xnumon v0.1.7.2 releases: monitor macOS for malicious activity
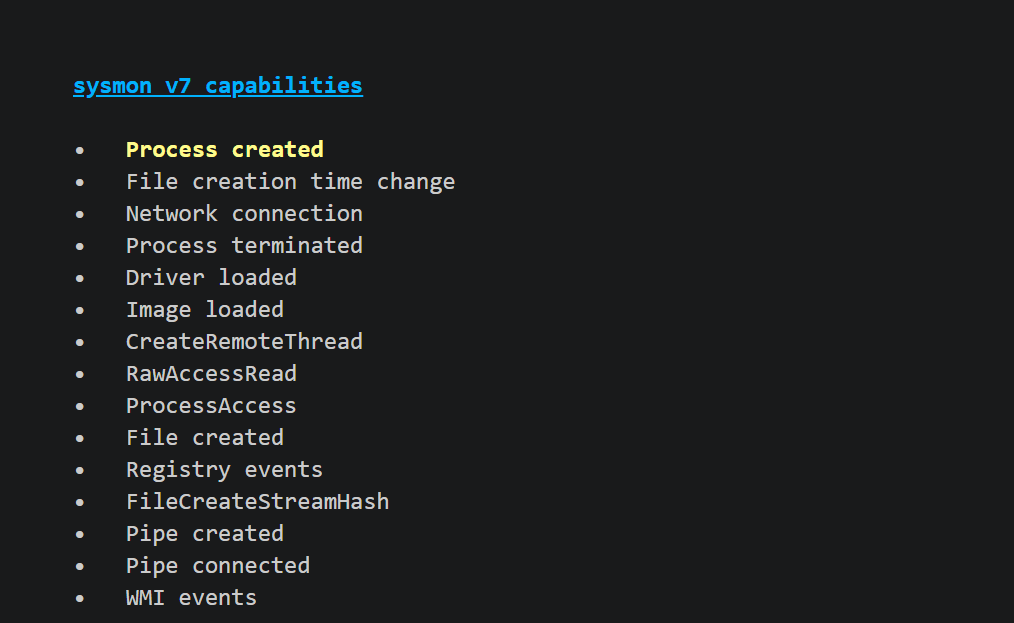
xnumon is a monitoring agent that produces system activity logs intended to be suitable for monitoring potentially large fleets of macOS systems for malware and intrusions. It aims at providing similar capabilities on macOS that sysmon provides on Windows.
Currently implemented are the following log events:
- xnumon-ops[0] and xnumon-stats[1]: for in-band monitoring of agent status and activity metrics. *
- image-exec[2]: a process has replaced its executable image as a result of calling execve(2) or posix_spawn(2). *
- process-access[3]: a process has accessed and possibly manipulated another process using either task_for_pid or ptrace(2). *
- launchd-add[4]: a process has added or modified a launch daemon or launch agent plist. †
- socket-listen[5]: a process has started listening on a socket. *
- socket-accept[6]: a process has accepted an incoming connection. *
- socket-connect[7]: a process has initiated an outgoing connection. ‡
xnumon provides context information such as executable image hashes, code signature meta-data, script shebang handling, and the history of previous executable images that led to the current process state. It does so by tracking fork and other syscalls instead of relying only on the ppid, which can change over the lifetime of a process. For the reliable acquisition of image hashes even from short-living or self-modifying executables, xnumon comes with an optional kernel extension.
xnumon is configurable. It supports different log formats and hash algorithms. In order to reduce log volume close to the source, xnumon implements a number of suppression mechanisms and allows tuning the level of information per event. The logging subsystem was designed to be easy to extend with custom log drivers.
Kernel Extension
The xnumon kext is optional and provides reliable acquisition of image hashes and code signing information even for short-living images using the Kauth KPI. The kernel extension is currently unsigned and therefore cannot be deployed unless you own a kernel signing certificate. A kernel signing certificate for xnumon has been requested from Apple but has not been approved yet.
To load the unsigned kext for testing and development, you need to disable System Integrity Protection (SIP) for kexts. Reboot to repair mode by pressing cmd⌘+r during boot and from within the repair console, run csrutil enable –without kext. This will also turn off the kext user consent requirement of High Sierra.
Changelog v0.1.7.2
- Avoid calling file operations that would block while the kext is blocking processes during exec(2); this avoids deadlocking the system while long-running low-level disk operation are in progress, such as while Boot Camp Assistant is editing partitions or Disk Utility is running fsck.
- Drop support for OS X 10.11 El Capitan.
Installing
Copyright (c) 2017-2018, Daniel Roethlisberger
Source: https://github.com/droe/






