Category: Vulnerability Analysis
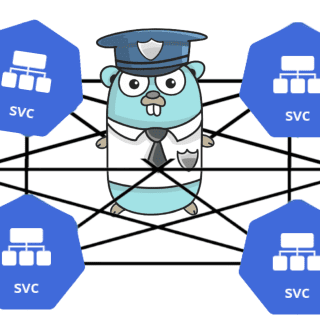
mesh-kridik Enhance your Kubernetes service mesh security !! mesh-kridik is an open-source security scanner that performs various security checks on a Kubernetes cluster with istio service mesh and outputs a security report. The security...
dorkscout dokrscout is a tool to automate the finding of vulnerable applications or secret files around the internet through google searches, dorkscout first starts by fetching the dorks lists from https://www.exploit-db.com/google-hacking-database, and then it...
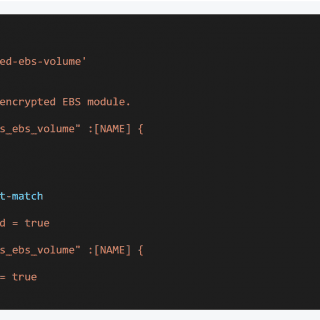
shisho Shisho is a lightweight static code analyzer designed for developers and security teams. The key motivation of Shisho is providing a means of Security-as-Code for Code. It allows us to analyze and transform your source...
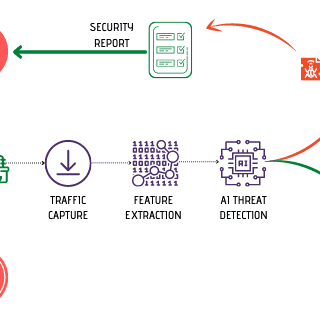
Civilsphere AI VPN The goal of this project is to better protect the privacy of civil society by researching and developing a locally and easy-to-implement VPN that checks the traffic of devices with AI-based...
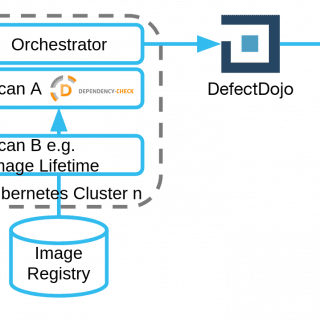
Cluster Scanner The Cluster Scanner detects images in a Kubernetes cluster and provides fast feedback based on various security tests. It is recommended to run the Cluster Scanner in production environments in order to...
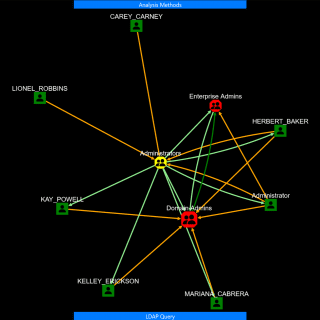
adalanche – Active Directory ACL Visualizer and Explorer Active Directory security is notoriously difficult. Small organizations generally have no idea what they’re doing, and way too many people are just added to Domain Admins....
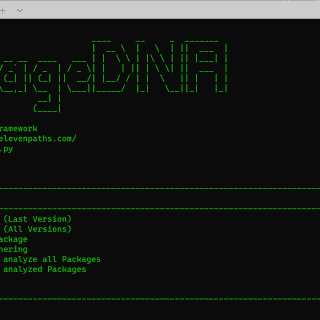
PackageDNA This tool gives developers, researchers, and companies the ability to analyze software packages of different programming languages that are being or will be used in their codes, providing information that allows them to...
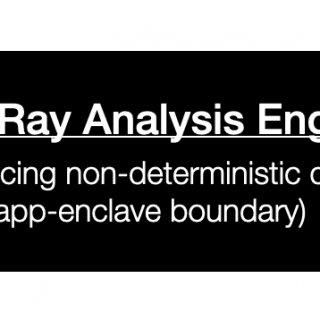
SGXRay: Automating Vulnerability Detection for SGX Apps Intel SGX protects isolated application logic and sensitive data inside an enclave with hardware-based memory encryption. To use such hardware-based security mechanism requires a strict programming model...
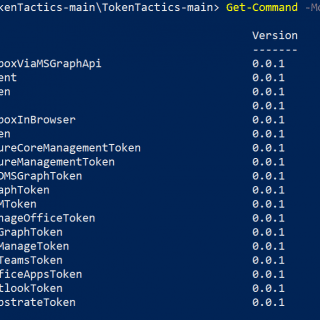
TokenTactics Azure JSON Web Token (“JWT”)Token Manipulation Toolset Azure JWT’s allow you to authenticate to certain endpoints as the user who signed in with the device code. Even if they used multi-factor authentication. Once...
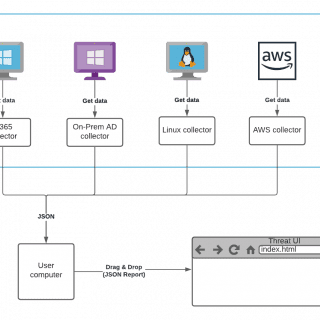
Tiuku Tiuku is a tool for scanning various kinds of systems and environments for security-related information and displaying the results in a browser-based user interface. It can also detect and highlight some issues automatically....
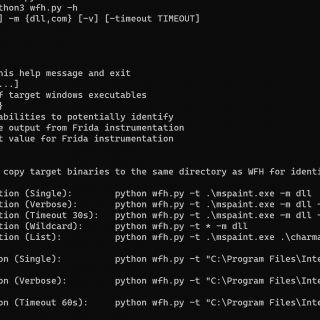
Windows Feature Hunter (WFH) Windows Feature Hunter (WFH) is a proof of concept python script that uses Frida, a dynamic instrumentation toolkit, to assist in potentially identifying common “vulnerabilities” or “features” within Windows executables. WFH...
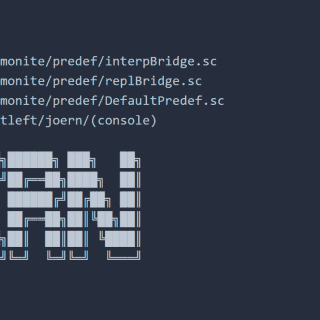
joern Joern is a platform for robust analysis of C/C++ code. It generates code property graphs, a graph representation of code for cross-language code analysis. Code property graphs are stored in a custom graph...
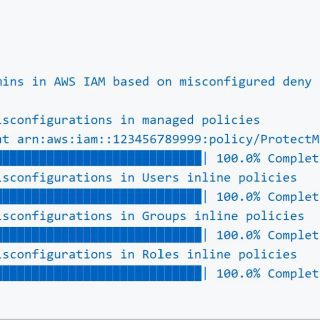
Red-Shadow Lightspin AWS IAM Vulnerability Scanner Scan your AWS IAM Configuration for shadow admins in AWS IAM based on misconfigured deny policies not affecting users in groups discovered by Lightspin’s Security Research Team. The...
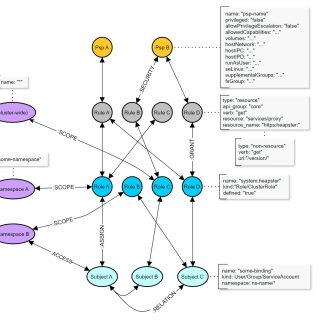
Krane Krane is a simple Kubernetes RBAC static analysis tool. It identifies potential security risks in K8s RBAC design and makes suggestions on how to mitigate them. Krane dashboard presents the current RBAC security posture and...
gosec – Golang Security Checker Inspects source code for security problems by scanning the Go AST. Usage Gosec can be configured to only run a subset of rules, exclude certain file paths, and produce...