Category: Sniffing & Spoofing
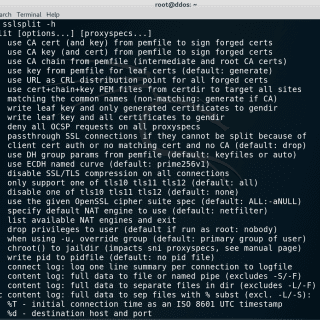
SSLsplit – transparent SSL/TLS interception Overview SSLsplit is a tool for man-in-the-middle attacks against SSL/TLS encrypted network connections. It is intended to be useful for network forensics, application security analysis, and penetration testing. SSLsplit...
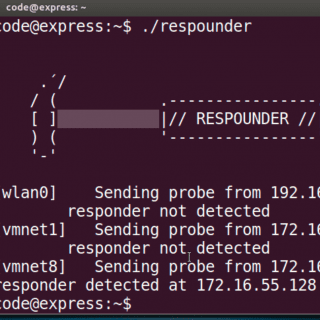
respounder A tool that detects the presence of a Responder in the network Identifies compromised machines before hackers run away with the loot (hashes) It sends LLMNR name resolution requests for made-up hostnames that do not...
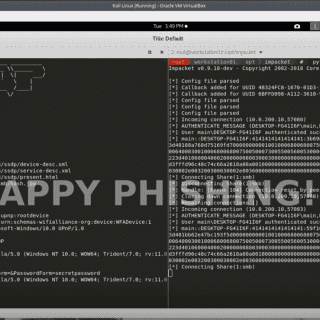
evil-ssdp This tool responds to SSDP multicast discovery requests, posing as a generic UPNP device. Your spoofed device will magically appear in Windows Explorer on machines in your local network. Users who are tempted...
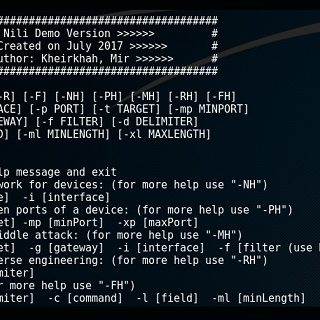
Nili is a Tool for Network Scan, Man in the Middle, Protocol Reverse Engineering, and Fuzzing. Prerequisites Python – Python Programming Language Scapy – Interactive Packet Manipulation Program Netzob – Protocol Reverse Engineering, Modeling and Fuzzing Installing...
ExchangeRelayX An NTLM relay tool to the EWS endpoint for on-premise exchange servers. Provides an OWA for hackers. Version 1.0.0. This tool is a PoC to demonstrate the ability of an attacker to perform...
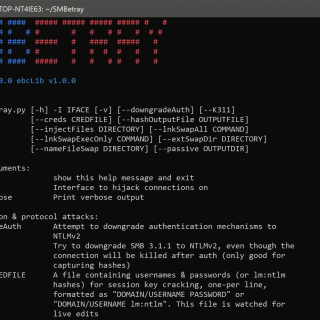
SMBetray SMB MiTM tool with a focus on attacking clients through file content swapping, lnk swapping, as well as compromising any data passed over the wire in cleartext. Version 1.0.0. This tool is a...
DNS Rebind Toolkit DISCLAIMER: This software is for educational purposes only. This software should not be used for illegal activity. The author is not responsible for its use. Don’t be a dick. DNS Rebind...
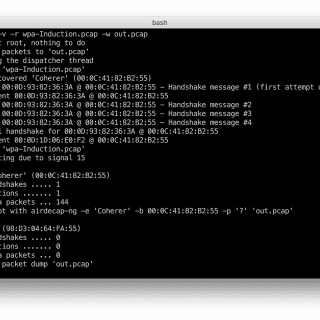
zizzania sniffs wireless traffic listening for WPA handshakes and dumping only those frames suitable to be decrypted (one beacon + EAPOL frames + data). In order to speed up the process, zizzania sends IEEE...
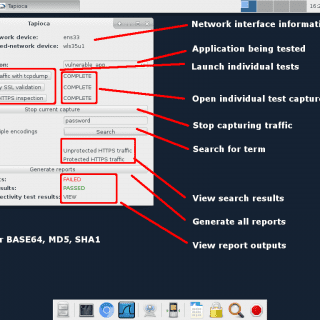
CERT Tapioca is a utility for testing mobile or any other application using MITM techniques. CERT Tapioca development was sponsored by the United States Army Armament Research, Development, and Engineering Center (ARDEC) as well...
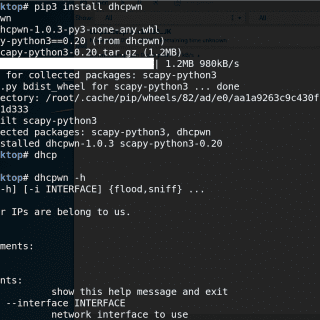
DHCPwn is a tool used for testing DHCP IP exhaustion attacks. It can also be used to sniff local DHCP traffic. Useful links: DHCP RFC1531 (obsolete) RFC1541 (obsolete) RFC2131 Bootstrap Protocol RFC951 Overview The DHCP protocol is connectionless and implemented via UDP. These two...
passivedns A tool to collect DNS records passively to aid Incident handling, Network Security Monitoring (NSM) and general digital forensics. PassiveDNS sniffs traffic from an interface or reads a pcap-file and outputs the DNS-server...
Whonow DNS Server A malicious DNS server for executing DNS Rebinding attacks on the fly. whonow lets you specify DNS responses and rebind rules dynamically using domain requests themselves. What’s great about dynamic DNS Rebinding rules is that you...
pythem – Penetration Testing Framework pythem is a multi-purpose pentest framework written in Python. It has been developed to be used by security researchers and security professionals. Usage Examples ARP spoofing – Man-in-the-middle. ARP+DNS...
POLYMORPH Polymorph is a framework written in the Python3 programming language that allows the modification of network packets in real-time, providing maximum control to the user over the contents of the packet. This framework...
SimpleEmailSpoofer A few Python programs designed to help penetration testers with email spoofing. Email Spoofing 101 Basic Principles Email spoofing has been an issue since the earliest days of the SMTP protocol. The root...