McAfee: Honeybee, a Malicious Document Campaign Targeting Humanitarian Aid Groups
According to a blog post published by McAfee, a cyber-security vendor headquartered in Santa Clara, California, on Friday, McAfee’s threat team uncovered a phishing campaign targeting the Humanitarian Aid Groups And used the political topic of North Korea as a bait to lure victims to open malicious Microsoft Word documents. Based on the name of the malicious file used in the attack, McAfee named the event “Honeybee.”
The phishing email from this activity exists in two forms, one with malicious documents as attachments and the other with links to download malicious documents. The malicious document contains a Visual Basic macro that is designed to remove and execute a new version of the SYSCON backdoor. This version of SYSCON first appeared in 2017, and Trend Micro researchers pointed out in October last year that SYSCON’s backdoor is being spread through malicious documents that cover North Korea and parts of the Red Cross and World Health Organization personnel.
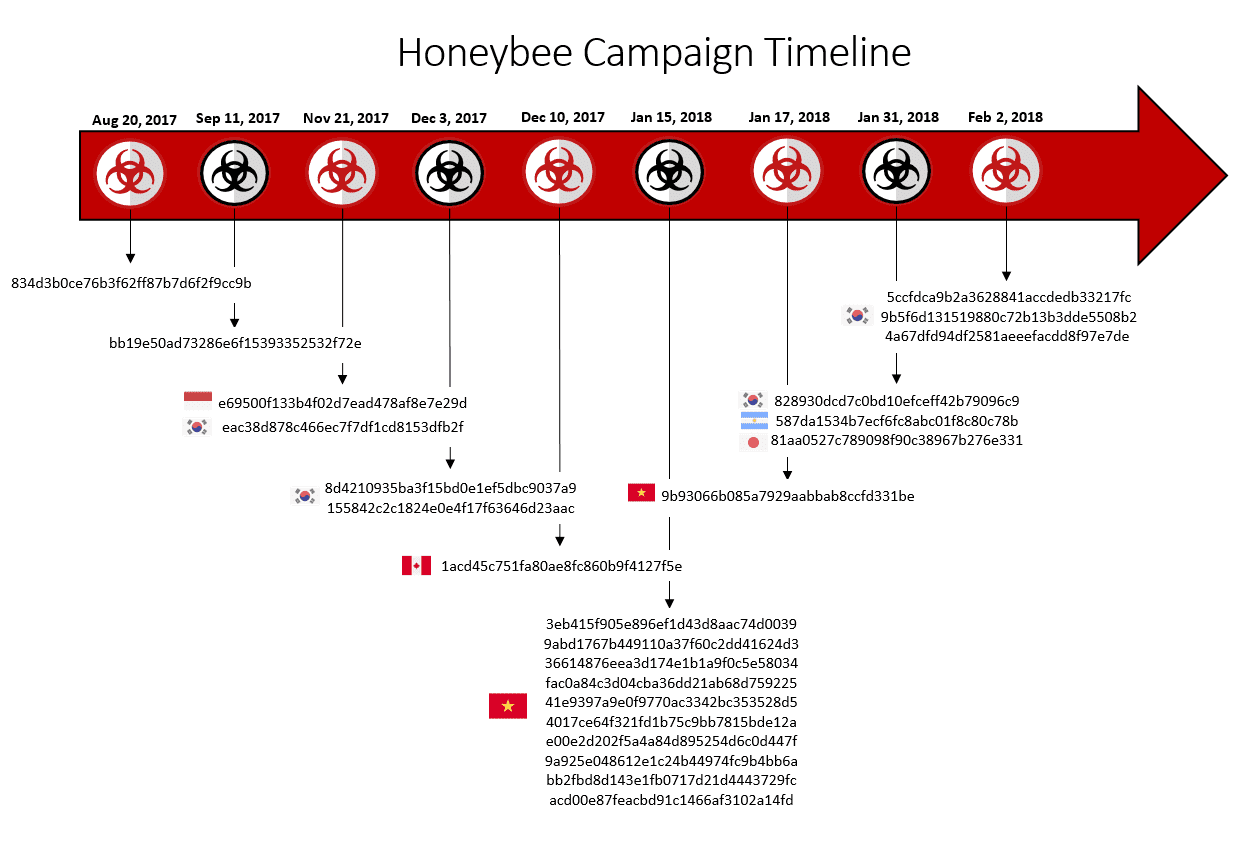
McAfee pointed out that malicious Visual Basic scripts use unique keys (custom letters) to encode data, consistent with previous SYSCON-based attacks. This approach is also used for Honeybee activities and appears to be in use since August 2017. The malware allows attackers to upload files to the server and download files to the infected system and execute them.
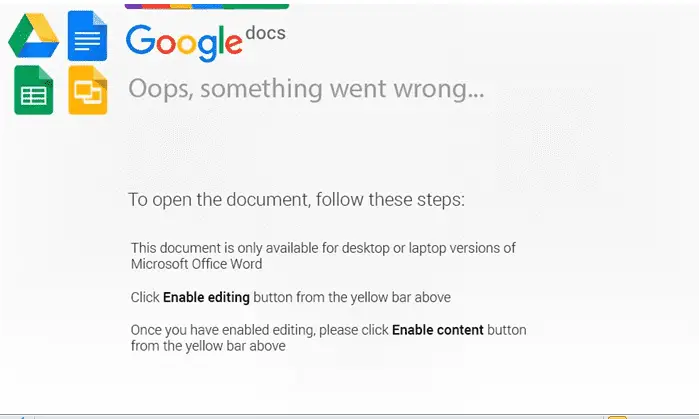
Malicious documents appear as fake Google Docs or Microsoft Office messages instructing recipients to enable editing and content to access information. If the recipient chooses to do so, they execute malicious code and download the malware onto their device.
 A few additional documents appeared between January 17 and February 3, but still contained the same Visual Basic macro code and the same author name. Some malicious documents have been verified that they do not contain malicious code, McAfee believes they are likely to be used for testing.
A few additional documents appeared between January 17 and February 3, but still contained the same Visual Basic macro code and the same author name. Some malicious documents have been verified that they do not contain malicious code, McAfee believes they are likely to be used for testing.
Most of these documents were submitted from South Korea, suggesting that the malware developer is likely to be Korean. The author of the document entitled “Windows User” created a related malicious document on January 12 containing a different encoding key, but actually used the same macro and same payload as the Honeybee document.
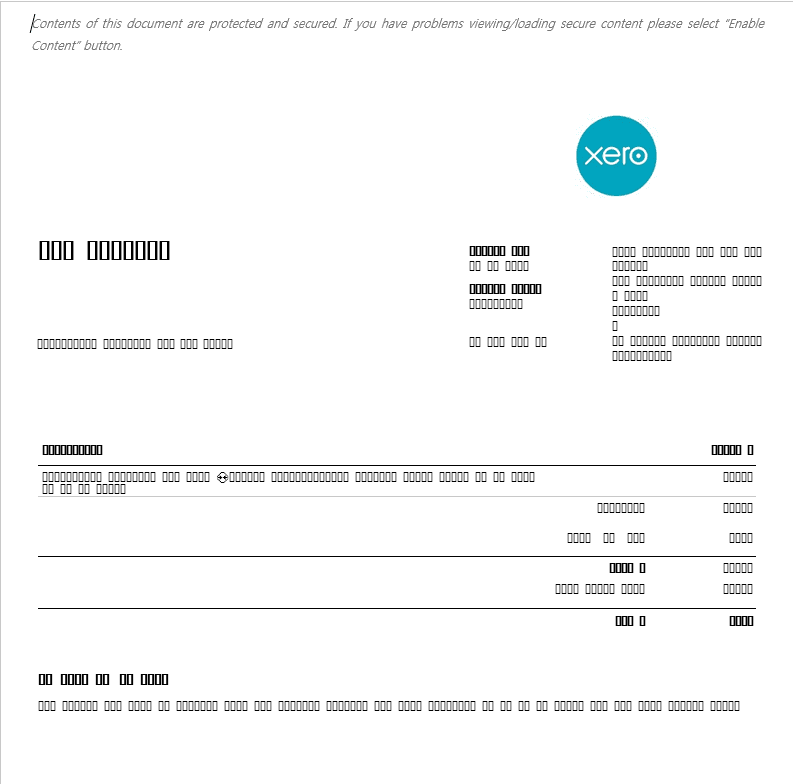
In addition to finding malicious documents, McAfee discovered a Win32-based executable. This is a dropper, using a digital signature stolen from Adobe Systems. It masquerades as a Word document icon, and once executed, opens a decoy file instructing the victim to enable the content to access the information. Bait documents attacked the use of the cloud-based accounting software company Xero:
McAfee said the techniques used to decoy files in Honeybee activities, such as luring messages, were mostly observed in South Korea. Now, this activity is clearly expanding beyond Korea and with Vietnam, Singapore, Argentina, Japan, Indonesia and Canada as the main goals. The bait paper, themed mainly on North Korea’s political issues, shows that those from those countries who are involved in humanitarian aid and North Korea and South Korea will be their main targets.
Source: McAfee







