Category: Reverse Engineering
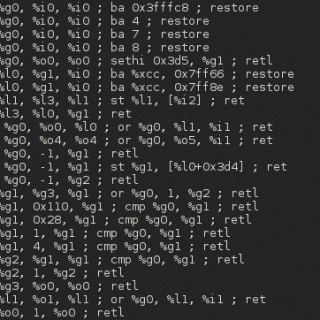
Exrop Exrop is automatic ROP chains generator tool which can build gadget chain automatically from given binary and constraints Only support for x86-64 for now! Features: handling non-return gadgets (jmp reg, call reg) set...
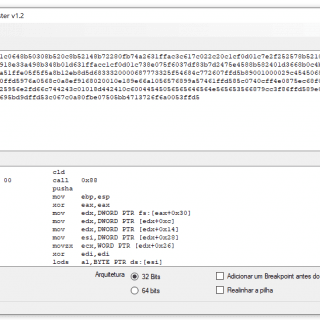
ShellCode Tester This tool tests generated ShellCodes. Download Use Example Source: https://github.com/helviojunior/
Windows shellcode emulation tool based upon unicorn framework ShellcodeEmulator emulates Windows shellcode with the help of windbg process memory dumps. You can provide shellcode to analyze with any Windows process dump image. The tool will...
Memory Mapper Memory Mapper is a lightweight library that allows the ability to map both native and managed assemblies into memory by either using process injection of a process specified by the user or...
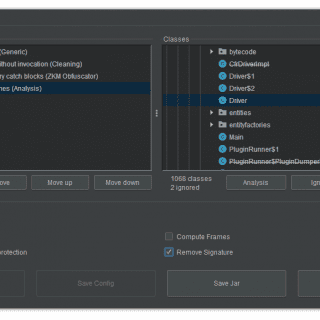
Threadtear Threadtear is a multifunctional deobfuscation tool for java. Android application support is coming soon (Currently working on a Dalvik to java converter). Suitable for easier code analysis without worrying too much about obfuscation....
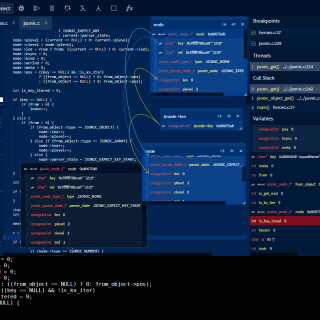
GDBFrontend GDBFrontend is an easy, flexible, and extension-able gui debugger. Changelog v0.11.3 beta Fixed startup issue on MacOS for x86_64 architecture (now it must be usable on x64 MacOS, please report if you encounter...
ATFuzzer “Opening Pandora’s Box through ATFuzzer: Dynamic Analysis of AT Interface for Android Smartphones” is accepted to the 35th Annual Computer Security Applications Conference (ACSAC) 2019. Structure of ATFuzzer implementation In the following, we...
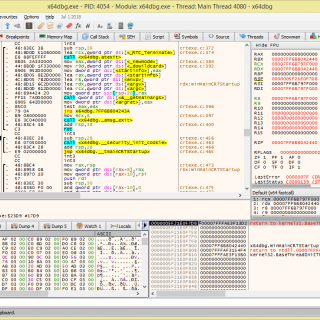
x64dbg x64dbg is an open-source binary debugger for Windows, aimed at malware analysis and reverse engineering of executables you do not have the source code for. There are many features available and a comprehensive...
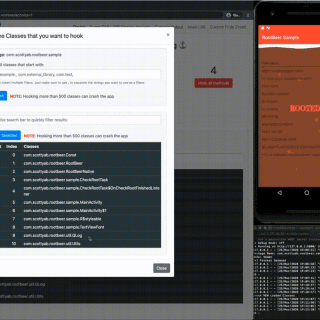
Runtime Mobile Security Runtime Mobile Security (RMS), powered by FRIDA, is a powerful web interface that helps you to manipulate Android Java Classes and Methods at Runtime. You can easily dump all the loaded classes...
libptrace libptrace is an event-driven process/thread debugging, tracing, and manipulation framework. It is written in C and has Python 2.7 bindings. It is meant to be used as a library. The API has been...
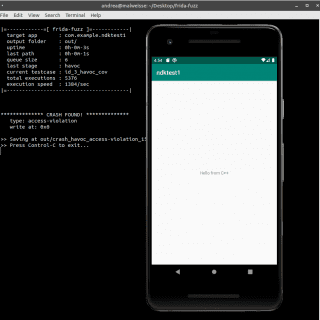
Frida/QBDI Android API Fuzzer This experimental fuzzer is meant to be used for API in-memory fuzzing on Android. The design is highly inspired and based on AFL/AFL++. ATM the mutator is quite simple, just...
angrgdb Use angr inside GDB. Create an angr state from the current debugger state. Install pip install angrgdb echo “python import angrgdb.commands” >> ~/.gdbinit Usage angrgdb implements the angrdbg API in GDB. You can use it...
Bleak A Windows native DLL injection library that supports several methods of injection. Injection Methods CreateThread HijackThread ManualMap Optional Extensions EjectDll HideDllFromPeb RandomiseDllHeaders RandomiseDllName Features WOW64 and x64 injection Caveats Attempting to inject into...
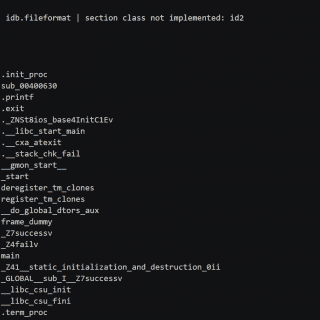
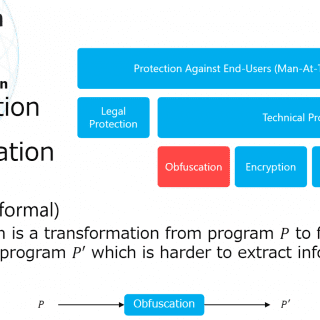
Advanced Binary Deobfuscation This repository contains the course materials of Advanced Binary Deobfuscation at the Global Cybersecurity Camp (GCC) Tokyo in 2020. Course Abstract Reverse engineering is not easy, especially if a binary code is obfuscated....
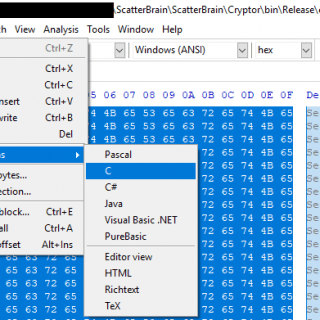
ScatterBrain Suite ScatterBrain is a shellcode runner with a variety of execution and elevation options. Given unencoded shellcode, it will then be encoded with the XOR key SecretKey (found in Cryptor/Program.cs and ScatterBrain/Headers/RawData.h) using the Cryptor binary. Cryptor.exe...