QRLJacking v2.1.1 releases – social engineering attacks vectors
What is QRLJacking?
QRLJacking or Quick Response Code Login Jacking is a simple social engineering attack vector capable of session hijacking affecting all applications that rely on the “Login with QR code” feature as a secure way to login into accounts. In a nutshell, the victim scans the attacker’s QR code which results in session hijacking.
What are the requirements to achieve a successful QRLJacking attack?
The QRLJacking attack consists of two sides:
- Server Side: A server-side script is needed to serve and shape the final look to the victim.
- Client Side: Cloning the QR Code and pushing it to the phishing page.
Process attack QRLJacking
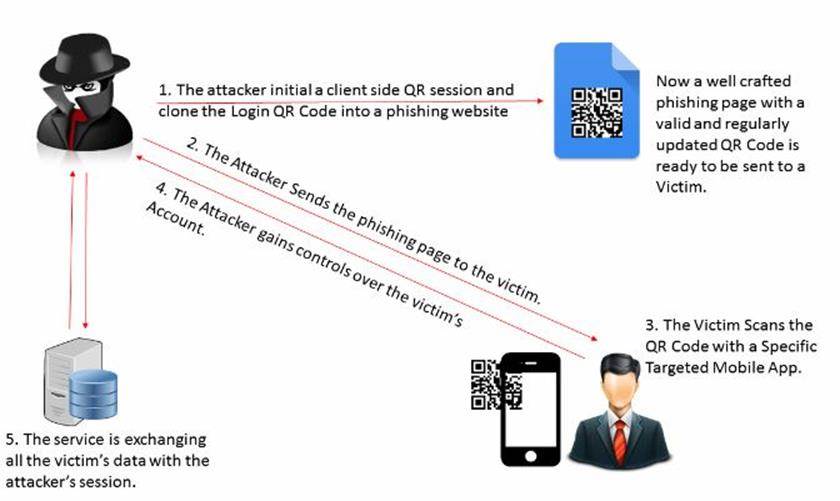
Here’s how the attack works secretly QRLJacking:
- Forward initializes QR-session on the client side and clones QR-code to enter the phishing website “is now correctly set up a phishing page with current and regularly updated QR-code ready to be sent to the victim.”
- The attacker sends a phishing page victims (many effective attack vector will be explained later in this article).
- Victims browse QR-code with a special target mobile application.
- An attacker gains control of the account the victim’s account.
- Service exchanges data with the victim’s session attacker.
QRLJacking attack gives hackers the ability to use the script full abduction account on a vulnerable input with the function of the QR-code, which, in effect, results in the theft of accounts and harm to reputation.
When the attacker receives the data, which we discussed in “Disclosure”, some of these data are used to communicate with the service server to find out some information about the user, which can be used later in the user application. Unfortunately, sometimes sharing of data occurs over an insecure network connection, allowing for easy control of an attacker, giving him the opportunity to modify or even delete the transmitted data.
Vulnerable Web Applications and Services
There are a lot of well-known web applications and services which were vulnerable to this attack until the date we wrote this paper. Here are some examples (that we have reported) including, but not limited to:
Chat Applications:
WhatsApp, WeChat, Line, Weibo, QQ Instant Messaging
Mailing Services:
QQ Mail (Personal and Business Corporate), Yandex Mail
eCommerce:
Alibaba, Aliexpress, Taobao, Tmall, 1688.com, Alimama, Taobao Trips
Online Banking:
AliPay, Yandex Money, TenPay
Passport Services “Critical”:
Yandex Passport (Yandex Mail, Yandex Money, Yandex Maps, Yandex Videos, etc…)
Mobile Management Software:
AirDroid
Other Services:
MyDigiPass, Zapper & Zapper WordPress Login by QR Code plugin, Trustly App, Yelophone, Alibaba Yunos
Demo
https://www.youtube.com/watch?v=JCoPSdQvESc
Download && Use
Copyright (C) 2019






