Reversed Overtaking Kit: An HTTP response fuzzer
RevOK
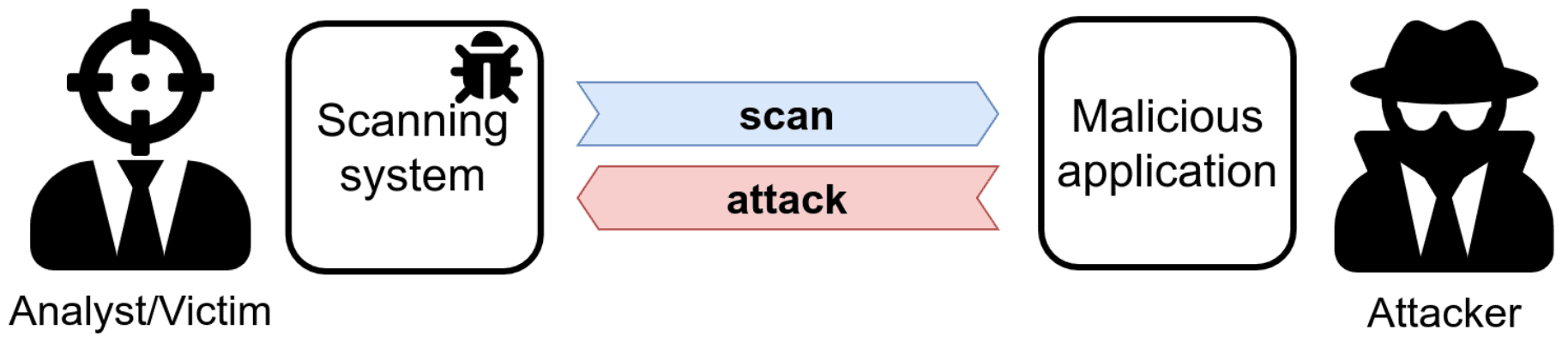
We see the targets of our scan as passive entities, and this leads to underestimating the risk of performing a scan. However, the tools we use to scan are not immune to vulnerabilities. Testing these bugs is often hard since they require a dedicated testing infrastructure: RevOK supports analysts by simulating a malicious target and by tracking data in the security scanner.
While the focus is on security scanners, RevOK can be used to test any software that takes (attacker-controlled) third-party data and displays it to a user (e.g., server-side REST API calls).
RevOK helped us to find two XSS to RCE bugs in Metasploit Pro[2] (CVE-2020-7354 and CVE-2020-7355), as well as many other vulnerabilities. We described this technique in our paper “Never Trust Your Victim: Weaponizing Vulnerabilities in Security Scanners”, accepted at RAID 2020.
How to cite us
RevOK implements the automatic testing methodology presented in “Never Trust Your Victim: Weaponizing Vulnerabilities in Security Scanners”.
Why RevOK?
In short, RevOK makes scanners explode.
This is somewhat of an obscure reference from the 1981 movie Scanners [4].
Private military company ConSec recruits “scanners” – super-powered individuals capable of telepathy and psychokinesis – and uses them in service of the company. However, when one of ConSec’s scanners demonstrates his powers at a marketing event, the volunteer – Darryl Revok – turns out to be a more powerful scanner, who causes the ConSec scanner’s head to explode.
Install & Use
Copyright (C) 2020 AvalZ