Telemetry Sourcerer v0.11 releases: Enumerate and disable common sources of telemetry
Telemetry Sourcerer
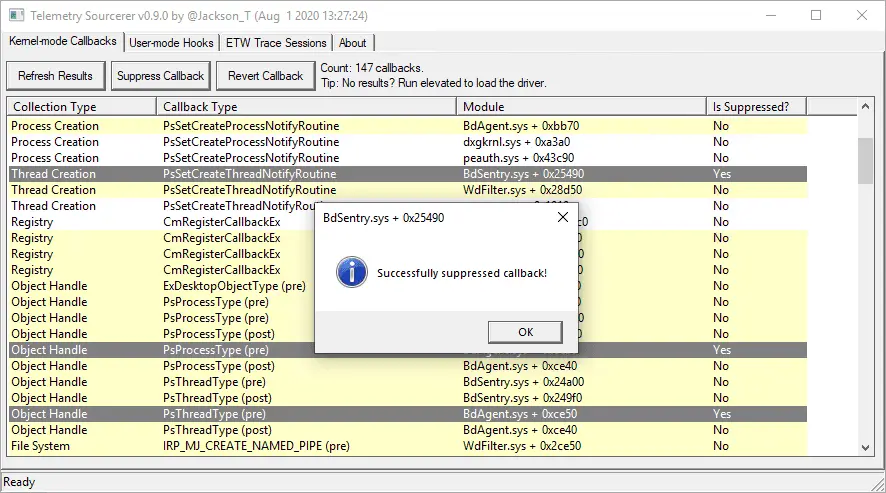
Telemetry Sourcerer can enumerate and disable common sources of telemetry used by AV/EDR on Windows.
Red teamers and security enthusiasts can use this tool in a lab environment to:
- Identify collection-based blind spots in the products they’re up against.
- Determine which sources of telemetry generate particular types of events.
- Validate whether using the tool’s tampering capabilities can lead to detection.
 For details on building a private lab, consider reading my post on Diverting EDR Telemetry to Private Infrastructure.
For details on building a private lab, consider reading my post on Diverting EDR Telemetry to Private Infrastructure.
OPSEC WARNING: Although it’s possible to use this in targeted environments, there are OPSEC risks when using any offensive security tool as is. You can instead leverage the code from this project into your own tooling for operational use and combine with other techniques to reduce the footprint it creates.
Features
- Enumerates various kernel-mode callbacks with the ability to suppress them.
- Detects inline user-mode hooks within the process, with the ability to unhook them.
- Lists ETW sessions and providers while highlighting potentially relevant ones to disable.
Caveats and Limitations
- This tool is meant for research purposes only and is not OPSEC-safe for production use.
- Compiled with Visual Studio 2019 using the Windows 10 SDK (10.0.19041.0) and WDK (2004).
- Currently does not look for IAT/EAT user-mode hooks, or kernel-mode hooks.
- The driver has not been thoroughly tested for abuse cases.
- Tested on Windows 7 and 10 only.
Changelog v0.11
Added
- Added support for Windows 10 20H2.
Changed
- Fixed code correctness issues (h/t to @JohnLaTwC).






