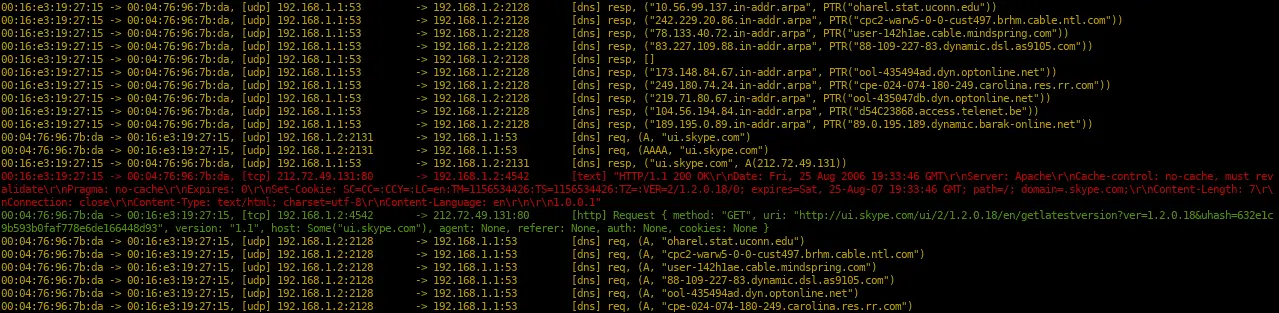
sniffglue is a network sniffer written in rust. Network packets are parsed concurrently using a thread pool to utilize all cpu cores. Project goals are that you can run sniffglue securely on untrusted networks and that it must not crash when processing packets. The output should be as useful as possible by default.
Protocols
- ethernet
- ipv4
- ipv6
- arp
- tcp
- udp
- icmp
- http
- tls
- dns
- dhcp
- cjdns eth beacons
- ssdp
- Dropbox beacons
- 802.11
Changelog v0.16
- Improved http request/response parser and logging ✨
- If TCP RST packet has data, still show it grey instead of red to improve signal:noise ratio
- Add support for LoongArch64 (#123, thanks @heiher)
- Replaced users with uzers, RUSTSEC-2023-0059 (#124, thanks @nc7s)
- Add Fedora/CentOS installation instructions (#107, thanks @tim77)
- Update dependencies (ported to clap 4, updated to Rust edition 2021, …)
Installation
There is an official package available for archlinux:
pacman -S sniffglue
To build from source, make sure you have libpcap and libseccomp installed, Debian/Ubuntu: libpcap-dev libseccomp-dev, Archlinux: libpcap libseccomp.
git clone
cargo install sniffglue
Docker
You can build sniffglue as a docker image to debug container setups. The image is currently about 11.1MB. It is recommended to push it to your own registry.
docker build -t sniffglue . docker run -it --init --rm --net=host sniffglue eth0
Use
sniffglue enp0s25
Security
To report a security issue please contact kpcyrd on ircs://irc.hackint.org.
Seccomp
To ensure a compromised process doesn’t compromise the system, sniffglue uses seccomp to restrict the syscalls that can be used after the process started. This is done in two stages, first at the very beginning (directly after env_logger initialized) and once after the sniffer has been set up, but before packets are read from the network.
Hardening
During the second stage, there’s also some general hardening that is applied before all unneeded syscalls are finally disabled. Those are system specific, so a configuration file is read from /etc/sniffglue.conf. This config file specifies an empty directory for chroot and an unprivileged account in user that is used to drop root privileges.
boxxy-rs
This project includes a small boxxy-rs based shell that can be used to explore the sandbox at various stages during and after initialization. This is also used by Travis to ensure the sandbox actually blocks syscalls.
cargo run --example boxxy
Reproducible builds
This project is tested using reprotest. Currently, the following variations are excluded:
- -time – needed because the crates.io cert expires in the future
- -domain_host – requires root for unshare(2) and has been excluded
Don’t forget to install the build dependencies.
ci/reprotest.sh
Fuzzing
The packet processing of sniffglue can be fuzzed using cargo-fuzz. Everything you should need is provided in the fuzz/ directory that is distributed along with its source code. Please note that this program links to libpcap which is not included in the current fuzzing configuration.
cargo fuzz run read_packet
Copyright (C) 2018 kpcyrd
Source: https://github.com/kpcyrd/