pwntools v4.11 releases: CTF framework and exploit development library
pwntools – CTF toolkit
Pwntools is a CTF framework and exploits the development library. Written in Python, it is designed for rapid prototyping and development and intended to make exploit writing as simple as possible.
There are bits of code everyone has written a million times, and everyone has their own way of doing it. Pwntools aims to provide all of these in a semi-standard way, so that you can stop copy-pasting the same struct.unpack(‘>I’, x) code around and instead use more slightly more legible wrappers like pack or p32 or even p64(…, endian=’big’, sign=True).
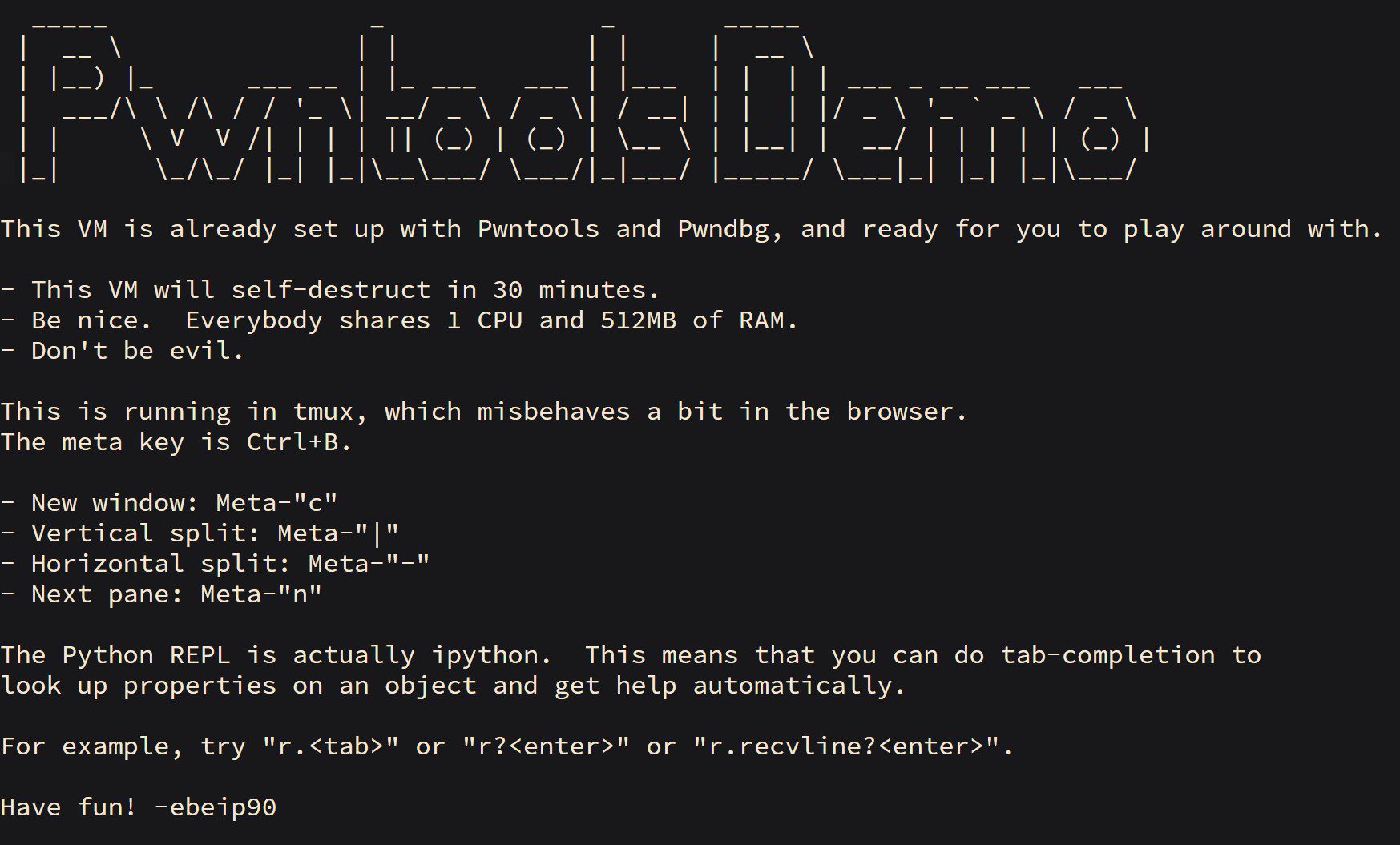
Aside from convenience wrappers around mundane functionality, it also provides a very rich set of tubes which wrap all of the IO that you’ll ever perform in a single, unifying interface. Switching from a local exploit to a remote exploit, or local exploit over SSH becomes a one-line change.
Last but not least, it also includes a wide array of exploitation assistance tools for intermediate-to-advanced use cases. These include remote symbol resolution given a memory disclosure primitive (MemLeak and DynELF), ELF parsing and patching (ELF), and ROP gadget discovery and call-chain building (ROP).
Changelog v4.11
- Make fmtstr module able to create payload without $ notation by @murph12F in #2185
- Add search for libc binary by leaked function addresses by @peace-maker in #2103
- Support for RISC-V 64-bit architecture by @Xeonacid in #2177
- ELF.nx and ELF.execstack enhancements by @yuvalpoliti in #2186
- Handle
context.newlinecorrectly intube.interactive()by @peace-maker in #2129 - Fix bug at ssh.py:
downloadanddownload_filewith relative paths by @goreil in #2214 - Fix ssh.process not setting ssh_process.cwd by @peace-maker in #2241
- Fix corefile module after pyelftools update by @peace-maker in #2261
- Lots of bug fixes and documentation improvements
Install & Use
Copyright (c) 2015 Gallopsled et al.






