linux-smart-enumeration v4.10 releases: Linux enumeration tools for pentesting and CTFs
linux-smart-enumeration
Linux enumeration tools for pentesting and CTFs
This project was inspired by LinEnum and uses many of its tests.
Unlike LinEnum, lse tries to gradually expose the information depending on its importance from a privesc point of view.
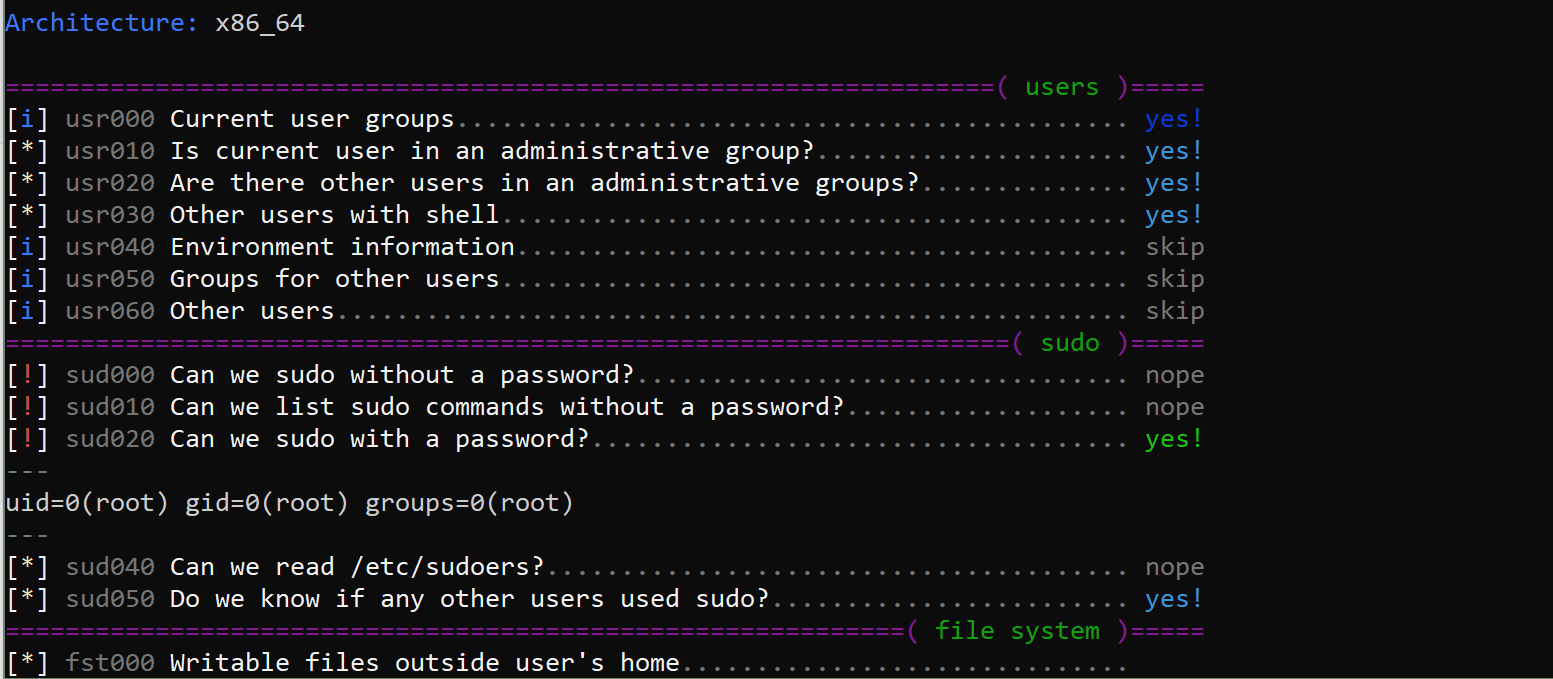
This script will show relevant information about the security of the local Linux system.
It has 3 levels of verbosity so you can control how much information you see.
In the default level, you should see the highly important security flaws in the system. Level 1 (./lse.sh -l1) shows interesting information that should help you to privesc. The level 2 (./lse.sh -l2 ) will just dump all the information it gathers about the system.
By default, it will ask you some questions: mainly the current user password (if you know it 😉 so it can do some additional tests.
Changelog v4.10
- Some bugfixes and minor improvements.
Download
git clone https://github.com/diego-treitos/linux-smart-enumeration.git
Use
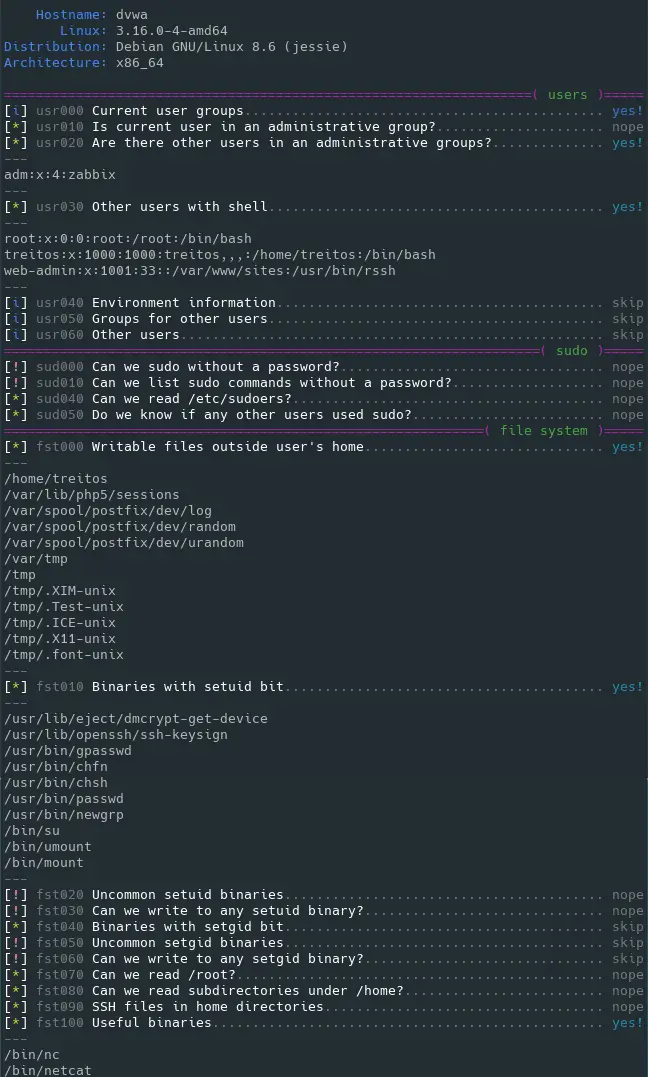
The idea is to get the information gradually.
First, you should execute it just like ./lse.sh. If you see some green yes!, you probably have already some good stuff to work with.
If not, you should try the level 1 verbosity with ./lse.sh -l1 and you will see some more information that can be interesting.
If that does not help, level 2 will just dump everything you can gather about the service using ./lse.sh -l2. In this case ,you might find useful to use ./lse.sh -l2 | less -r.
You can also select what tests to execute by passing the -s parameter. With it, you can select specific tests or sections to be executed. For example ./lse.sh -l2 -s usr010,net,pro will execute the test usr010 and all the tests in the sections net and pro.
Copyright (C) 2019 Diego-treitos






