getaltname v4.2.3 releases: Extract subdomains from SSL certificates in HTTPS sites
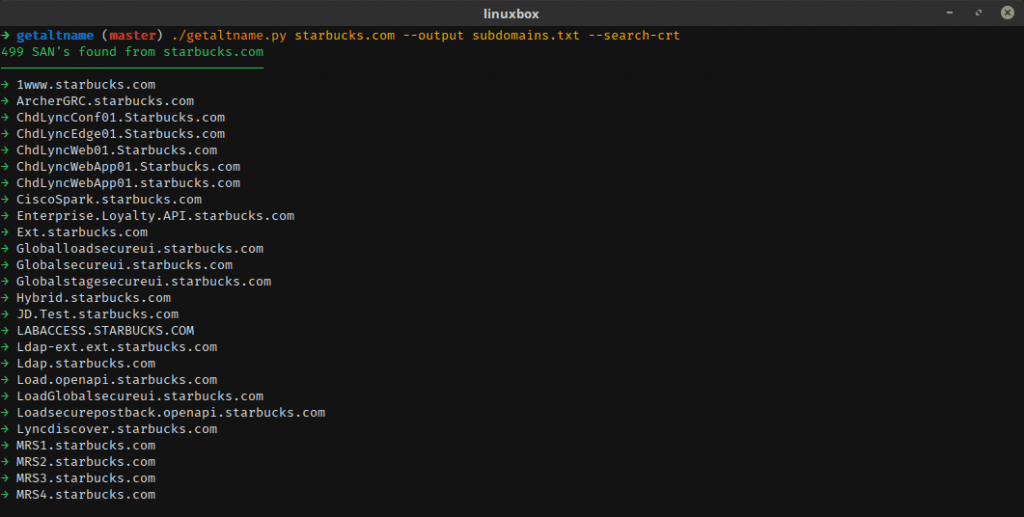
GetAltName (or GAN) is a tool that can extract Subject Alternative Names found in SSL Certificates directly from HTTPS websites which can provide you with DNS names (subdomains) or virtual servers.
This code extract subdomain names from https sites and return a list or json output of its findings. It is not a subdomain brute-force tool, and you can actually find those subdomains manually, this tool is about the automation of that process, it also offers the following features:
- Input a host or Nmap XML file to scan and return subdomains.
- List or JSON output, useful if you want to export data into other tools.
- You can optionally filter out domain names that don’t match the domain name that you’re analyzing.
- Copy to your clipboard the domain names as a list or string if you don’t want to deal with files, this is also useful for tools that don’t accept file input.
Features
- File output
- Output to clipboard
- Clean sub-domains wildcards
- Remove duplicates
- A filter system for the main domain and TLD’s.
- Add colors (so l33t. /s)
- Get additional sub-domains from crt.sh
- Read Nmap XML and analyze them
- JSON Output
- Unit Tests
Changleog v4.2.3
- Improved parsing when reading from a text file
- Fixed bug where you cannot input dashes in hostnames
- Changed the display output from columns to a vertical list to improve readability when scanning multiple hosts
- Other minor changes
Installation
$ git clone https://github.com/franccesco/getaltname.git
$ pip install -r requirements.txt
Usage
Demo
Copyright (c) [2018] [Franccesco Orozco]
Source: https://github.com/franccesco/







