[Defcon tool] Firmware Slap: Discovering vulnerabilities in firmware
Firmware Slap
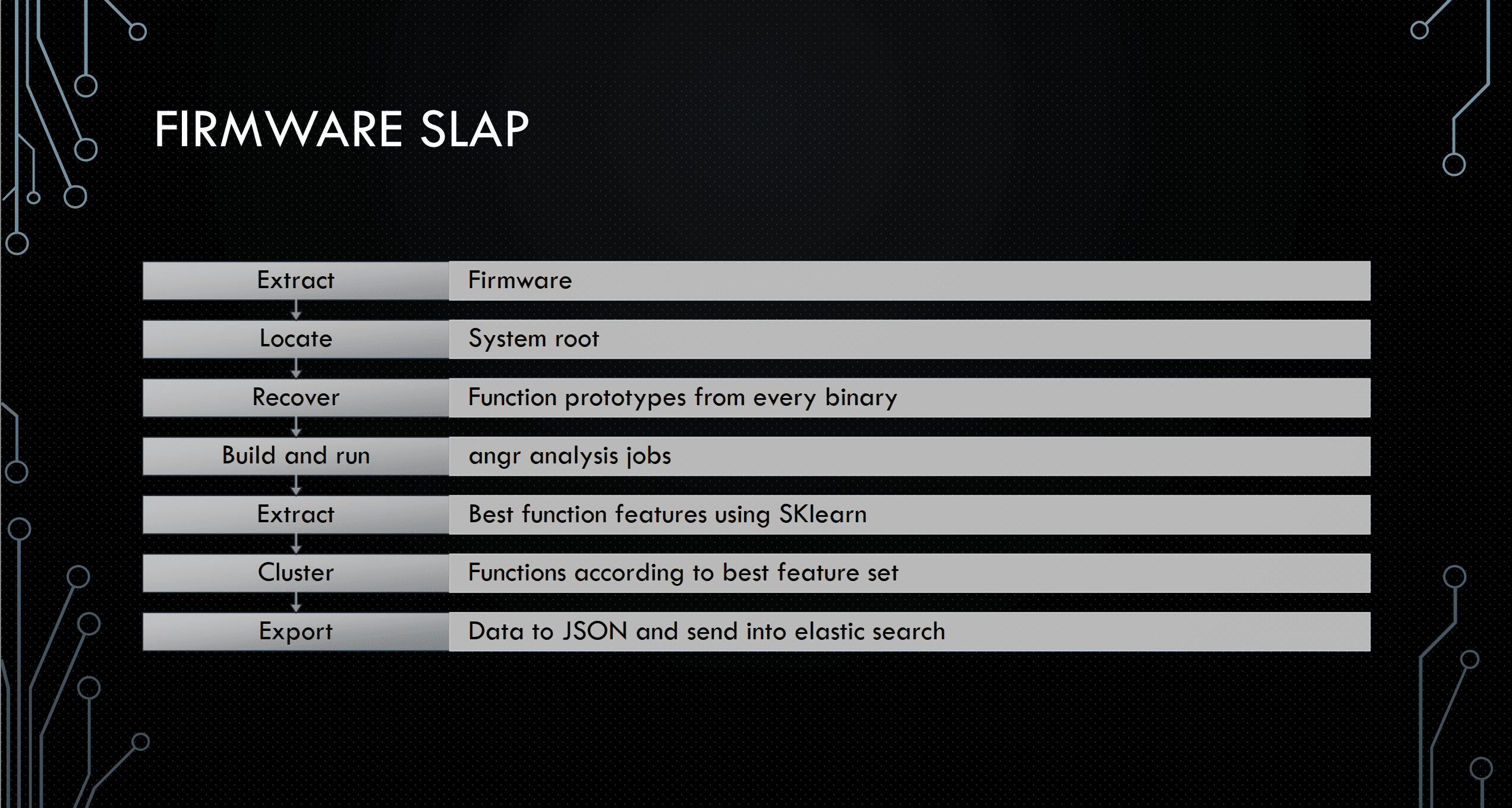
Firmware slap combines concolic analysis with function clustering for vulnerability discovery and function similarity in firmware. Firmware slap is built as a series of libraries and exports most information as either pickles or JSON for integration with other tools.
Install
git clone
Firmware slap should be run in a virtual environment. It has been tested on Python3.6
sudo apt install python3-virtualenv
virtualenv -p python3 fwslap
source fwslap/bin/activate
cd ~
mkdir .virtualenvs
pip install virtualenv
which virtualenv #note path warnings
pip install virtualenvwrapper
echo “export PATH=$PATH:~/.local/bin” >> ~/.bashrc
echo “export WORKON_HOME=~/.virtualenvs” >> ~/.bashrc
echo “source ~/.local/bin/virtualenvwrapper.sh” >> ~/.bashrc#usually best here to open new terminal
mkvirtualenv fwslap -p /usr/bin/python3
workon fwslappython setup.py install
You will need rabbitmq, docker, and (radare2 or Ghidra)
# Ubuntu
sudo apt install rabbitmq-server docker.io
# OSX
brew install rabbitmq# Radare2
git clone https://github.com/radare/radare2.git
sudo ./radare2/sys/install.sh
# Ghidra
wget https://ghidra-sre.org/ghidra_9.0.4_PUBLIC_20190516.zip
unzip ghidra_9.0.4_PUBLIC_20190516.zip -d ghidra
echo “export PATH=\$PATH:$PWD/ghidra/ghidra_9.0.4/support” >> ~/.bashrc
Quickstart
Use
# Get the firmware used for examples
wget https://firmware.securifi.com/AL3_64MB/AL3-R024-64MB
binwalk -Mre AL3-R024-64MB
Start a celery work from the project root directory:
# In a separate terminal
celery -A firmware_slap.celery_tasks worker –loglevel=info
In a different terminal window, run a vulnerability discovery job.
The returned vulnerability object
The above command will return an object in the result variable. This is a dictionary will all sorts of awesome information about vulnerability. There are three major keys in the object: The function arguments, The memory, and the injected location.
args
The args key will detail information about the recovered argument and what the argument values must be to recreate the vulnerability. In the below example, one argument is recovered, and to trigger the command injection that argument must be a char* that contains “`reboot`” to trigger a reboot.
Memory
The memory component of the object keeps track of the required memory values set to trigger the vulnerability. It also offers stack addresses and .text addresses with the offending commands for setting the required memory constraints. The first memory event required is at mtd_write_firmware+0x0 and the second is at mtd_write_firmware+0x38. Assembly is provided to help prettify future display work.
Command Injection Specific
Since command injections are the easiest to demo, I’ve created a convenience dictionary key to demonstrate the location of the command injection easily.
Sample Vulnerability Cluster Script
The vulnerability cluster script will attempt to discover vulnerabilities using the method in the Sample Vulnerability Discovery script and then build k-means clusters of a set of given functions across an extracted firmware to find similar functions to vulnerable ones.
$ Vuln_Cluster_Celery.py -h
usage: Vuln_Cluster_Celery.py [-h] [-L LD_PATH] [-F FUNCTION] [-V VULN_PICKLE]
Directory
positional arguments:
Directory
optional arguments:
-h, --help show this help message and exit
-L LD_PATH, --LD_PATH LD_PATH
Path to libraries to load
-F FUNCTION, --Function FUNCTION
-V VULN_PICKLE, --Vuln_Pickle VULN_PICKLE
The below command takes -F as a known vulnerable function. -V as a dumped pickle from a previous run to not need to discover new vulnerabilities and -L for the library path. A sample usage:
Copyright (C) 2019 ChrisTheCoolHut