HosTaGe v2.4 releases: Low Interaction Mobile Honeypot
HosTaGe – Honeypot-To-Go
HosTaGe is a lightweight, low-interaction, portable, and generic honeypot for mobile devices that aims at the detection of malicious, wireless network environments. As most malware propagates over the network via specific protocols, a low-interaction honeypot located at a mobile device can check wireless networks for actively propagating malware. We envision such honeypots running on all kinds of mobile devices, e.g., smartphones and tablets, to provide a quick assessment of the potential security state of a network.
HosTaGe emulates the following protocols as of the latest version: AMQP, COAP, ECHO, FTP, HTTP, HTTPS, MySQL, MQTT, MODBUS, S7COMM, SNMP, SIP, SMB, SSH, SMTP, and TELNET
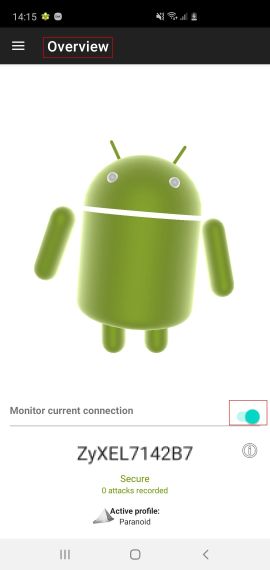
Overview
Starting the Honeypot Service
To start the honeypot service, the device must be connected to WiFi or to an LTE/4G Network. The current support for LTE/4G is minimal. The honeypot service of the app can be started from the home screen using the switch. By default, the “Paranoid” profile is started which emulates all the protocols in HosTaGe.
Attack States
The home screen of the app has an Android bot. The bot exhibits three states through animation which are:
- Safe (Cheerful Dancing)
- Under Attack! (Jumping in red with a bee)
- Infected Network (A vigil bot)
By default when the honeypot service is started on a new network, the android bot starts with a cheerful animation that suggests that the network is safe. The current state of the network can also be checked by double-tapping on the bot. On detecting an attack, the android bot starts to jump in a panic with a bee around it. This is to notify the user that an attack has been detected. The bot exhibits the panic mode for a detected attack for a period of 15 minutes. Following this period, the bot exhibits a warning animation that notifies the user that the network is infected. HosTaGe also stores the infected networks in its database so that the user is notified whenever the app is connected to an infected network.
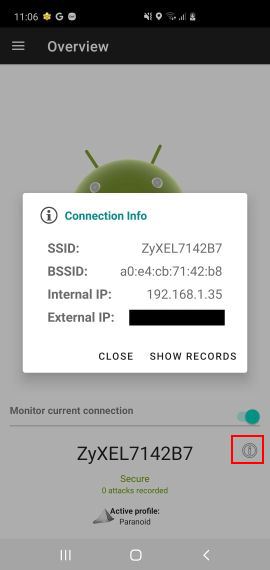
Connection Information
The information button on the overview screen provides information about the network name, network device MAC, local and external IP of the device.
Changelog v2.4
Features
#204 Remove unused Sync module and replace toasts
#193, #203 Pcap storage location and rotation
#202 UI adjustments
#178 Change color scheme
#179 Changes in Privacy Policy
#108 Location Permissions Update for Android 10 and 11
Bugs
#205 App crash on enabling HPFeeds and Multistage in Settings Fragment in v.2.4
#192 Change toasts to snack bars
#200 Crash on detecting an attack
#177 Location Permission and Storage Permission Flow
#191 Crash on click of attacks in home screen
#182 Change of the default profile on app launch
#183 Reordering of profiles in profile fragment
#181 Check toasts of Multistage and IP Tables
#189 General code housekeeping
Download & Use
Copyright (C) 2013-2020, Aalborg University (Denmark) and Technische Universität Darmstadt (Germany)