bincat v1.2 releases: Binary code static analyser, with IDA integration
What is BinCAT?
A static Binary Code Analysis Toolkit, designed to help reverse engineers, directly from IDA.
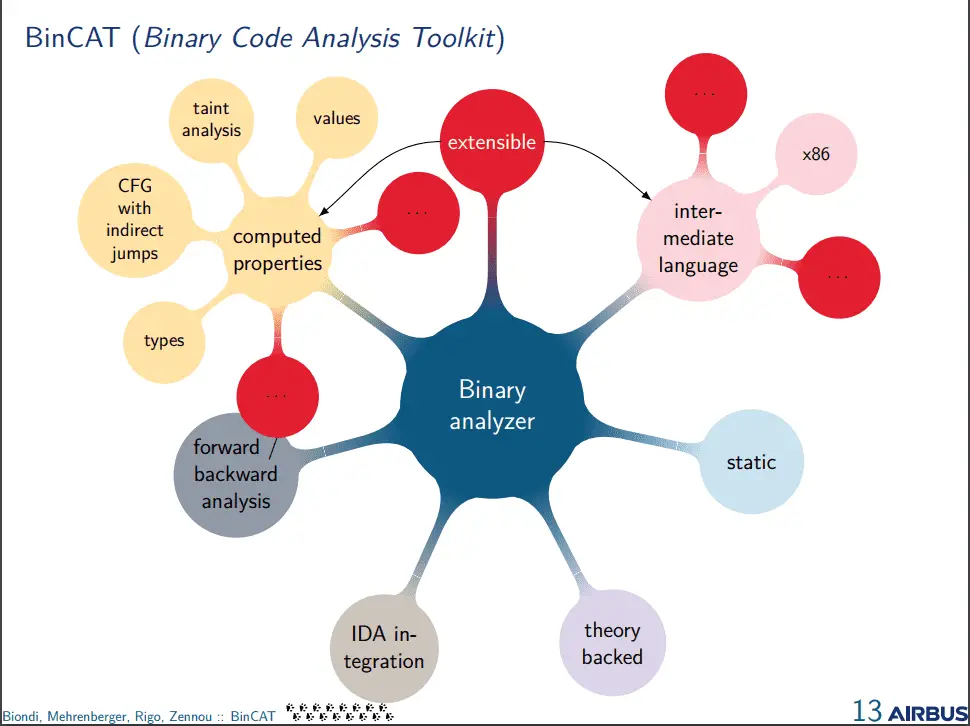
It features:
- value analysis (registers and memory)
- taint analysis
- type reconstruction and propagation
- backward and forward analysis
Changelog v1.2
- Initial RISC-V support
- Initial, incomplete, ARMv7 Thumb support
- Python 3 migration (IDA 7.4 required)
- Asynchronous code path (signal handler/int3/int X) support
- Many small bugfixes and improvements
In action
You can check BinCAT in action here:
Check the tutorial out to see the corresponding tasks.
Quick FAQ
Supported host platforms:
- IDA plugin: all, version 6.9 or later (BinCAT uses PyQt, not PySide)
- analyzer (local or remote): Linux, Windows, macOS (maybe)
Supported CPU for analysis (for now):
- x86-32
- ARMv7
- ARMv8
- PowerPC
Installation
Binary distribution install (recommended)
The binary distribution includes everything needed:
- the analyzer
- the IDA plugin
Install steps:
- Extract the binary distribution of BinCAT (not the git repo)
- In IDA, click on “File -> Script File…” menu (or type ALT-F7)
- Select install_plugin.py
- BinCAT is now installed in your IDA user dir
- Restart IDA
Analyzer
The analyzer can be used locally or through a Web service.
On Windows, the binary distribution includes the analyzer.
On Linux:
- Using Docker: Docker installation instructions
- Manual: Manual installation instructions
IDA Plugin
Only IDA v6.9 or later (7 included) are supported
Install for Windows
- Unzip BinCAT
- In IDA, click on “File -> Script File…” menu (or type ALT-F7)
- Select
- BinCAT is now installed in your IDA user dir
Or install manually.
Linux install
It should work with IDA on Wine, once pip is installed:
- download https://bootstrap.pypa.io/get-pip.py (verify it’s good 😉
- ~/.wine/drive_c/Python27/python.exe get-pip.py
Using
Quickstart
- Load the plugin by using the Ctrl-Shift-B shortcut, or using the Edit -> Plugins -> BinCAT menu
- Select an instruction in any IDA view, then use the Ctrl-Shift-A shortcut, or the BinCAT -> Analyze from here context menu
Configuration
Global options can be configured through the Edit/BinCAT/Options menu.
Default config and options are stored in $IDAUSR/idabincat/conf.
Options
- Use remote bincat: select if you are running docker in a Docker container
- Remote URL: http://localhost:5000 (or the URL of a remote BinCAT server)
- Autostart: autoload BinCAT at IDA startup
- Save to IDB: default state for the save to idb checkbox







