WinPayloads – Undetectable Windows Payload Generation
WinPayloads is a payload generator tool that uses Metasploit’s meterpreter shellcode, injects the users ip and port into the shellcode and writes a python file that executes the shellcode using ctypes. This is then aes encrypted and compiled into a Windows Executable using pyinstaller.
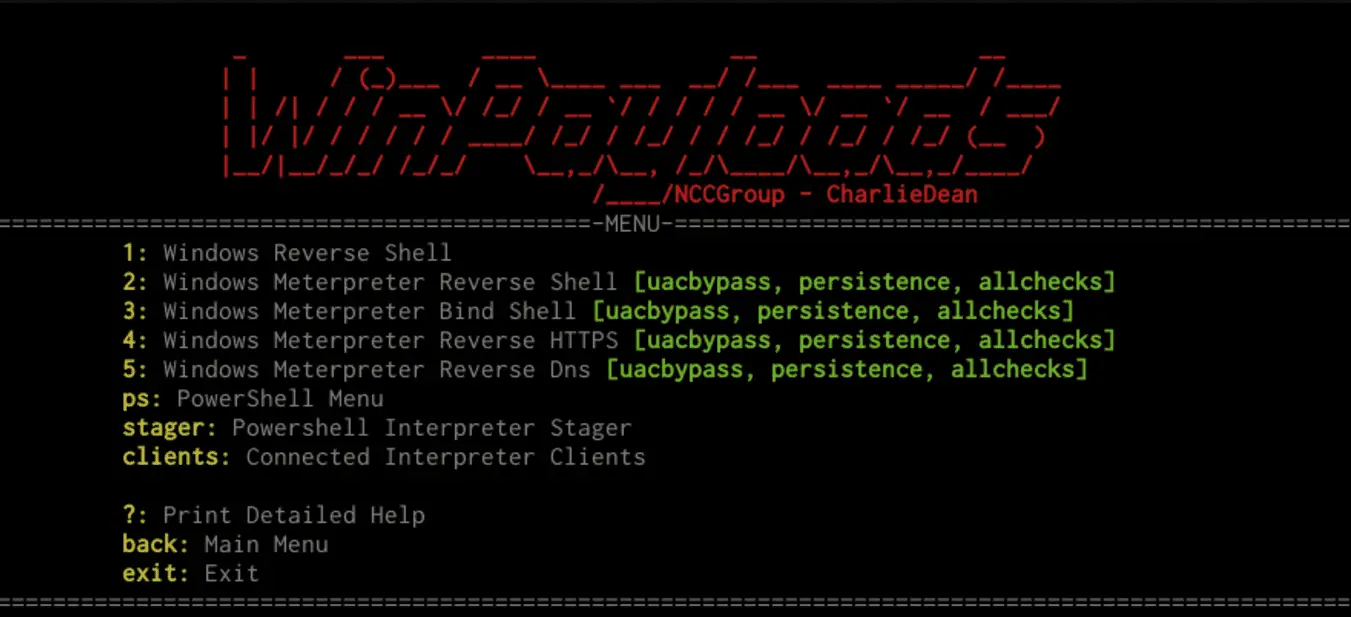
Features
- UACBypass – PowerShellEmpire https://github.com/PowerShellEmpire/Empire/raw/master/data/module_source/privesc/Invoke-BypassUAC.ps1 Copyright (c) 2015, Will Schroeder and Justin Warner. All rights reserved.
- PowerUp – PowerShellEmpire https://raw.githubusercontent.com/PowerShellEmpire/PowerTools/master/PowerUp/PowerUp.ps1 Copyright (c) 2015, Will Schroeder and Justin Warner. All rights reserved.
- Invoke-Shellcode https://github.com/PowerShellMafia/PowerSploit/blob/master/CodeExecution/Invoke-Shellcode.ps1Copyright (c) 2012, Matthew Graeber. All rights reserved.
- Invoke-Mimikatz https://github.com/PowerShellMafia/PowerSploit/blob/master/Exfiltration/Invoke-Mimikatz.ps1Copyright (c) 2012, Matthew Graeber. All rights reserved.
- Invoke-EventVwrBypass https://github.com/enigma0x3/Misc-PowerShell-Stuff/blob/master/Invoke-EventVwrBypass.ps1Matt Nelson (@enigma0x3)
- Persistence – Adds payload persistence on reboot
- Psexec Spray – Spray hashes until successful connection and psexec payload on target
- Upload to local web server – Easy deployment
- Powershell stager – allows invoking payloads in memory & more
Installation
Demo
Source: https://github.com/nccgroup/






