DRAKVUF Sandbox v0.18.2 releases: automated hypervisor-level malware analysis system
DRAKVUF Sandbox
DRAKVUF Sandbox is an automated black-box malware analysis system with a DRAKVUF engine under the hood.
This project provides you with a friendly web interface that allows you to upload suspicious files to be analyzed. Once the sandboxing job is finished, you can explore the analysis result through the mentioned interface and get insight on whether the file is truly malicious or not.
Because it is usually pretty hard to set up a malware sandbox, this project also provides you with an installer app that would guide you through the necessary steps and configure your system using settings that are recommended for beginners. At the same time, experienced users can tweak some settings or even replace some infrastructure parts to better suit their needs.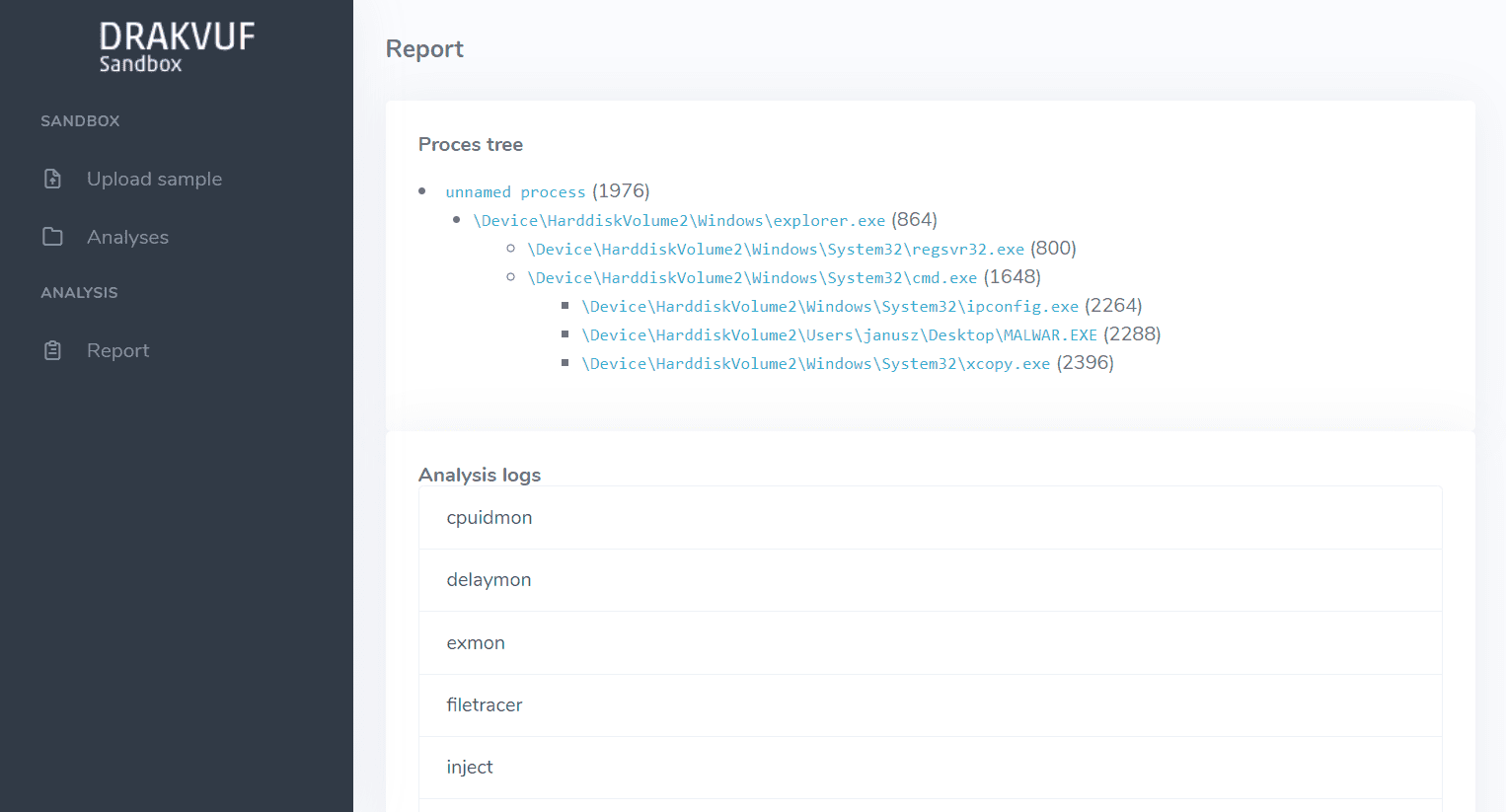
Supported hardware&software
In order to run DRAKVUF Sandbox, your setup must fullfill all of the listed requirements:
- Processor: Intel processor with VT-x and EPT features
- Host system: Debian 10 Buster/Ubuntu 18.04 Bionic/Ubuntu 20.04 Focal with at least 2 core CPU and 5 GB RAM
- Guest system: Windows 7 (x64), Windows 10 (x64; experimental support)
Nested virtualization:
- KVM does work, however it is considered experimental. If you experience any bugs, please report them to us for further investigation.
- Due to lack of exposed CPU features, hosting drakvuf-sandbox in cloud is not supported (although it might change in the future)
- Hyper-V does not work
- Xen does work out of the box
- VMware Workstation Player does work, but you need to check Virtualize EPT option for a VM; Intel processor with EPT still required
Install && Use
DRAKVUF (C) 2014-2020 Tamas K Lengyel






