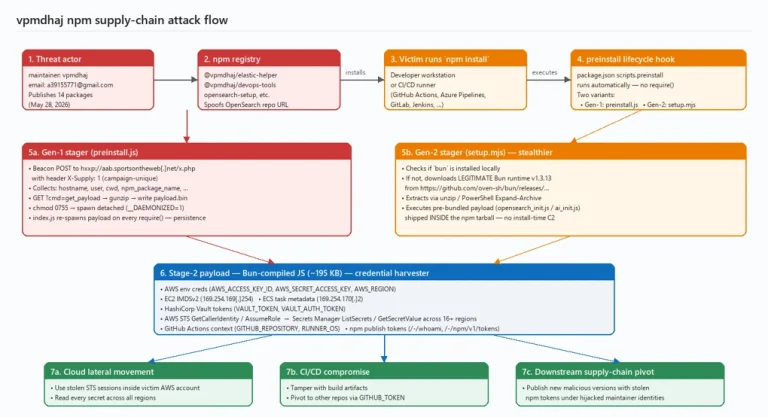
Urgent Alert for DevOps Engineers Microsoft security analysts recently identified an active threat vector targeting modern software...
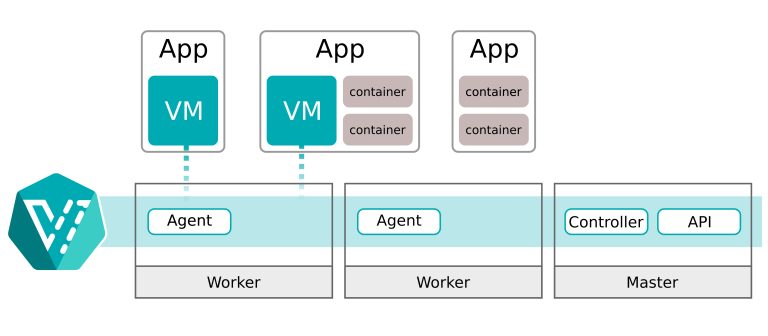
Security analysts have uncovered a severe security defect within cloud virtualization infrastructure. Specifically, the newly identified KubeVirt...
Following Google’s ostentatious declaration at Google I/O 2026 to embed artificial intelligence entirely into search, an unexpected...
The Samba Team has released urgent security patches to address multiple network infrastructure defects. Specifically, these new...
The Jenkins project recently released an urgent patch update addressing multiple security issues in its popular automation...
Google recently pushed a major software modification to its millions of global desktop users. Specifically, the technology...
GitLab has issued an urgent set of software modifications to safeguard development pipelines. Specifically, these new GitLab...
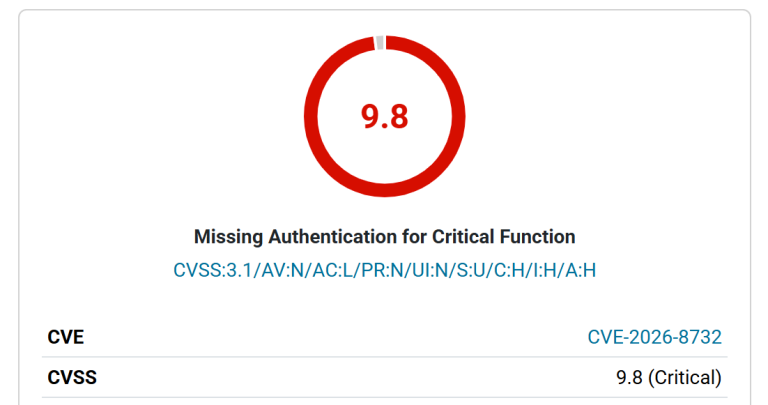
Synology has issued an urgent security alert for its enterprise communication platform. Specifically, the vendor released software...
Recently, a major security threat emerged within the WordPress ecosystem. Attackers are actively targeting a critical flaw...
Enterprise security teams do not usually replace email encryption because something dramatic happens overnight. They replace it...
IBM has issued an urgent security warning regarding a critical security loophole in an open-source artificial intelligence...
Security researchers recently discovered a severe security flaw in a popular virtual private network client. Specifically, developers...
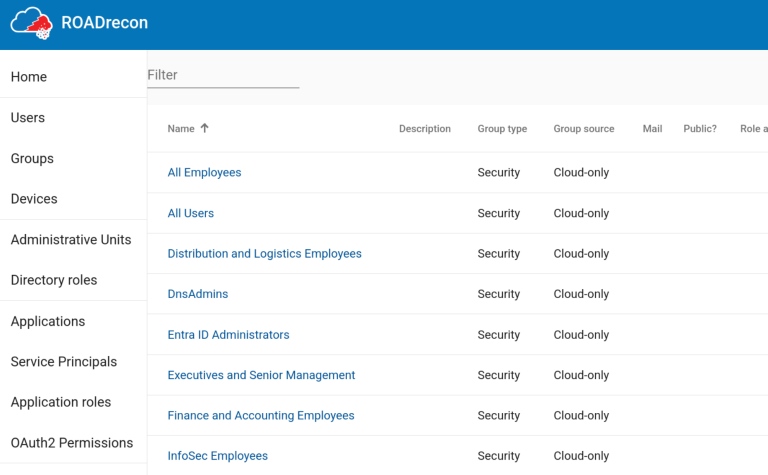
Security analysts have released a comprehensive analysis regarding specialized offensive tools in modern network breaches. Specifically, hackers...
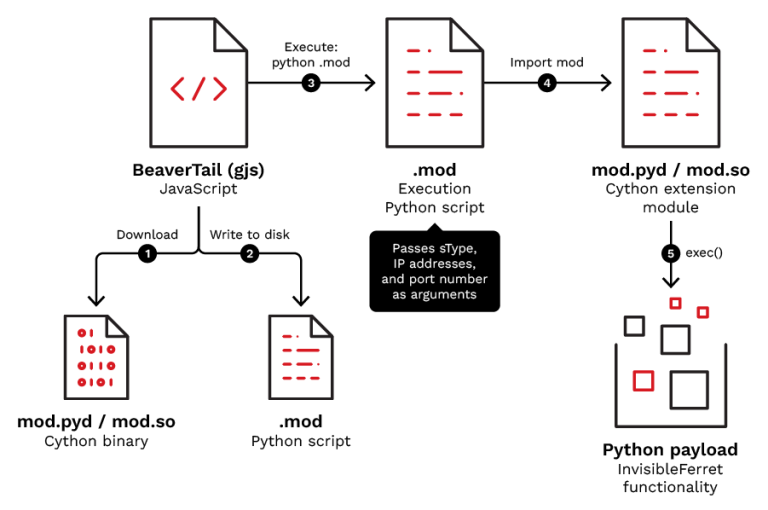
North Korea-aligned threat actors are updating their malicious toolsets to target software developers globally. Specifically, TrendAI Research...
Security researcher Asim Manizada recently published full technical details regarding a major security flaw in Linux systems....
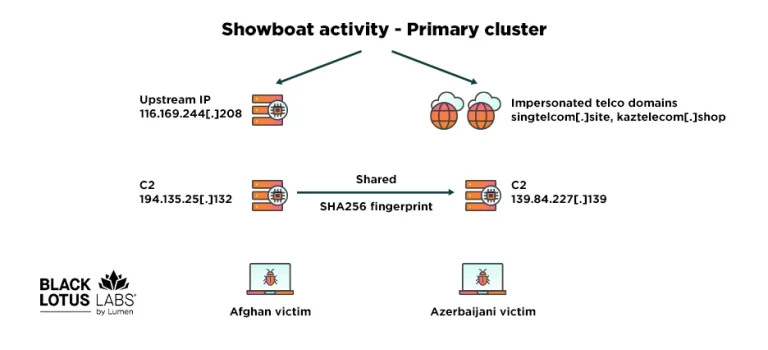
Threat researchers have exposed a stealthy cyber espionage tool targeting critical infrastructure. Specifically, Black Lotus Labs recently...
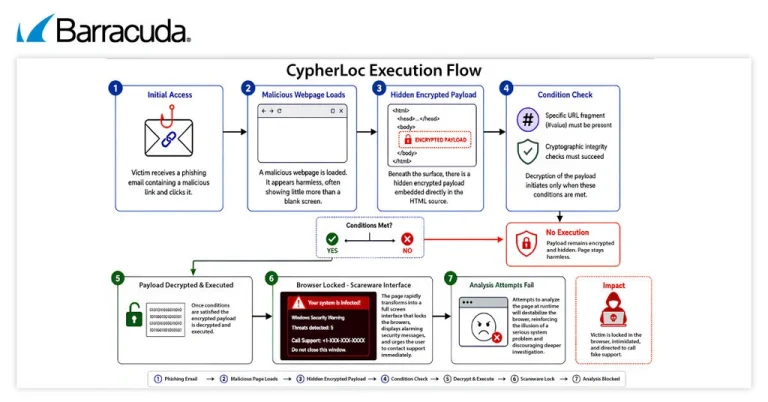
Threat intelligence experts have uncovered a massive browser-manipulation campaign active across the global digital landscape. Specifically, researchers...
Recently, numerous developers expressed profound dissatisfaction regarding the GPT-5.5 model. Specifically, they noted a perceptible degradation in...
A dangerous new cyber assault is currently targeting corporate infrastructure networks. Specifically, security researchers have uncovered a...