progpilot v1.0.2 releases: A static analysis tool for security
progpilot
A static analyzer for security purposes – Only PHP language is currently supported.
Changelog v1.0.2
- Fix new bug reported in #44
- update dependencies
Use
- Download the latest phar archive in releases folder (or builds folder for dev versions).
- Optional: configure your analysis with a yaml file.
- Optional : use the up-to-date security files configuration in package/src/uptodate_data folder.
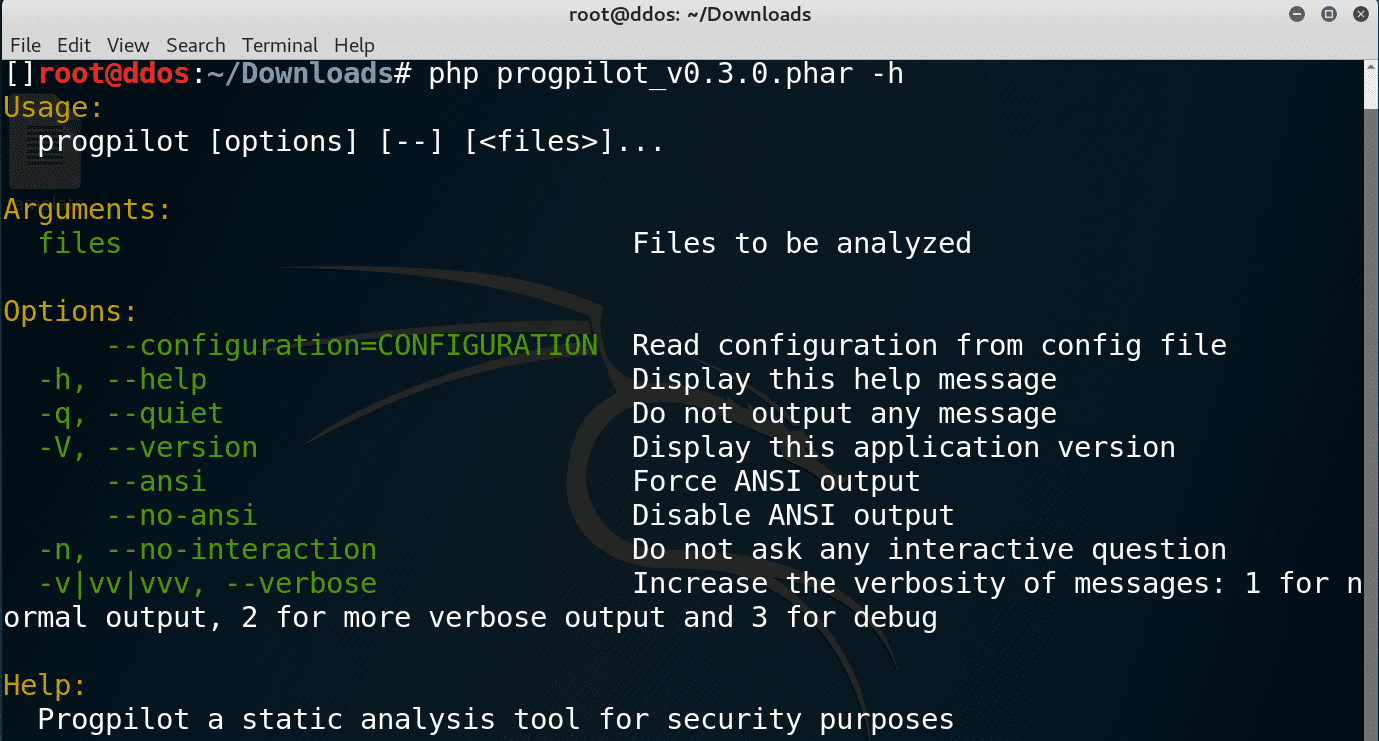
- Progpilot takes two optional arguments :
- your YAML configuration file (if not the default configuration will be used)
- your files and folders that have to be analysed
Library installation
Use getcomposer to install progpilot.
Your composer.json looks like this one :
Then run composer :
composer install
Then you could try the following example.
Library example
- For more information: look at the chapter about API explaination
- Use this code to analyze source_code1.php :
- When source_code1.php contains this code :
- The simplified output will be :
All files (composer.json, example1.php, source_code1.php) used in this example are in the projects/example folder.
For more examples look at this page
Copyright (c) 2017 Eric Therond <designsecurity.org>





