Category: Penetration Testing
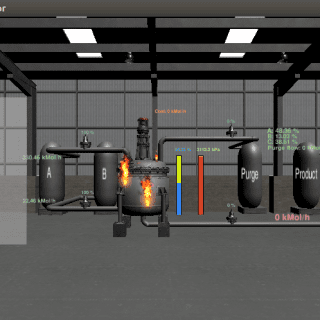
GRFICS GRFICS is a graphical realism framework for industrial control simulations that uses Unity 3D game engine graphics to lower the barrier to entry for industrial control system security. GRFICS provides users with a...
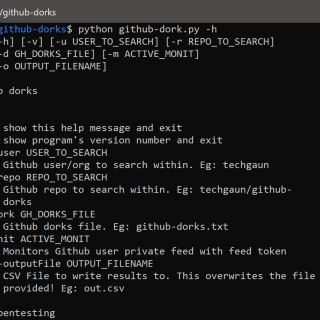
Github Dorks Github search is quite powerful and useful feature and can be used to search sensitive data on the repositories. Collection of github dorks that can reveal sensitive personal and/or organizational information such as...
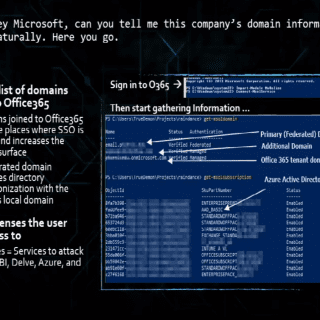
RainDance A toolkit for enumerating and collecting information from Office 365. Raindance uses built-in powershell modules, namely from the MSOnline & AzureAD powershell modules to log into Office 365 tenants with legitimate credentials and...
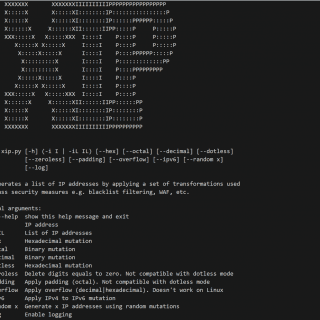
XIP XIP generates a list of IP addresses by applying a set of transformations used to bypass security measures e.g. blacklist filtering, WAF, etc. Below are the implemented transformations: Hexadecimal Decimal Octal IPV4 to...
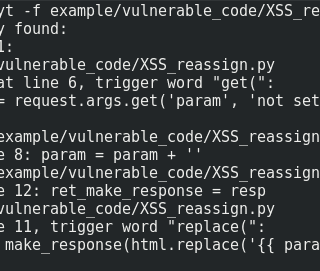
Python Taint Static analysis of Python web applications based on theoretical foundations (Control flow graphs, fixed point, data flow analysis) This report presents the static analysis too PyT which has been created to detect...
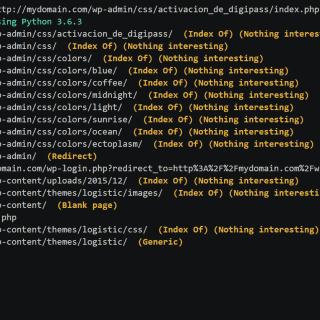
Dirhunt is a web crawler optimize for search and analyze directories. This tool can find interesting things if the server has the “index of” mode enabled. Dirhunt is also useful if the directory listing is not enabled....
JCS (Joomla Component Scanner) made for penetration testing purpose on Joomla CMS. JCS can help you with the latest component vulnerabilities and exploits. The database can update from several resources and a Crawler has...
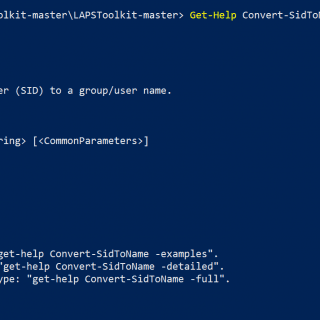
LAPSToolkit Functions are written in PowerShell that leverage PowerView to audit and attack Active Directory environments that have deployed Microsoft’s Local Administrator Password Solution (LAPS). It includes finding groups specifically delegated by sysadmins, finding...
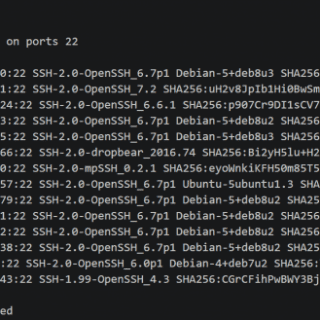
SSH Auditor The best way to scan for weak ssh passwords on your network Features ssh-auditor will automatically: Re-check all known hosts as new credentials are added. It will only check the new credentials....
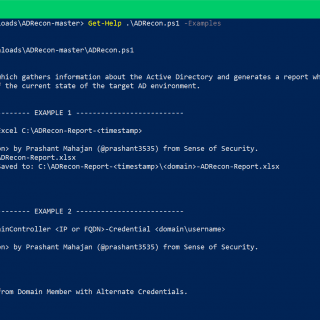
ADRecon: Active Directory Recon ADRecon is a tool which extracts and combines various artifacts (as highlighted below) out of an AD environment. The information can be presented in a specially formatted Microsoft Excel report...
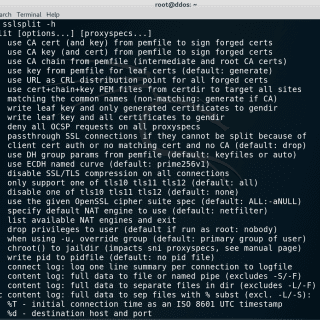
SSLsplit – transparent SSL/TLS interception Overview SSLsplit is a tool for man-in-the-middle attacks against SSL/TLS encrypted network connections. It is intended to be useful for network forensics, application security analysis, and penetration testing. SSLsplit...
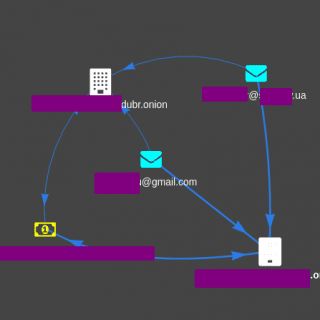
DOGE Darknet Osint Graph Explorer Still in dev, works right. You should use this in addition to Darknet OSINT Transform Download git clone https://github.com/pielco11/DOGE.git Pay attention here Query prototype: SELECT DISTINCT custom_column_name AS input, another_custom_name AS...
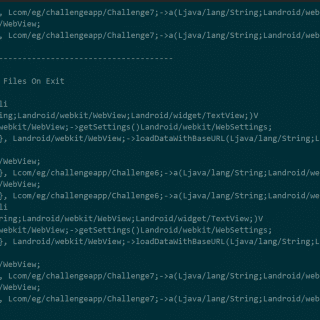
scrounger – a person who borrows from or lives of others. There is no better description for this tool for two main reasons, the first is because this tool takes inspiration from many other tools...
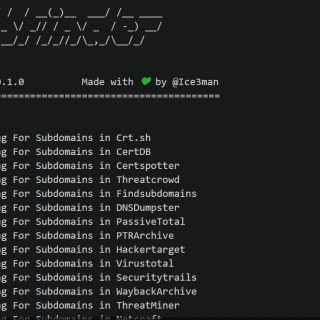
SubFinder SubFinder is a subdomain discovery tool that uses various techniques to discover massive amounts of subdomains for any target. It has been aimed at a successor to the sublist3r project. SubFinder uses Passive Sources,...
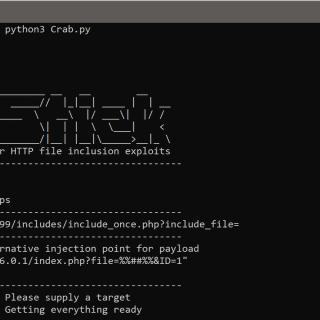
CrabStick Crabstick is an HTTP/HTTPS security vulnerability scanner that finds LFI/RFI (local and remote file inclusion) and tries to escalate this to gain a remote reverse shell. Crabstick’s is designed to handle, look and feel like...