Category: Malware Analysis
MalwLess Simulation Tool (MST) MalwLess is an open source tool that allows you to simulate system compromise or attack behaviors without running processes or PoCs. The tool is designed to test Blue Team detections and...
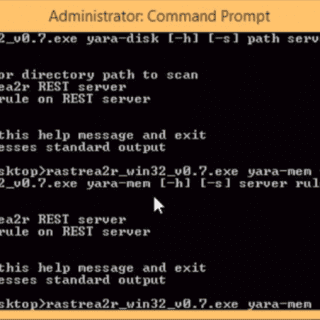
Ever wanted to turn your AV console into an Incident Response & Threat Hunting machine? Rastrea2r (pronounced “rastreador” – hunter- in Spanish) is a multi-platform open source tool that allows incident responders and SOC...
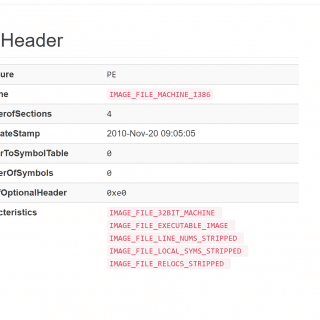
Manalyze A static analyzer for PE files Manalyze was written in C++ for Windows and Linux and is released under the terms of the GPLv3 license. It is a robust parser for PE files with...
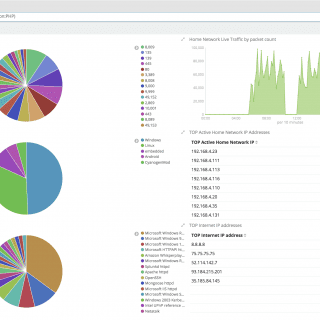
CHIRON is a home analytics based on ELK stack combined with Machine Learning threat detection framework AKTAION. CHIRON parses and displays data from P0f, Nmap, and BRO IDS. CHIRON is designed for home use...
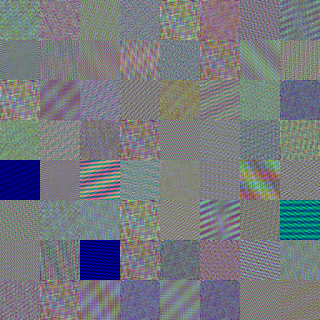
malwaregan Emulating malware authors for proactive protection using GANs over a distributed image visualization of dynamic file behavior. References to the code The WGAN-GP model trained is based on the code published at here....
EKTotal EKTotal is an integrated analysis tool that can automatically analyze the traffic of Drive-by Download attacks. The proposed software package can identify four types of Exploit Kits such as RIG and Magnitude, and...
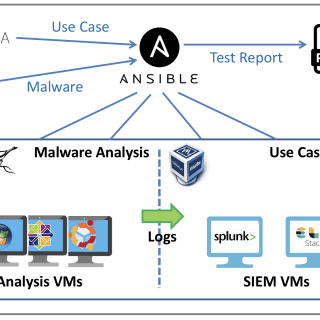
ypsilon Automated Use Case Testing Ypsilon is an Automated Security Use Case Testing Environment using real malware to test SIEM use cases in a closed environment. Different tools such as Ansible, Cuckoo, VirtualBox, Splunk, and ELK are combined to determine...
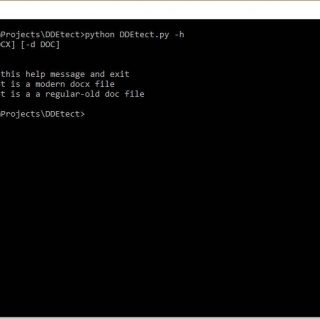
DDEtect Written by Amit Serper, @0xAmit DDEtector is a simple DDE object detector written in python Currently supports only word DOCX and legacy DOC files Prints the contents of the DDE payloads (Note: In some cases,...
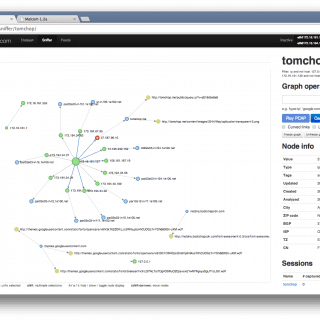
Malcom – Malware Communication Analyzer Malcom is a tool designed to analyze a system’s network communication using graphical representations of network traffic, and cross-reference them with known malware sources. This comes in handy when...
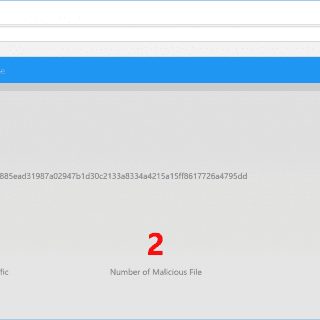
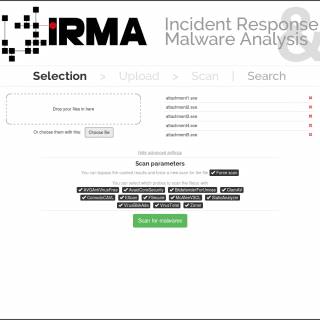
IRMA: Incident Response & Malware Analysis IRMA is an asynchronous and customizable analysis system for suspicious files. This repository is a subproject of IRMA and contains the source code for IRMA’s Frontend, which is...
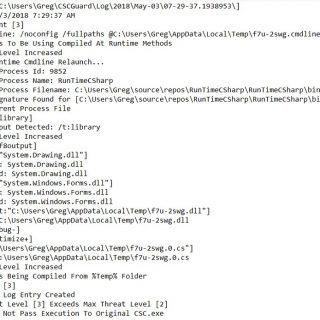
CSCGuard Protects and logs suspicious and malicious usage of .NET CSC.exe and Runtime C# Compilation Features Able to detect and prevent runtime C# compilation used by malware even when “GenerateInMemory” is used Limited Heuristic...
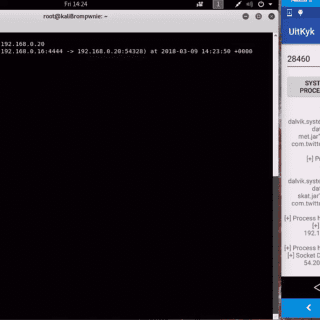
Uitkyk is a framework that allows you to identify Android malware according to the instantiated objects on the heap for a specific Android process. Uitkyk scans the heap of a specific Android process using...
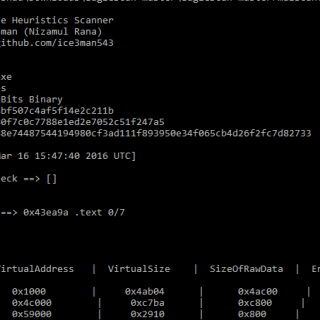
MalScan MalScan is a simple PE File Heuristics Scanners written in python that you can use to quickly analyze a PE file and find out whether anything suspicious exists. It is a simple tool...
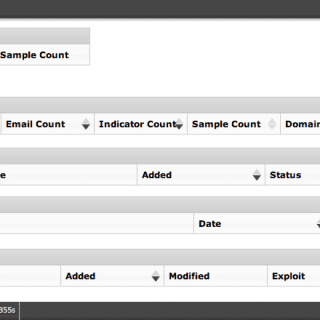
Collaborative Research Into Threats (CRITs) is a web-based tool which combines an analytic engine with a cyber threat database that not only serves as a repository for attack data and malware, but also provides...
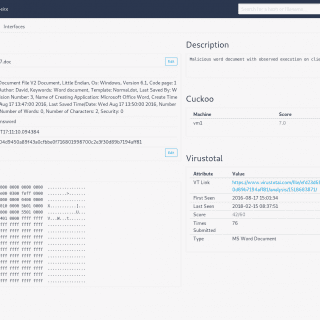
Introduction Snake is a malware storage zoo that was built out of the need for a centralized and unified storage solution for malicious samples that could seamlessly integrate into the investigation pipeline. Snake is...