Network Flight Recorder v1.12 releases releases: score network traffic and flag anomalies
Network Flight Recorder
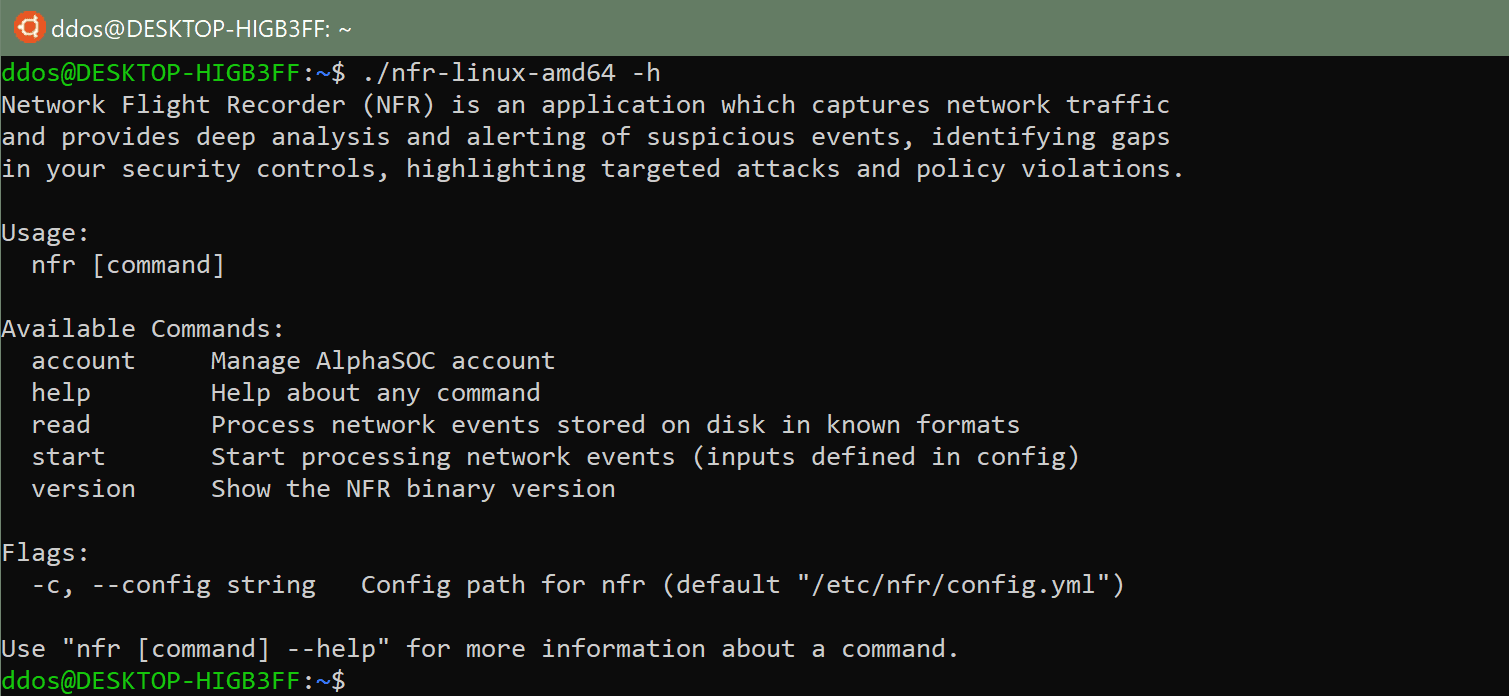
NFR is a lightweight application which processes network traffic using the AlphaSOC Analytics Engine. NFR can monitor log files on disk (e.g. Microsoft DNS debug logs, Bro IDS logs) or run as a network sniffer under Linux to score traffic. Upon processing the data, alerts are presented in either JSON or CEF format for escalation via syslog.
The AlphaSOC Analytics Engine performs deep investigation of the material, such as:
- Volumetric and quantitative analysis (counting events, identifying patterns)
- Resolving FQDNs and domains to gather context (identifying sinkholes and ASN values)
- Breakdown and analysis of each FQDN label (i.e. hostname, domain, TLD)
- Gathering of reputation data (e.g. WHOIS and associated malware samples)
- Categorization of traffic based on known patterns (e.g. C2, P2P, VPN, cryptomining)
Particular use cases solved by Network Behavior Analytics include:
- Uncovering C2 callbacks and traffic to known sinkholes
- Tor, I2P, and Freenet anonymized circuit identification
- Cryptomining and JavaScript cryptojacking detection
- Flagging traffic to known phishing domains
- Brand impersonation detection via Unicode homoglyphs and transpositions
- Flagging multiple requests for DGA domains, indicating infection
- DNS and ICMP tunneling and exfiltration detection
- Alerting of lateral movement and active network scanning
- Policy violation flagging (e.g. third-party VPN and P2P use)
NFR expects to find its configuration file in /etc/nfr/config.yml. You can find an example config.yml file in the repository’s root directory. The file defines the AlphaSOC Analytics Engine location and configuration, input preferences (e.g. log files to monitor), output preferences, and other variables. If you already have the AlphaSOC API key, update the file with your key and place it within the /etc/nfr/ directory.
If you are a new user, simply run the nfr account register to create the file and generate an API key, e.g.
Changelog v1.12
- eb477f1 Use fixed version of goreleaser
Use