DeTTECT v1.9 releases: Detect Tactics, Techniques & Combat Threats
DeTTECT
DeTT&CT aims to assist blue teams using ATT&CK to score and compare data log source quality, visibility coverage, detection coverage, and threat actor behaviors. All of which can help, in different ways, to get more resilient against attacks targeting your organization. The DeTT&CT framework consists of a Python tool, YAML administration files and scoring tables for the different aspects.
DeTT&CT provides the following functionality:
- Administrate and score the quality of your data sources.
- Get insight on the visibility you have on for example endpoints.
- Map your detection coverage.
- Map threat actor behaviors.
- Compare visibility, detections and threat actor behaviors to uncover possible improvements in detection and visibility. This can help you to prioritize your blue teaming efforts.
The colored visualizations are created with the help of MITRE’s ATT&CK™ Navigator.
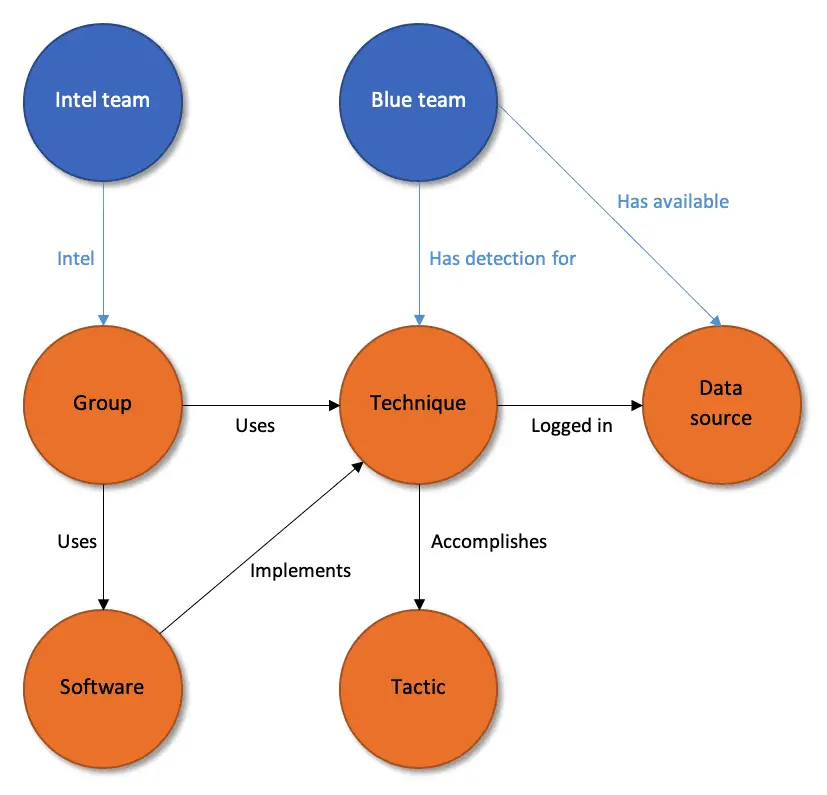
The Cyber Threat Intelligence Repository of MITRE ATT&CK™ contains loads of valuable information on:
- TTPs (Tactics, Techniques and Procedures)
- Groups (threat actors)
- Software (software used by threat actors)
- Data sources (visibility required for detection)
The relationship between these types of information can be visualized using the following diagram:
You can map the information you have within your organization on the entities available in ATT&CK. DeTT&CT delivers a framework which does exactly that, and it will help you to administrate your blue team’s data sources (including data quality), visibility and detection. It will also provide you with means to administrate threat intelligence that you get from your intelligence team or a third-party provider. This can then also be compared to your current detection or visibility coverage.
DeTT&CT administrates all this information within different YAML files, and a scoring table is provided to have a standardized way of scoring your data quality, visibility, and detection. A Python tool is used (dettect.py) to generate all kind of output:
- ATT&CK Navigator layer files
- Excel files
- Graphs
For example, DeTT&CT can generate a layer file for the ATT&CK Navigator, which shows you your visibility and detection coverage, or techniques and software used by certain threat actors.
Changelog v1.9
- DeTT&CT now supports Mobile data sources which are introduced in MITRE ATT&CK version 13.
Install && Use
Copyright (C) 2019 Marcus Bakker (Twitter: @bakk3rm) and Ruben Bouman (Twitter: @rubenb_2)