Category: Post Exploitation
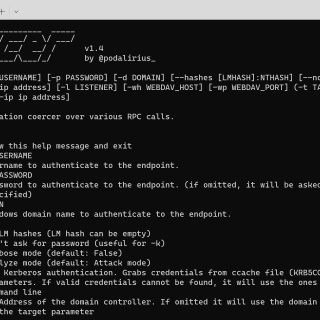
Coercer A python script to automatically coerce a Windows server to authenticate on an arbitrary machine through 9 methods. Features Automatically detects open SMB pipes on the remote machine. Calls one by one all...
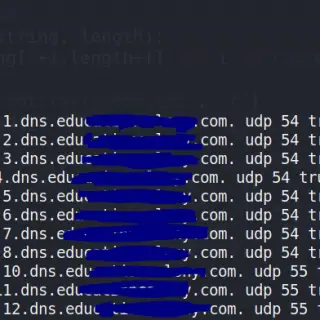
What is DNS Tunneling? DNS tunneling is a technique that has been around for a long time and is used by a variety of attackers. At a basic level, it involves using the DNS...
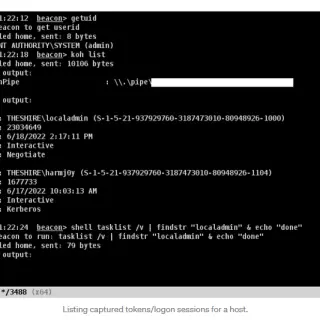
Koh Koh is a C# and Beacon Object File (BOF) toolset that allows for the capture of user credential material via purposeful token/logon session leakage. Technical Background When a new logon session is estabslished...
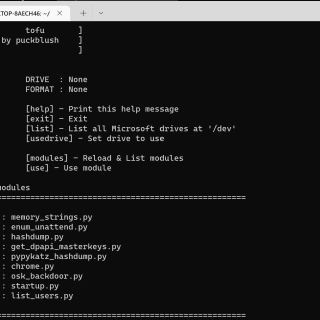
tofu A modular tool for hacking offline Windows filesystems and bypassing login screens. Can do hashdumps, OSK-Backdoors, user enumeration, and more. How it works : When a Windows machine is shut down, unless it...
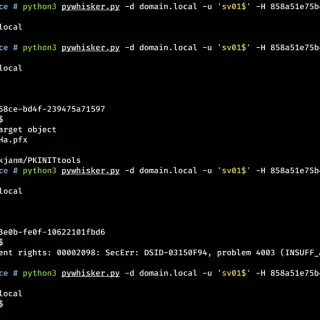
PyWhisker pyWhisker is a Python equivalent of the original Whisker made by Elad Shamir and written in C#. This tool allows users to manipulate the msDS-KeyCredentialLink attribute of a target user/computer to obtain full control over that object. It’s...
pyCobaltHound pyCobaltHound is an Aggressor script extension for Cobalt Strike which aims to provide deep integration between Cobalt Strike and Bloodhound. pyCobaltHound strives to assist red team operators by: Automatically querying the BloodHound database to discover escalation paths opened...
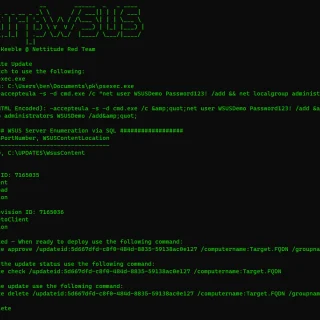
SharpWSUS SharpWSUS is a CSharp tool for lateral movement through WSUS. WSUS is a Microsoft solution for administrators to deploy Microsoft product updates and patches across an environment in a scalable manner, using a...
BOFHound BOFHound is an offline BloodHound ingestor and LDAP result parser compatible with TrustedSec’s ldapsearch BOF and the Python adaptation, pyldapsearch. BOFHound will parse sets of log files to generate BloodHound compatible JSON files for those times...
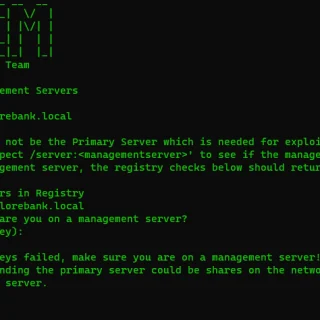
MalSCCM This tool allows you to abuse local or remote SCCM servers to deploy malicious applications to hosts they manage. To use this tool your current process must have admin rights over the SCCM...
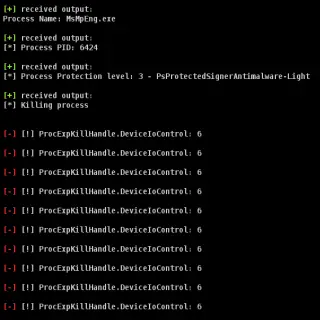
KDStab This is a Beacon Object File combined implementation of Yaxser’s Backstab and pwn1sher’s KillDefender for use with Cobalt Strike. KDStab is a post-exploitation tool to defeat Windows Defender (in theory it could work...
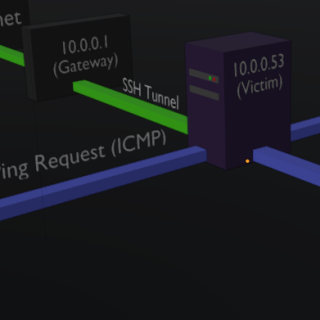
Puwr Easily expand your attack surface on a local network by discovering more hosts, via SSH. Using a machine running an SSH service, Puwr uses a given subnet range to scope out IP’s, sending...
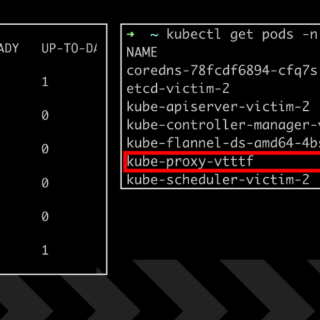
k0otkit – Manipulate K8s in a K8s way k0otkit is a universal post-penetration technique which could be used in penetrations against Kubernetes clusters. With k0otkit, you can manipulate all the nodes in the target...
Tetanus Tetanus is a Windows and Linux C2 agent written in rust. Features Background job management Built-in ssh client Connect to a machine and download/upload files between that machine and Mythic Get directory listings...
BOF – Lateral movement technique by abusing Windows Perception Simulation Service to achieve DLL hijacking ServiceMove is a POC code for an interesting lateral movement technique by abusing Windows Perception Simulation Service to achieve...
EventViewerUAC_BOF This is a Beacon Object File implementation of the Event Viewer deserialization UAC bypass discovered by @orange_8361 and the POC put together by CsEnox. OPSEC WARNINGS! This UAC bypass performs the following actions which should be...